Buff Htb Walkthrough
Htb Buff Walkthrough Spyx S Blog Simple Place For Me To Blog Buff is a really good oscp style box, where i’ll have to identify a web software running on the site, and exploit it using a public exploit to get execution through a webshell. Welcome back dear reader, this time we tackle the hackthabox buff machine that was tricky at times with a series of unexpected behaviors. i'll explain what the problem that slowed me down was, let's not waste any more time and jump right in!.
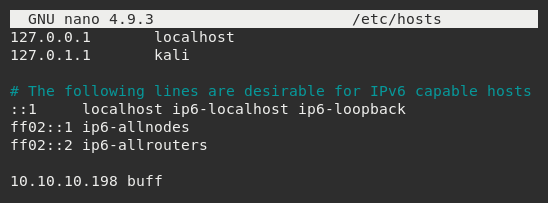
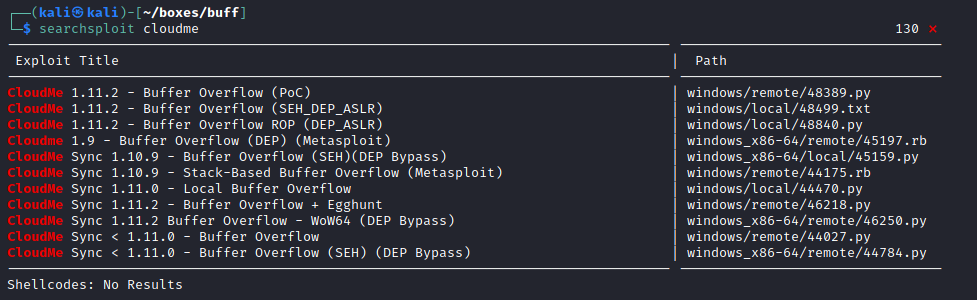
Htb Buff Write Up Walkthrough Jacob Riggs Blog These writeups will explain my steps to completion, along with the tools and techniques that i used. the machines that i have chose to complete are from the tj null spread sheet, and are. This is my first writeup about buffer overflow, and also on a windows machine, it was a very rewarding experience, so i’m going to look for another box to do with the same theme and continue learning this extraordinary vulnerability. This is my write up and walkthrough for the buff box. when commencing this engagement, buff was listed in htb (hackthebox) with an easy difficulty rating. This exploit is a python script abusing a buffer overflow vulnerability in the cloudme service. however, we saw no other open ports on our rustscan. thus, we need to find out which port this service runs on and then set up a port forward firstly, i performed a simple google search to answer the first question.
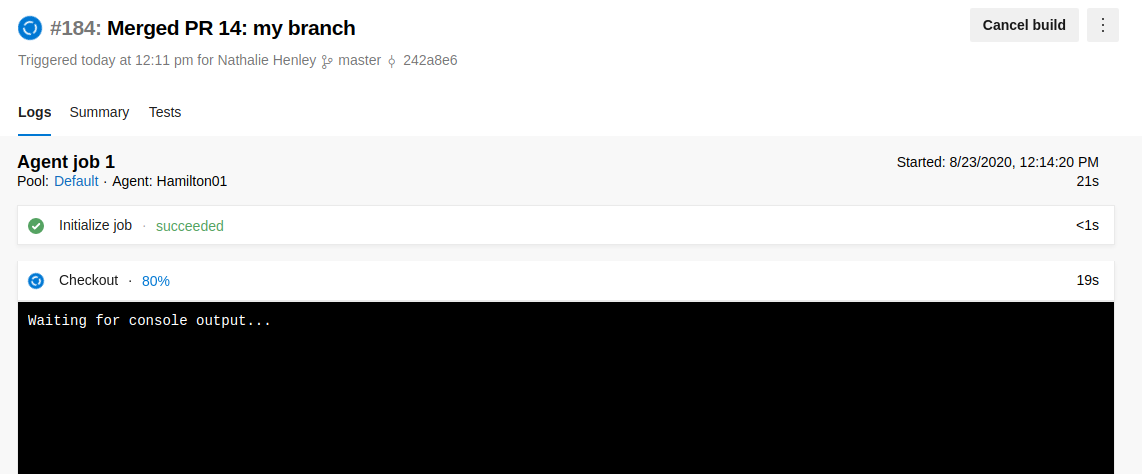
Htb Worker Walkthrough This is my write up and walkthrough for the buff box. when commencing this engagement, buff was listed in htb (hackthebox) with an easy difficulty rating. This exploit is a python script abusing a buffer overflow vulnerability in the cloudme service. however, we saw no other open ports on our rustscan. thus, we need to find out which port this service runs on and then set up a port forward firstly, i performed a simple google search to answer the first question. Buff is a windows box found on hackthebox. if you are working on the box and looking for some hints, i will tell you that this box is mainly focused on known cves. there is nothing you need to write by hand, just make sure you are enumerating and checking everything for existing exploits. A showcase of my cybersecurity journey through hack the box ctf challenges, highlighting skills in network enumeration, exploitation, and problem solving. ctf chronicles htb buff walkthrough.md at main · solaconsay ctf chronicles. In this walkthrough i have demonstrated how i exploited buff hackthebox machine with ip address 10.10.10.198 in very simple way. Today, we will be continuing with our exploration of hack the box (htb) machines, as seen in previous articles. this walkthrough is of an htb machine named buff.
Comments are closed.