Buff Hackthebox Walkthrough Infosec Blogs
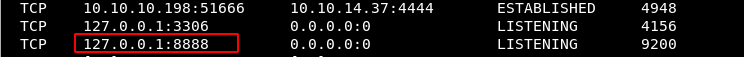
Buff Hackthebox Walkthrough Infosec Blogs Welcome back dear reader, this time we tackle the hackthabox buff machine that was tricky at times with a series of unexpected behaviors. i'll explain what the problem that slowed me down was, let's not waste any more time and jump right in!. Buff is a really good oscp style box, where i’ll have to identify a web software running on the site, and exploit it using a public exploit to get execution through a webshell.
Buff Hackthebox Walkthrough Geek Girl Today, we will be continuing with our exploration of hack the box (htb) machines, as seen in previous articles. this walkthrough is of an htb machine named buff. htb is an excellent platform that hosts machines belonging to multiple oses. it also has some other challenges as well. These writeups will explain my steps to completion, along with the tools and techniques that i used. the machines that i have chose to complete are from the tj null spread sheet, and are. Buff is a quite easy box highlighting basics of enumeration, where we discover a website running a vulnerable software and exploit it using a publicly available exploit to a get remote code execution on the box. This is my write up and walkthrough for the buff box. when commencing this engagement, buff was listed in htb (hackthebox) with an easy difficulty rating.

Buff Hackthebox Walkthrough Geek Girl Buff is a quite easy box highlighting basics of enumeration, where we discover a website running a vulnerable software and exploit it using a publicly available exploit to a get remote code execution on the box. This is my write up and walkthrough for the buff box. when commencing this engagement, buff was listed in htb (hackthebox) with an easy difficulty rating. Awesome write ups from the world's best hackers intopics ranging from bug bounties, ctfs, hack the box walkthroughs, hardware challenges, and real life encounters. This was an easy windows machine that involved exploiting an unauthenticated remote code execution vulnerability through file upload bypass affecting gym management system to gain initial access and a buffer overflow vulnerability in the cloudme software to escalate privileges to administrator. Hackthebox | buff walkthrough | htb we are starting a daily series in which we are going to cover writeups of 37 hack the box boxes of the tjnull list for oscp preparation. 37 days of hack the box …. This is shreya and today i am gonna show you how to pwn buff from hackthebox. buff is an easy level windows machine having a straightforward way to obtain initial foothold.

Buff Hackthebox Walkthrough Geek Girl Awesome write ups from the world's best hackers intopics ranging from bug bounties, ctfs, hack the box walkthroughs, hardware challenges, and real life encounters. This was an easy windows machine that involved exploiting an unauthenticated remote code execution vulnerability through file upload bypass affecting gym management system to gain initial access and a buffer overflow vulnerability in the cloudme software to escalate privileges to administrator. Hackthebox | buff walkthrough | htb we are starting a daily series in which we are going to cover writeups of 37 hack the box boxes of the tjnull list for oscp preparation. 37 days of hack the box …. This is shreya and today i am gonna show you how to pwn buff from hackthebox. buff is an easy level windows machine having a straightforward way to obtain initial foothold.
Buff Hackthebox Walkthrough Geek Girl Hackthebox | buff walkthrough | htb we are starting a daily series in which we are going to cover writeups of 37 hack the box boxes of the tjnull list for oscp preparation. 37 days of hack the box …. This is shreya and today i am gonna show you how to pwn buff from hackthebox. buff is an easy level windows machine having a straightforward way to obtain initial foothold.
Comments are closed.