Brute Force Attack Pdf Password User Computing
Download Brute Force Attack Password Cracking Fileebook Brute force attack is a method that is used by hackers to get access to unauthorized information by trying every possible combination and pattern of passwords or encryption keys until they find the correct password or encryption key. Brute force attacks remain a critical threat to login security, leveraging repeated attempts to guess valid credentials. this project presents a secure login system designed to counter such.
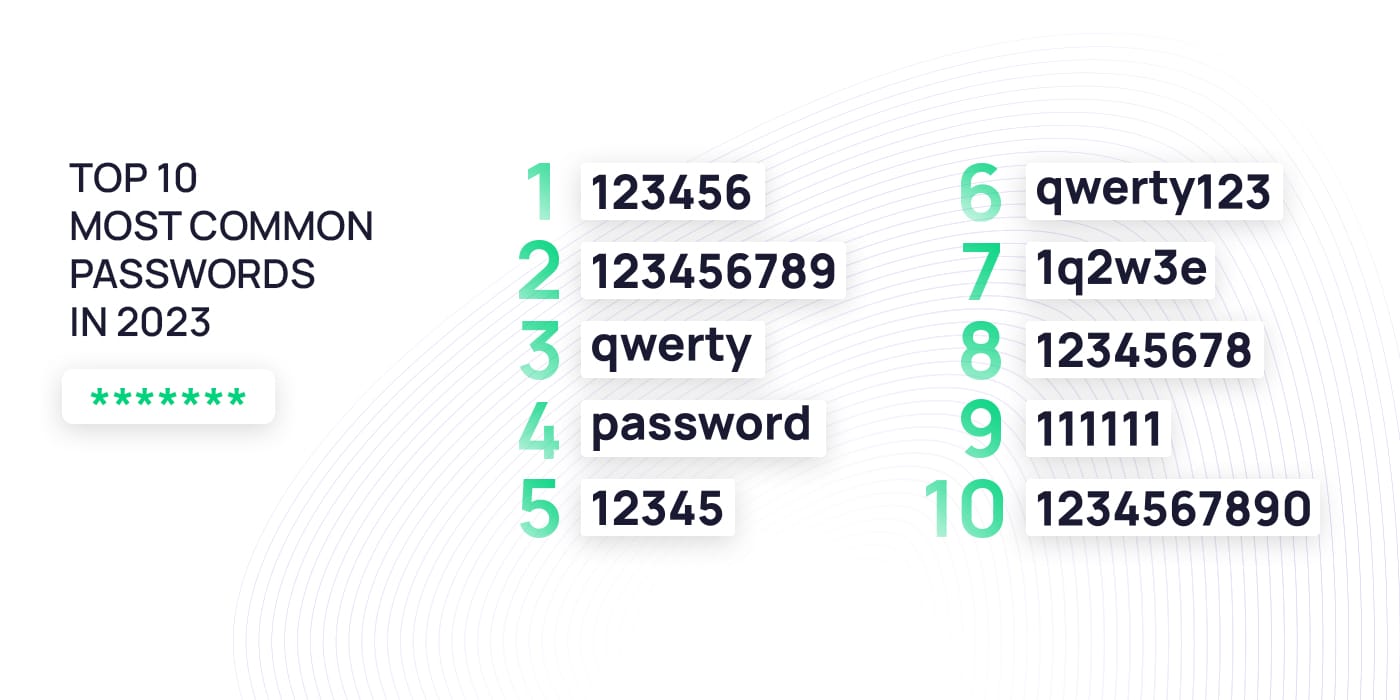
What Are Brute Force Attacks Examples Prevention Tips A brute force attack is a hacking method that uses trial and error to crack passwords, login credentials, and encryption keys. it is a simple yet efficient method for gaining unwanted access to networks, enterprise systems, and user accounts. A brute force attack is the simplest method to gain access to a site or server (or anything that is password protected). it tries various combinations of usernames and passwords until it gets in. Let’s assume that a user creates a completely random password, rejecting the possibility of using a brute force dictionary attack. here is a critical analysis of the potential enforcement of various security policy requirements:. Additionally, large scale data breaches have exposed millions of user credentials, which attackers reuse to launch credential stuffing and dictionary attacks.this paper focuses on analyzing two major password attack techniques: brute force attacks and dictionary attacks.

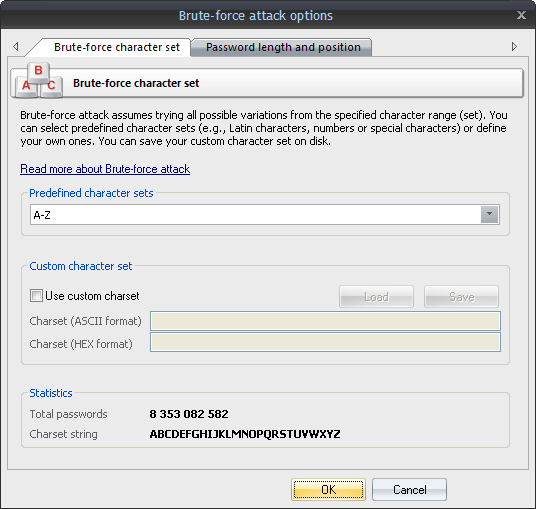
What Are Brute Force Attacks Examples Prevention Tips Let’s assume that a user creates a completely random password, rejecting the possibility of using a brute force dictionary attack. here is a critical analysis of the potential enforcement of various security policy requirements:. Additionally, large scale data breaches have exposed millions of user credentials, which attackers reuse to launch credential stuffing and dictionary attacks.this paper focuses on analyzing two major password attack techniques: brute force attacks and dictionary attacks. The document discusses brute force attacks and methods to prevent them. it describes how brute force attacks work by automatically trying all possible login combinations. Brute force: a brute force technique is an attempt to crack passwords using permutation and combination approach. this method takes a lot of time and memory consumption depending on the length and complexity of password. Pdfrip is a multithreaded pdf password cracking utility written in rust with support for wordlist attacks, bounded masks, contains word workflows, date and number generators, printable ascii brute forcing, checkpoint resume, and structured json output. Since kdf is a function, the only way to recover the text password from the hash password will be a brute force attack . it is important to use the same trick in password recovery because it saves time and prevents data and information from forgetting the password.
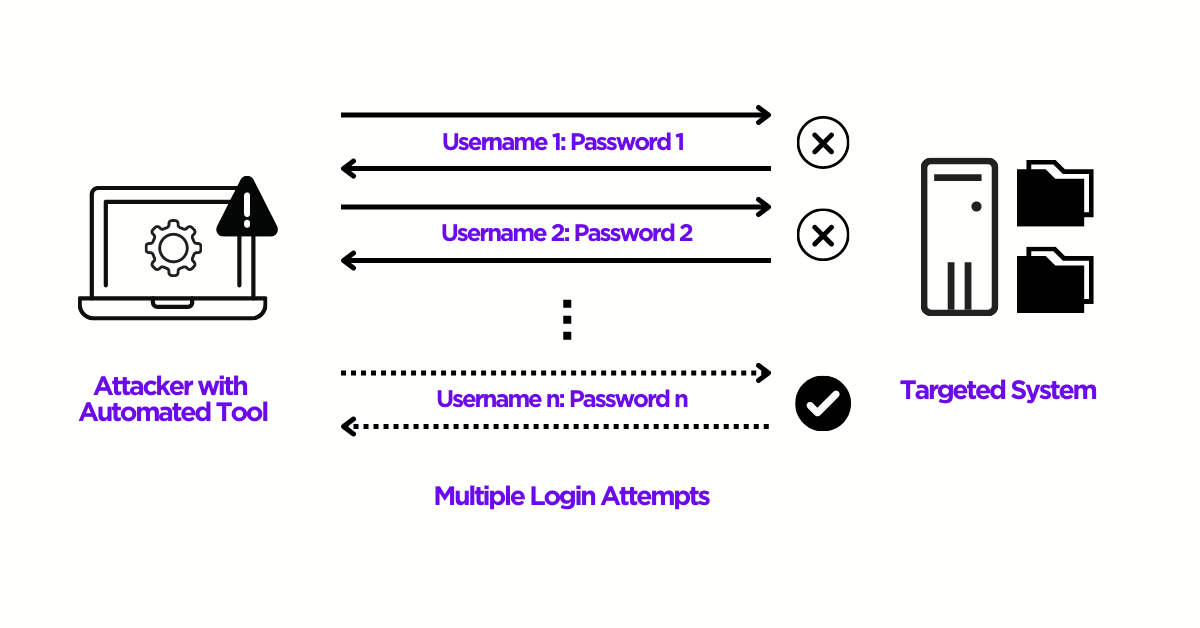
Detecting Brute Force Password Attacks The document discusses brute force attacks and methods to prevent them. it describes how brute force attacks work by automatically trying all possible login combinations. Brute force: a brute force technique is an attempt to crack passwords using permutation and combination approach. this method takes a lot of time and memory consumption depending on the length and complexity of password. Pdfrip is a multithreaded pdf password cracking utility written in rust with support for wordlist attacks, bounded masks, contains word workflows, date and number generators, printable ascii brute forcing, checkpoint resume, and structured json output. Since kdf is a function, the only way to recover the text password from the hash password will be a brute force attack . it is important to use the same trick in password recovery because it saves time and prevents data and information from forgetting the password.

No Password Is Strong Enough Learn About Brute Force Attacks Pdfrip is a multithreaded pdf password cracking utility written in rust with support for wordlist attacks, bounded masks, contains word workflows, date and number generators, printable ascii brute forcing, checkpoint resume, and structured json output. Since kdf is a function, the only way to recover the text password from the hash password will be a brute force attack . it is important to use the same trick in password recovery because it saves time and prevents data and information from forgetting the password.
Brute Force Password Attacks Defined
Comments are closed.