Broken Access Control Pdf

A Comprehensive Guide To Broken Access Control Purplebox Security This comprehensive write up explores broken access control in depth, covering its root causes, real world exploitation techniques, detection methodologies, and mitigation strategies. Broken access control (bac), ranked as 5th crucial vulnerability in open web application security project (owasp), appear to be critical in web applications because of its adverse consequence.

Broken Access Control Description Pdf Internet Web Web Server Techniques. what is broken access control? access control issues enable unauthorized users to access, modify and delete resources. or perform actions beyond the permissions. broken access control encompasses various security vulnerabilities typic. In this survey, we provides a structured overview on the existing approaches on preventing and detecting access control vulnerabili ties in web applications in diferent phase of development cycles. Contribute to sblrm cybersecurity portfolio development by creating an account on github. This review provides a comprehensive analysis of the root causes and technical mechanisms behind broken access control vul nerabilities, categorizing their common forms and implications.

Detection Of Broken Access Control Vulnerability Using Graph Contribute to sblrm cybersecurity portfolio development by creating an account on github. This review provides a comprehensive analysis of the root causes and technical mechanisms behind broken access control vul nerabilities, categorizing their common forms and implications. Broken access control access or modify information beyond limits. access or modify user info without logging in. access or modify info that belongs to another user. It provides examples of broken access control, such as unverified data usage and forced browsing, and suggests measures for securing applications, including thorough testing of access control mechanisms. the document concludes with an invitation for questions and clarifications from participants. Broken access control free download as pdf file (.pdf), text file (.txt) or read online for free. broken access control is a security vulnerability that allows unauthorized users to access restricted data and functionalities due to weak implementation of access controls. Broken access control vulnerabilities pose significant risks across various web applications. the paper surveys detection and prevention methods for broken access control vulnerabilities, highlighting research gaps. current research categorizes countermeasures into prevention, detection, and exploitation prevention strategies.
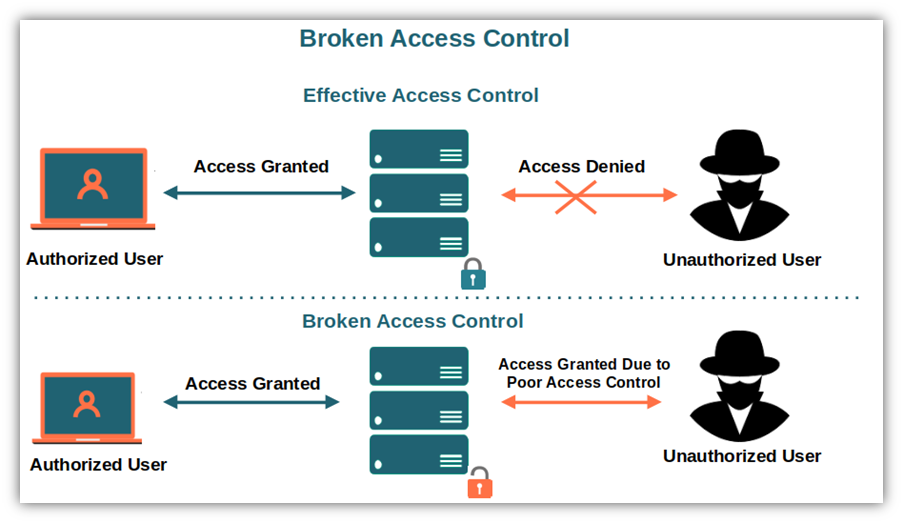
What Are The Owasp Top 10 Vulnerabilities And How To Mitigate Them Broken access control access or modify information beyond limits. access or modify user info without logging in. access or modify info that belongs to another user. It provides examples of broken access control, such as unverified data usage and forced browsing, and suggests measures for securing applications, including thorough testing of access control mechanisms. the document concludes with an invitation for questions and clarifications from participants. Broken access control free download as pdf file (.pdf), text file (.txt) or read online for free. broken access control is a security vulnerability that allows unauthorized users to access restricted data and functionalities due to weak implementation of access controls. Broken access control vulnerabilities pose significant risks across various web applications. the paper surveys detection and prevention methods for broken access control vulnerabilities, highlighting research gaps. current research categorizes countermeasures into prevention, detection, and exploitation prevention strategies.
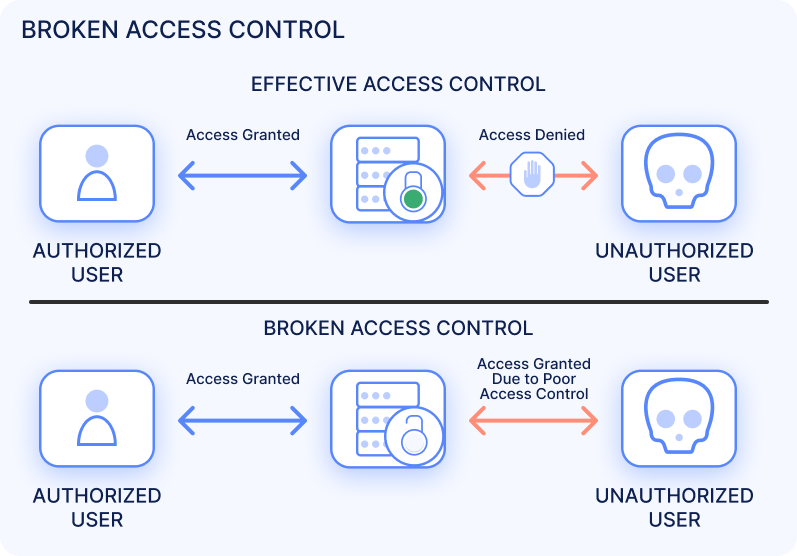
Owasp Top 10 Broken Access Control Ionix Broken access control free download as pdf file (.pdf), text file (.txt) or read online for free. broken access control is a security vulnerability that allows unauthorized users to access restricted data and functionalities due to weak implementation of access controls. Broken access control vulnerabilities pose significant risks across various web applications. the paper surveys detection and prevention methods for broken access control vulnerabilities, highlighting research gaps. current research categorizes countermeasures into prevention, detection, and exploitation prevention strategies.

Broken Access Control Idor Explained Pdf
Comments are closed.