Broken Access Control Idor Explained Pdf
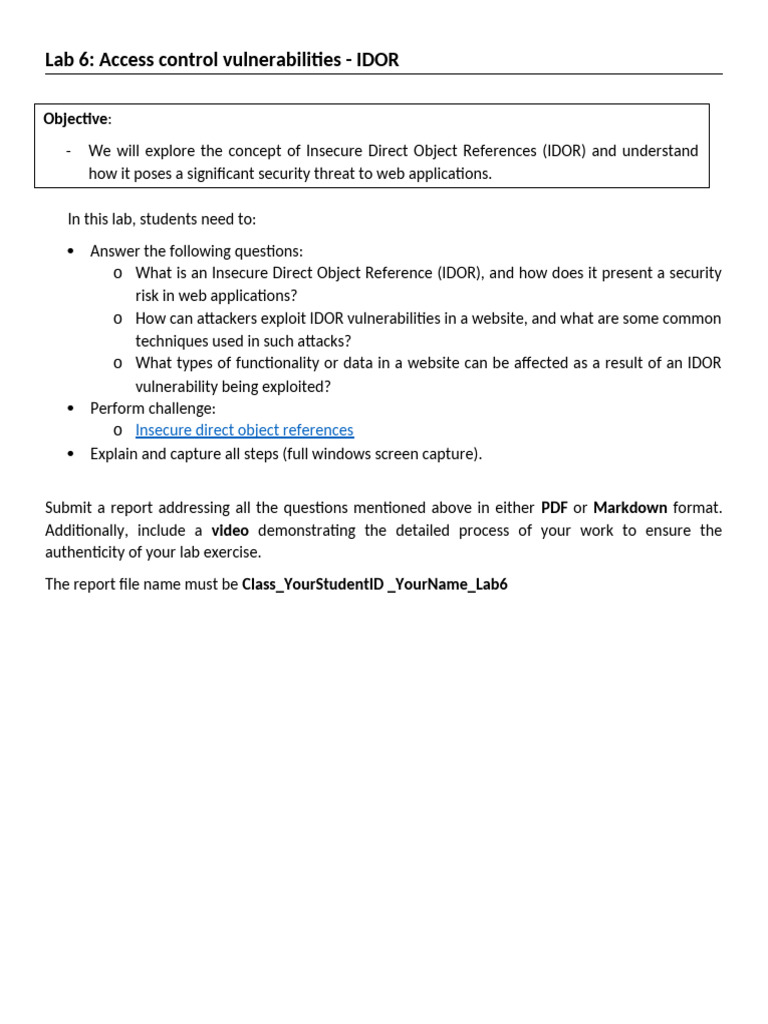
Lab6 Access Control Vulnerabilities Idor Pdf Broken access control & idor explained the document discusses broken access control vulnerabilities, specifically highlighting the risks of accessing or modifying user information without proper authentication. This comprehensive write up explores broken access control in depth, covering its root causes, real world exploitation techniques, detection methodologies, and mitigation strategies.

Broken Access Control Examples Pdf Investment in installing the application yourself to map out any roles and functions you do not have access to on the client’s hosted site can yield tremendous results. Broken access control is the #1 owasp risk. learn how idor attacks work, horizontal vs vertical escalation, and how to implement ownership checks that actually hold. Idor insecure direct object reference. objects are accessed directly based on user input. Idor vulnerabilities are access control vulnerabilities enabling malicious actors to modify or delete data or access sensitive data by issuing requests to a website or a web application programming interface (api) specifying the user identifier of other, valid users.
19 Broken Access Control Idor insecure direct object reference. objects are accessed directly based on user input. Idor vulnerabilities are access control vulnerabilities enabling malicious actors to modify or delete data or access sensitive data by issuing requests to a website or a web application programming interface (api) specifying the user identifier of other, valid users. This review provides a comprehensive analysis of the root causes and technical mechanisms behind broken access control vul nerabilities, categorizing their common forms and implications. Insecure direct object references (idor) are a type of access control vulnerability that arises when an application uses user supplied input to access objects directly. Insecure direct object reference (idor) is a vulnerability that arises when attackers can access or modify objects by manipulating identifiers used in a web application's urls or parameters. Idor stands for insecure direct object reference and it occurs when an application exposes a reference to an internal object such as a user, order, invoice, file, or transaction without properly.
Comments are closed.