Bountyhunter Hackthebox Walkthrough

Bountyhunter Hackthebox Walkthrough Ethicalhacs This walkthrough will be slightly different to my others. whereas most of my writeups are blind exploration, for this box i am using guided mode. this is because it better reflects my upcoming. Bounty hunter is a ctf linux machine with an easy difficulty rating on the hack the box platform. so let’s get started and take a deep dive into disassembling this machine utilizing the methods outlined below.

Bountyhunter Hackthebox Walkthrough Ethicalhacs Bountyhunter is a very simple linux machine designed for beginners. in this walk through we will be going understand how to gain user and root access of a machine. In this walkthrough i have demonstrated step by step how i rooted to bountyhunter hackthebox machine. hope you will learn something new. All activities demonstrated in this video were conducted on legally authorized systems such as hackthebox & tryhackme. The series will primarily consist of walkthroughs for the skill assessments in hackthebox’s bug bounty hunter path modules.
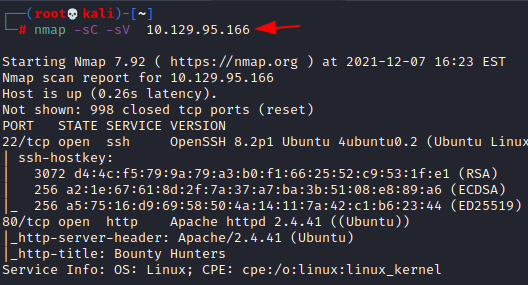
Bounty Hunter Hackthebox Walkthrough All activities demonstrated in this video were conducted on legally authorized systems such as hackthebox & tryhackme. The series will primarily consist of walkthroughs for the skill assessments in hackthebox’s bug bounty hunter path modules. In this hack the box writeup, we will walk through the process of hacking into the bounty hunter machine. this machine requires a mix of web application exploitation and privilege escalation techniques. A walkthrough write up of the "bountyhunter" box following the crest pentesting pathway feautring xml injection, code analysis, and web vulnerability assessment. Bountyhunter is a retired box available on hack the box. it offers a fun challenge when it comes to exploiting an xxe vulnerability and crafting a custom exploit for privilege escalation. Bountyhunter is rated as an easy machine on hackthebox. although it’s clear not all easy machines are created equal! we scan the box to find just two open ports, 22 and 80. a look at the website running on port 80 finds a bug bounty reporting system that is in development.
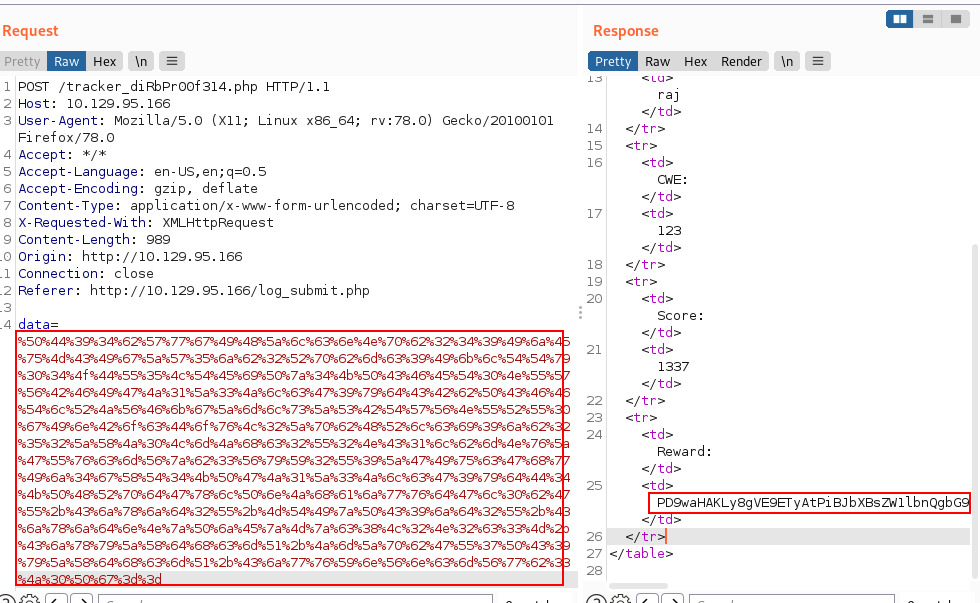
Bounty Hunter Hackthebox Walkthrough In this hack the box writeup, we will walk through the process of hacking into the bounty hunter machine. this machine requires a mix of web application exploitation and privilege escalation techniques. A walkthrough write up of the "bountyhunter" box following the crest pentesting pathway feautring xml injection, code analysis, and web vulnerability assessment. Bountyhunter is a retired box available on hack the box. it offers a fun challenge when it comes to exploiting an xxe vulnerability and crafting a custom exploit for privilege escalation. Bountyhunter is rated as an easy machine on hackthebox. although it’s clear not all easy machines are created equal! we scan the box to find just two open ports, 22 and 80. a look at the website running on port 80 finds a bug bounty reporting system that is in development.
Comments are closed.