Bounty Hunter Hackthebox Walkthrough

Hackthebox Bucket Walkthrough Pdf Cyberspace Computer Data Bounty hunter is a ctf linux machine with an easy difficulty rating on the hack the box platform. so let’s get started and take a deep dive into disassembling this machine utilizing the methods outlined below. This walkthrough will be slightly different to my others. whereas most of my writeups are blind exploration, for this box i am using guided mode. this is because it better reflects my upcoming.

Beginner Tips To Own Boxes At Hackthebox Bug Bounty Hunting The series will primarily consist of walkthroughs for the skill assessments in hackthebox’s bug bounty hunter path modules. Bountyhunter walkthrough: hackthebox writeup bountyhunter is a very simple linux machine designed for beginners. in this walk through we will be going understand how to gain user and root access of a …. Contribute to sn130hk hacker walkthrough development by creating an account on github. Bountyhunter is rated as an easy machine on hackthebox. although it’s clear not all easy machines are created equal! we scan the box to find just two open ports, 22 and 80. a look at the website running on port 80 finds a bug bounty reporting system that is in development.

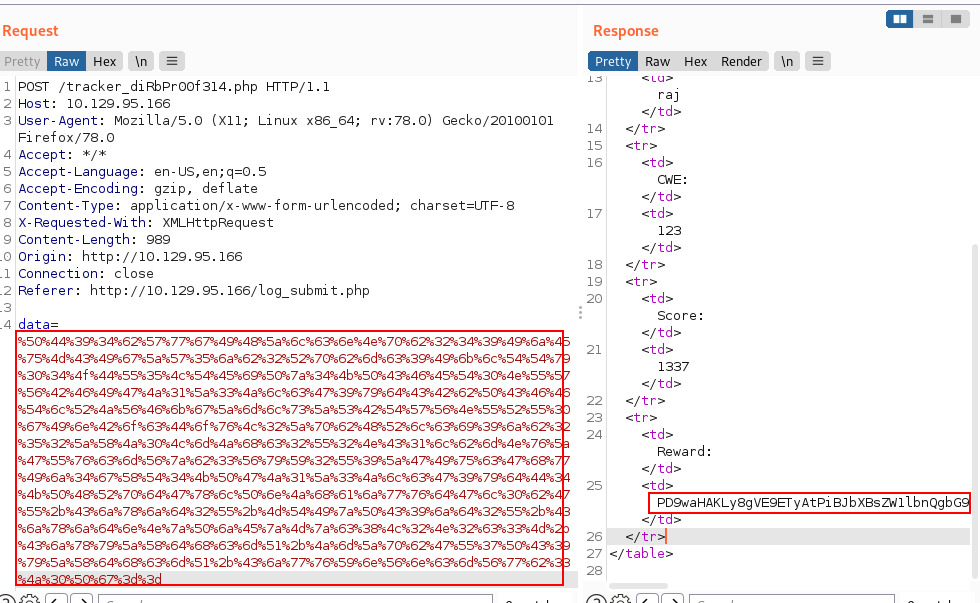
Bountyhunter Hackthebox Walkthrough Ethicalhacs Contribute to sn130hk hacker walkthrough development by creating an account on github. Bountyhunter is rated as an easy machine on hackthebox. although it’s clear not all easy machines are created equal! we scan the box to find just two open ports, 22 and 80. a look at the website running on port 80 finds a bug bounty reporting system that is in development. T his is a walkthrough writeup on bountyhunter which is a linux box categorized as easy on hackthebox. the initial foothold was gained by discovering and exploiting xxe vulnerability, meanwhile the privilege escalation part was interesting and required us to do some basic code analysis. In this walkthrough i have demonstrated step by step how i rooted to bountyhunter hackthebox machine. hope you will learn something new. Bounty hunter walkthrough: a step by step penetration testing journey just finished a deep dive report on the bounty hunter machine from hackthebox, a great controlled environment to. Bountyhunter is a “vulnerable by design” machine created by ejedev and hosted at hackthebox.eu. in this walk through i perform the actions of an attacker. the goals are to get user level privileges on the victim machine (get the flag in home $user user.txt) and escalate privileges to root (get the flag in root root.txt). victim machine specs.
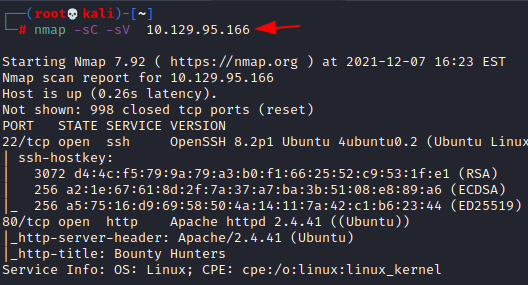
Bounty Hunter Hackthebox Walkthrough T his is a walkthrough writeup on bountyhunter which is a linux box categorized as easy on hackthebox. the initial foothold was gained by discovering and exploiting xxe vulnerability, meanwhile the privilege escalation part was interesting and required us to do some basic code analysis. In this walkthrough i have demonstrated step by step how i rooted to bountyhunter hackthebox machine. hope you will learn something new. Bounty hunter walkthrough: a step by step penetration testing journey just finished a deep dive report on the bounty hunter machine from hackthebox, a great controlled environment to. Bountyhunter is a “vulnerable by design” machine created by ejedev and hosted at hackthebox.eu. in this walk through i perform the actions of an attacker. the goals are to get user level privileges on the victim machine (get the flag in home $user user.txt) and escalate privileges to root (get the flag in root root.txt). victim machine specs.
Bounty Hunter Hackthebox Walkthrough Bounty hunter walkthrough: a step by step penetration testing journey just finished a deep dive report on the bounty hunter machine from hackthebox, a great controlled environment to. Bountyhunter is a “vulnerable by design” machine created by ejedev and hosted at hackthebox.eu. in this walk through i perform the actions of an attacker. the goals are to get user level privileges on the victim machine (get the flag in home $user user.txt) and escalate privileges to root (get the flag in root root.txt). victim machine specs.
Comments are closed.