Blockchain Development Lecture 5 Security Tokens Wallets

Lecture 5 Security Dark Pdf Cryptography Key Cryptography Blockchain development lecture 5: security, tokens, wallets blockchain at berkeley 19.5k subscribers subscribe. This section contains the lecture slides used in the course.

Lecture 2 Blockchain Pdf The course aims to equip students with the knowledge to design and demonstrate decentralized applications while understanding the real world applications and impacts of blockchain technology. Topic: security, tokens, wallets instructor: janice ng, minxing chen video edited by simon zirui guo lecture slides: drive.google a berkeley.e. Session 5 free download as pdf file (.pdf), text file (.txt) or read online for free. Unit i nd this technology is described as the most disruptive technology of the decade. thus, blockchain is used for the secure transference of items like money, contracts, property rights, stocks, and even networks wi hout any requirement of third party intermediaries like governments, banks, etc. once the data is.

Security Tokens In Crypto Common Types And Advantages Session 5 free download as pdf file (.pdf), text file (.txt) or read online for free. Unit i nd this technology is described as the most disruptive technology of the decade. thus, blockchain is used for the secure transference of items like money, contracts, property rights, stocks, and even networks wi hout any requirement of third party intermediaries like governments, banks, etc. once the data is. Whether you are a beginner or an experienced developer, this course will guide you through the entire process of creating decentralized applications (dapps) and interacting with smart contracts using web3 libraries. In this finn das explainer, we're going to dive right into the cortex that powers the entire crypto economic world. we'll cover the basic architecture, the rules that govern it, the security that. Cs 251: blockchain technologies fall 2025 course syllabus and readings every lecture is accompanied by readings that support and expand what was covered in the lecture. What is a blockchain? abstract answer: a blockchain provides coordination between many parties, when there is no single trusted party if trusted party exists ⇒ no need for a blockchain [financial systems: often no trusted party].
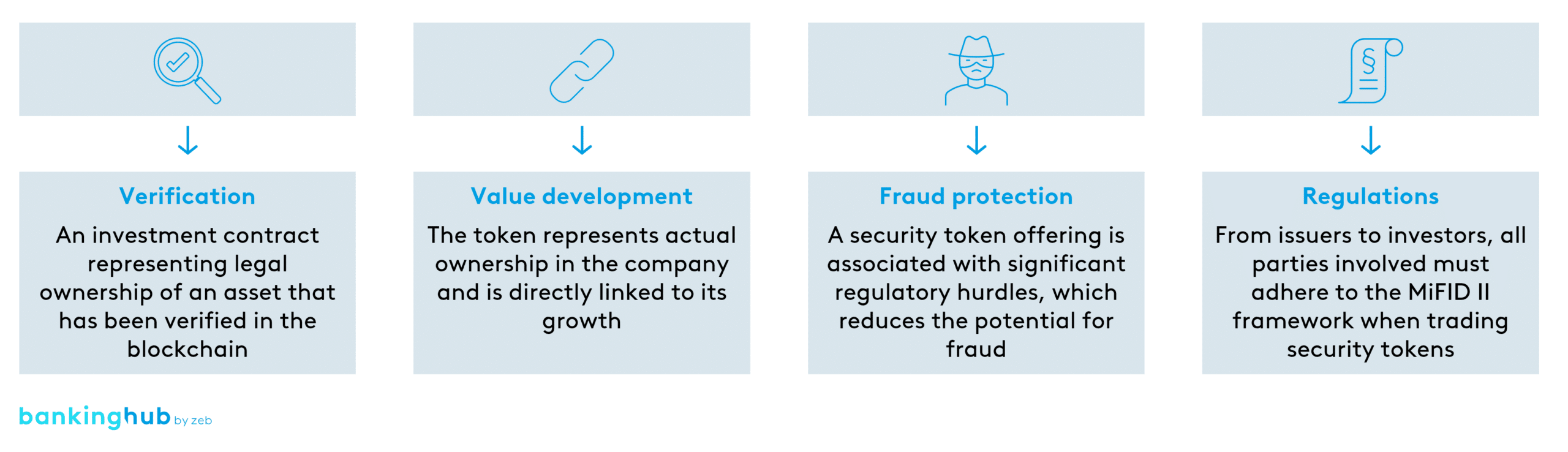
Security Tokens Bankinghub Whether you are a beginner or an experienced developer, this course will guide you through the entire process of creating decentralized applications (dapps) and interacting with smart contracts using web3 libraries. In this finn das explainer, we're going to dive right into the cortex that powers the entire crypto economic world. we'll cover the basic architecture, the rules that govern it, the security that. Cs 251: blockchain technologies fall 2025 course syllabus and readings every lecture is accompanied by readings that support and expand what was covered in the lecture. What is a blockchain? abstract answer: a blockchain provides coordination between many parties, when there is no single trusted party if trusted party exists ⇒ no need for a blockchain [financial systems: often no trusted party].

How Security Tokens Can Be Created In Blockchain Bitdeal Cs 251: blockchain technologies fall 2025 course syllabus and readings every lecture is accompanied by readings that support and expand what was covered in the lecture. What is a blockchain? abstract answer: a blockchain provides coordination between many parties, when there is no single trusted party if trusted party exists ⇒ no need for a blockchain [financial systems: often no trusted party].
Comments are closed.