Blackshades Ransomware Authors Leave Digital Crumbs Behind
Blackshades Ransomware Authors Leave Digital Crumbs Behind I recently analyzed a new ransomware, called blackshades, which left me scratching my head, as to why the author was leaving digital evidence of who they actually are…. • check ransomware clues folder (c:\programdata\blackshades\rsa32 stat.log) – if you see a uuid between square brackets below, you may be eligible for a decryption service run by swiss authorities (“tinba sommer project”).
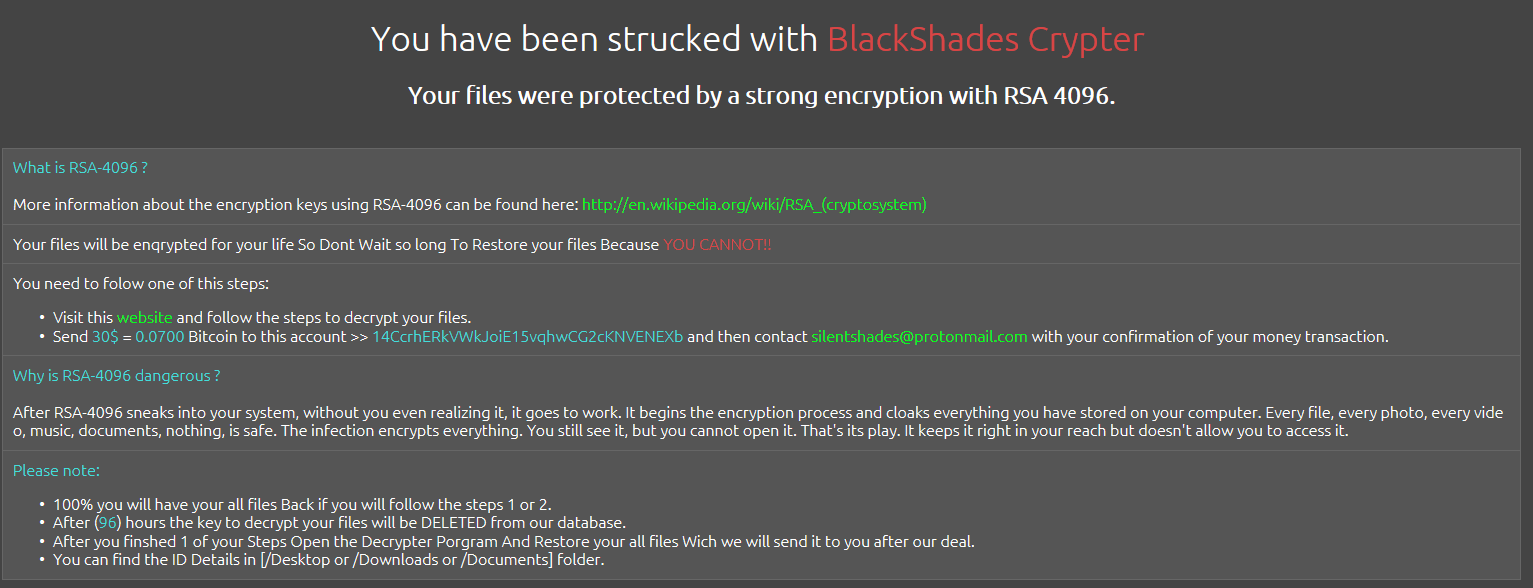
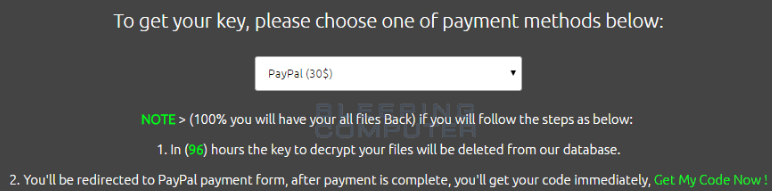
Blackshades Ransomware Authors Leave Digital Crumbs Behind Blackshades can also act as ransomware. hackers using blackshades can restrict access to the victim's computer and demand a ransom paid to the hacker in order for the restriction to be lifted. Screenshot of a message encouraging users to contact the developers of black shades ransomware (silentshade@protonmail ) to decrypt their compromised data: black shades ransomware is very similar to cerber, locky, bloccato, and dozens of other viruses. Blackshades is a remote access trojan (rat) malware designed to grant unauthorized remote control over infected computers, allowing operators to activate webcams and microphones for surveillance, steal files and credentials, and execute other invasive actions. Explore the latest news, real world incidents, expert analysis, and trends in blackshades rat — only on the hacker news, the leading cybersecurity and it news platform.
Blackshades Ransomware Authors Leave Digital Crumbs Behind Blackshades is a remote access trojan (rat) malware designed to grant unauthorized remote control over infected computers, allowing operators to activate webcams and microphones for surveillance, steal files and credentials, and execute other invasive actions. Explore the latest news, real world incidents, expert analysis, and trends in blackshades rat — only on the hacker news, the leading cybersecurity and it news platform. A collaborative operation by international law enforcement agencies nabbed authors, staff members, and users of the popular software used for everything from blackmail to financial fraud. Since at least 2010, an organization known as “blackshades” has sold and distributed malicious software to thousands of cybercriminals throughout the world. Almost 100 alleged hackers, including 17 from the uk, have been arrested around the world for distributing and using the blackshades remote access trojan (rat). "armed with $40 and a computer, an individual could easily get the blackshades remote access tool and become a perpetrator," said george venizelos, assistant director at the fbi, in a statement.
Blackshades Ransomware Authors Leave Digital Crumbs Behind A collaborative operation by international law enforcement agencies nabbed authors, staff members, and users of the popular software used for everything from blackmail to financial fraud. Since at least 2010, an organization known as “blackshades” has sold and distributed malicious software to thousands of cybercriminals throughout the world. Almost 100 alleged hackers, including 17 from the uk, have been arrested around the world for distributing and using the blackshades remote access trojan (rat). "armed with $40 and a computer, an individual could easily get the blackshades remote access tool and become a perpetrator," said george venizelos, assistant director at the fbi, in a statement.
Comments are closed.