Blackshades Hackingbharara Computer Camera Access

Blackshades Arrests In Computer Malware Probe Bbc News In november 2013, abrahams pleaded guilty to hacking over 100 150 women and installing the highly invasive malware blackshades on their computers in order to obtain nude images and videos of them. The rat was co created by yucel and has been used to infect computers throughout the world to spy on victims through their web cameras, steal files and account information, and log victims' key strokes.

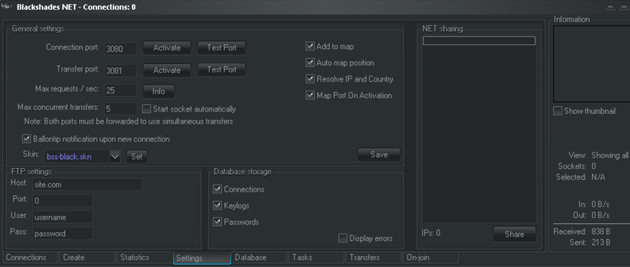
Webcam Hacker Spied On Sex Acts With Blackshades Malware Bbc News The homes of hackers in australia, canada, asia and europe have been raided and computers seized as authorities worldwide crackdown on users of malware called blackshades. Marlen rappa, a customer of blackshades who purchased the rat and used it to infect victims’ computers, spy on those victims using their web cameras, and steal personal files from their computers, pled guilty on october 31, 2014, before u.s. district judge valerie e. caproni. Contribute to malwares remote access trojan development by creating an account on github. Blackshades is a remote access trojan (rat) malware designed to grant unauthorized remote control over infected computers, allowing operators to activate webcams and microphones for surveillance, steal files and credentials, and execute other invasive actions.

The Tech Flaw That Lets Hackers Control Surveillance Cameras Bbc News Contribute to malwares remote access trojan development by creating an account on github. Blackshades is a remote access trojan (rat) malware designed to grant unauthorized remote control over infected computers, allowing operators to activate webcams and microphones for surveillance, steal files and credentials, and execute other invasive actions. The federal bureau of investigation recently busted about 100 novice and pro cyber criminals alike for using a malware dubbed blackshades which was used to gain remote access to computer sets of victims who were unaware that they were being watched through their own webcam. Webcam activation: one of the most troubling features of blackshades is its ability to access a computer’s webcam covertly. the hacker can activate the webcam at will, capturing images and videos of the victim in their most vulnerable moments. In some cases, users employed the inexpensive software, known as blackshades' remote access tool or rat, to take over the computers' cameras and spy on their owners, u.s. officials said at. Hackers who paid $40 for a sinister software program called blackshades stole sexually explicit photographs from personal computers, trained victims’ webcams on them using a remote access.

Feds Charge Alleged Blackshades Hackers The federal bureau of investigation recently busted about 100 novice and pro cyber criminals alike for using a malware dubbed blackshades which was used to gain remote access to computer sets of victims who were unaware that they were being watched through their own webcam. Webcam activation: one of the most troubling features of blackshades is its ability to access a computer’s webcam covertly. the hacker can activate the webcam at will, capturing images and videos of the victim in their most vulnerable moments. In some cases, users employed the inexpensive software, known as blackshades' remote access tool or rat, to take over the computers' cameras and spy on their owners, u.s. officials said at. Hackers who paid $40 for a sinister software program called blackshades stole sexually explicit photographs from personal computers, trained victims’ webcams on them using a remote access.

5 Scary Things About The Blackshades Rat The Washington Post In some cases, users employed the inexpensive software, known as blackshades' remote access tool or rat, to take over the computers' cameras and spy on their owners, u.s. officials said at. Hackers who paid $40 for a sinister software program called blackshades stole sexually explicit photographs from personal computers, trained victims’ webcams on them using a remote access.
All About Blackshades The Malware That Lets Hackers Watch You Through
Comments are closed.