Blackhat 2013 Virtual Deobfuscator Removing Virtualization
Llvm Powered Deobfuscation Of Virtualized Binaries Virtual deobfuscator removing virtualization obfuscations from malware – a darpa cyber fast track funded effort approved for public release, distribution unlimited. Blackhat 2013 virtual deobfuscator: temoving virtualization obfuscations from malware a darpa cyber fast track funded effort.

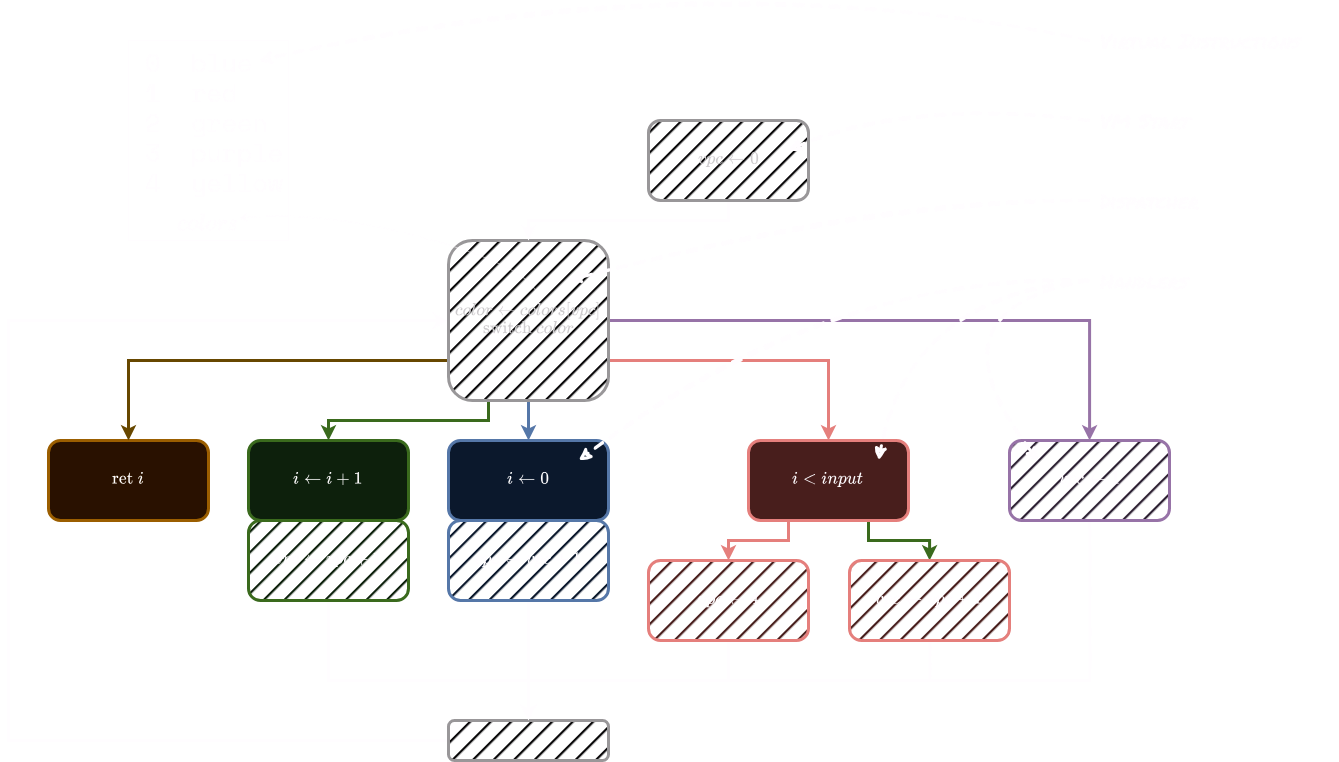
Black Hat Talk Virtual Deobfuscator A Darpa Cyber Fast Track Funded Reverse engineering tool for virtualization wrappers. the virtual deobfuscator was developed as part of the darpa cyber fast track program. the goal was to create a tool that could remove virtual machine (vm) based protections from malware. i developed a prototype version that looks very promising. The tool i created, virtual deobfuscator, will require no static man hours reversing for the bytecode location or how the vm interpreter works, and will recreate instructions nearly equivalent to the original instructions. Explore a groundbreaking approach to reverse engineering virtualization obfuscators in this black hat usa 2013 conference talk. discover the virtual deobfuscator, a darpa cyber fast track funded tool developed by jason raber. Virtual deobfuscator • developed in python • uses a run trace • filters out vm interpreters logic – risc pipeline • result: bytcode interpretation (syntax and semantics) • architecture agnostic • recursive clustering • peephole optimization 7.
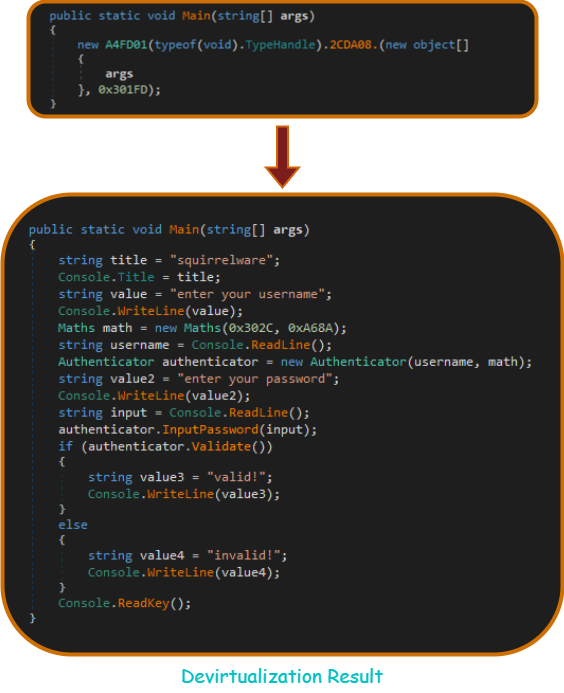
A Tale Of Net Deobfuscation Virtualguard Devirtualization Explore a groundbreaking approach to reverse engineering virtualization obfuscators in this black hat usa 2013 conference talk. discover the virtual deobfuscator, a darpa cyber fast track funded tool developed by jason raber. Virtual deobfuscator • developed in python • uses a run trace • filters out vm interpreters logic – risc pipeline • result: bytcode interpretation (syntax and semantics) • architecture agnostic • recursive clustering • peephole optimization 7. We tested the virtual deobfuscator on the malware win32.klone.af, available from the open malware library. klone uses both vm obfuscation, in the form of vmprotect, and a general protection packer, nspack. both of these protections are commercially available tools. Virtualdeobfuscator is a reverse engineering tool for virtualization wrappers. the goal of the virtual deobfuscator is to analyze a runtrace and filter out the vm processing instructions, leaving a reverse engineer with a bytecode version of the original binary. For this version, you can update csvm handlers info containing file to restore the data from virtualized part. in simpler terms, the agile system uses a special way to manage its code instructions, known as opcodes. unlike other systems, it combines several opcodes and handles them together. Published on 2014 01 15 blackhat 2013 fully arbitrary 802.3 packet injection: maximizing the ethernet attack surface published on 2014 01 15 blackhat 2013 rooting sim cards published on 2014 01 15 blackhat 2013 truncating tls connections to violate beliefs in web applications published on 2014 01 15.

A Tale Of Net Deobfuscation Virtualguard Devirtualization We tested the virtual deobfuscator on the malware win32.klone.af, available from the open malware library. klone uses both vm obfuscation, in the form of vmprotect, and a general protection packer, nspack. both of these protections are commercially available tools. Virtualdeobfuscator is a reverse engineering tool for virtualization wrappers. the goal of the virtual deobfuscator is to analyze a runtrace and filter out the vm processing instructions, leaving a reverse engineer with a bytecode version of the original binary. For this version, you can update csvm handlers info containing file to restore the data from virtualized part. in simpler terms, the agile system uses a special way to manage its code instructions, known as opcodes. unlike other systems, it combines several opcodes and handles them together. Published on 2014 01 15 blackhat 2013 fully arbitrary 802.3 packet injection: maximizing the ethernet attack surface published on 2014 01 15 blackhat 2013 rooting sim cards published on 2014 01 15 blackhat 2013 truncating tls connections to violate beliefs in web applications published on 2014 01 15.
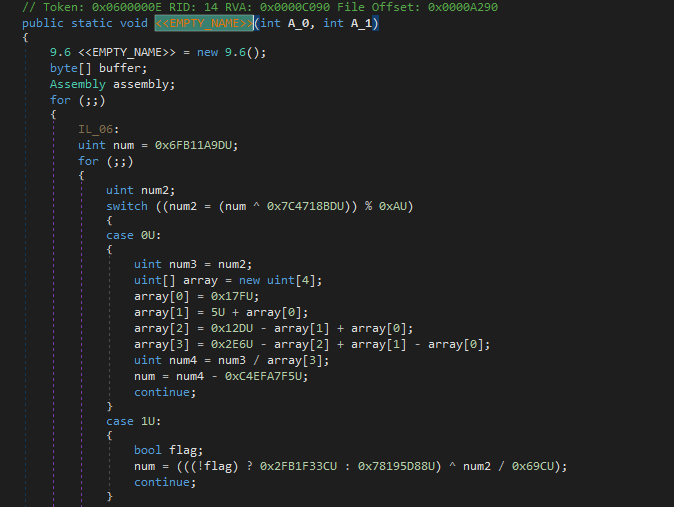
A Tale Of Net Deobfuscation Virtualguard Basics For this version, you can update csvm handlers info containing file to restore the data from virtualized part. in simpler terms, the agile system uses a special way to manage its code instructions, known as opcodes. unlike other systems, it combines several opcodes and handles them together. Published on 2014 01 15 blackhat 2013 fully arbitrary 802.3 packet injection: maximizing the ethernet attack surface published on 2014 01 15 blackhat 2013 rooting sim cards published on 2014 01 15 blackhat 2013 truncating tls connections to violate beliefs in web applications published on 2014 01 15.
Comments are closed.