Black Hat Talk Graph Convolutional Network Based Suspicious
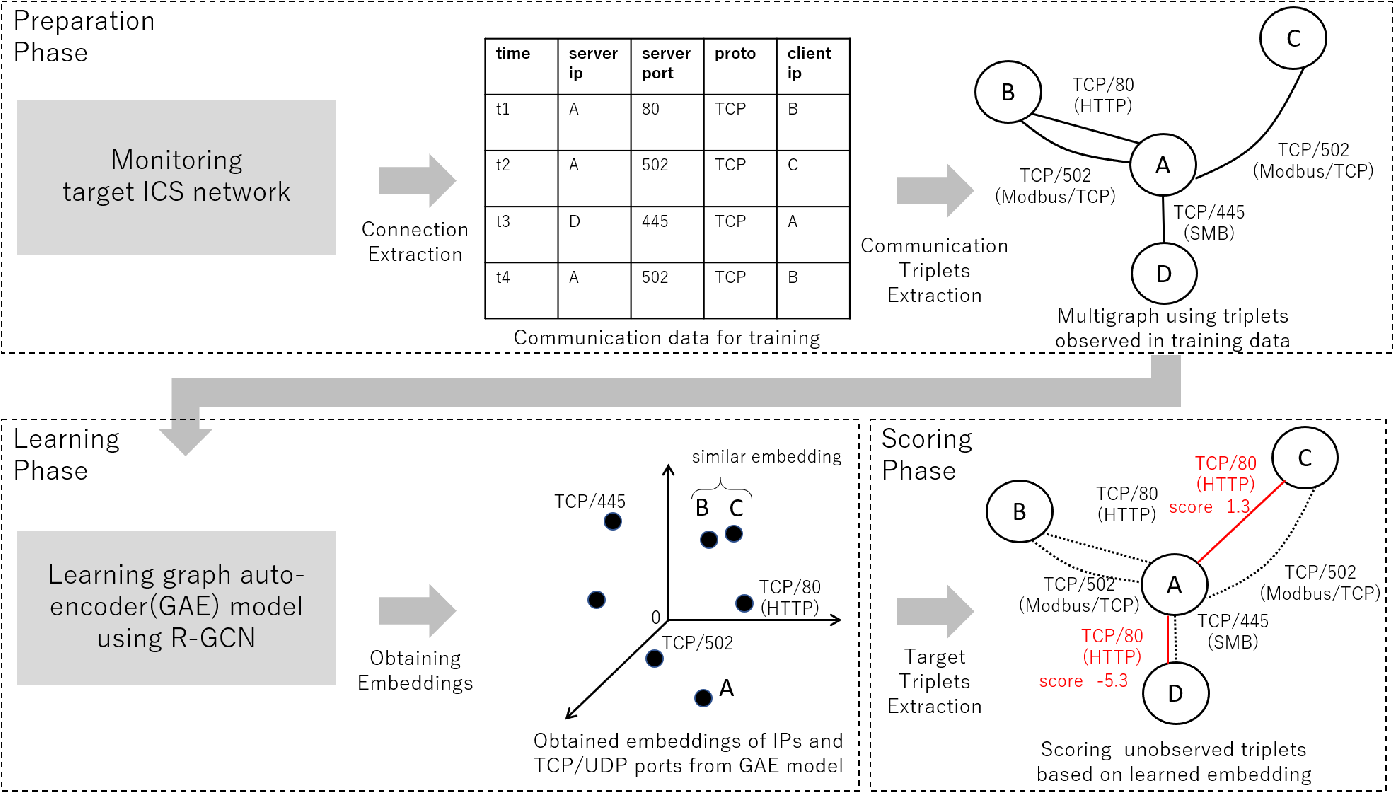
Figure 3 From Graph Convolutional Network Based Suspicious Explore graph convolutional networks for detecting suspicious communication pairs in industrial control systems, enhancing security monitoring beyond traditional whitelisting methods. Graph convolutional network based suspicious communication pair estimation for industrial control systems presented at black hat europe 2020 virtual, dec. 9, 2020, 11:20 a.m. (30 minutes).

Black Hat Talk Graph Convolutional Network Based Suspicious To solve this problem, we developed a graph convolutional network based suspicious communication pair estimation using relational graph convolution networks, and evaluated its performance. To solve this problem, we developed a graph convolutional network based suspicious communication pair estimation using relational graph convolution networks, and evaluated its. Audio and video are generally available 90 120 days after the event on the black hat channel. if a speaker is listed on the conference page, but their speech is not present, it generally means there is no available audio, video or materials. "whitelisting is considered an effective security monitoring method for networks used in industrial control systems, where the whitelists consist of observed.

Black Hat Talk Graph Based Binary Analysis From Black Hat Class Central Audio and video are generally available 90 120 days after the event on the black hat channel. if a speaker is listed on the conference page, but their speech is not present, it generally means there is no available audio, video or materials. "whitelisting is considered an effective security monitoring method for networks used in industrial control systems, where the whitelists consist of observed. This paper presented kparrts, a real time suspicious activity recognition framework that combines mediapipe based keypoint extraction with a two layer graph convolutional network (gcn) for efficient joint spatiotemporal modeling. To reduce false positives in security monitoring due to a simple whitelist based judgment, a new framework for scoring communications was developed and piloted, based on graph convolutional. Login with your gmail account keep me signed in forgot password?. Our paper was accepted to black hat europe 2020. panasonic ai website learn about our research and development in artificial intelligence and robotics technologies. our challenges in real world are now in the most exciting phase ever with ai.

Black Hat Talk Graph Based Binary Analysis From Black Hat Class Central This paper presented kparrts, a real time suspicious activity recognition framework that combines mediapipe based keypoint extraction with a two layer graph convolutional network (gcn) for efficient joint spatiotemporal modeling. To reduce false positives in security monitoring due to a simple whitelist based judgment, a new framework for scoring communications was developed and piloted, based on graph convolutional. Login with your gmail account keep me signed in forgot password?. Our paper was accepted to black hat europe 2020. panasonic ai website learn about our research and development in artificial intelligence and robotics technologies. our challenges in real world are now in the most exciting phase ever with ai.

Overview Of Spectral Based Convolutional Graph Neural Network Convgnn Login with your gmail account keep me signed in forgot password?. Our paper was accepted to black hat europe 2020. panasonic ai website learn about our research and development in artificial intelligence and robotics technologies. our challenges in real world are now in the most exciting phase ever with ai.
Graph Convolutional Neural Network Architecture And Its Applications
Comments are closed.