Black Hat Hacking Tools
Black Hat Hacking Tools Volswim Hacking tools collection with some of the best osint, recon, and offensive security tools used by the top elite hackers around the world. Whether you're into red teaming, blue teaming, application security, or osint — this curated list gives you direct access to powerful, field tested tools demonstrated live by top cybersecurity professionals at black hat events around the world.

Black Hat Hacking Tools Download Crackhaven Briefings, trainings, arsenal tool demos, and more! register here. black hat webinars are free to attend and occur monthly. learn more and register here. catch up with hours of free content from black hat events. learn more. This document provides a comprehensive introduction to the official black hat arsenal tools repository. this repository serves as a centralized collection of cybersecurity tools that have been demonstrated at black hat arsenal events since 2011. Explore the dark side of the digital world and uncover the sinister tools employed by black hat hackers. from malware to social engineering, ransomware, and defence strategies, this deep dive into the world of cyber threats sheds light on the importance of cybersecurity in the digital age. Below are ten ai tools (or tool categories) that both ethical hackers and cybercriminals leverage today—along with how each side uses them, why the tool matters, and tips to defend against its darker applications.
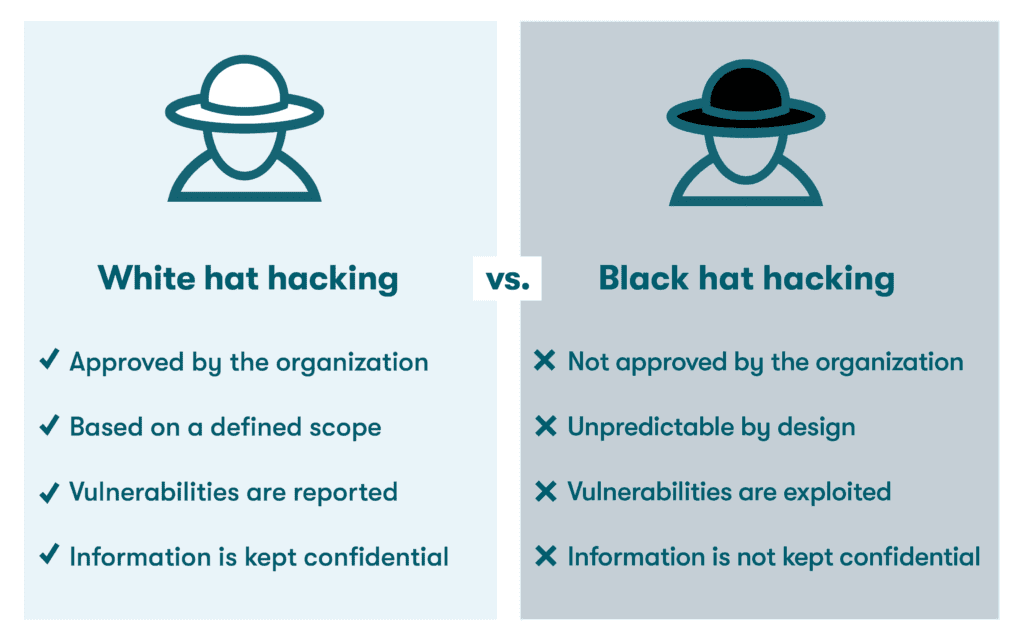
What Is Ethical Hacking Why Is It So Important For Cybersecurity Explore the dark side of the digital world and uncover the sinister tools employed by black hat hackers. from malware to social engineering, ransomware, and defence strategies, this deep dive into the world of cyber threats sheds light on the importance of cybersecurity in the digital age. Below are ten ai tools (or tool categories) that both ethical hackers and cybercriminals leverage today—along with how each side uses them, why the tool matters, and tips to defend against its darker applications. With over 2k stars on our github combined, covering recon, osint, source code review and hacking toolkits. coded by: chris ‘saintdrug’ abou‑chabké with for bheh. This repo was created containing over 48 starred tools for specific attack vectors, covering a wide range of techniques used by advanced offensive security and red teams to conduct wide range of pentesting, bug bounty hunting and more. Whether you're in red teaming, blue teaming, appsec, or osint — this list helps you explore and leverage the best tools demonstrated live by security professionals across the world. Here’s a comprehensive list of over 100 tools that can be used by both white hat and black hat hackers depending on intent. these tools cover a wide range of purposes, including network scanning, penetration testing, password cracking, web application testing, and more. network scanning and reconnaissance 1. nmap 2. zenmap 3. netcat 4. angry.
Comments are closed.