Biometric Data Person Authentication And Identification Altexsoft

Biometric Data Person Authentication And Identification Altexsoft Depending on their functions, all biometric systems can be divided into two categories — authentication and identification. let’s look at each operation case in detail and define where they can be used. In this paper, we explain biometric authentication and its use in identifying users. biometric authentication uses unique physical or behavioral characteristics, such as fingerprints,.
Biometric Data Person Authentication And Identification Altexsoft In biometric security, it’s important to distinguish between authentication, verification, and identification, as these terms are often mistakenly used interchangeably. In this paper, we present a thorough survey of privacy preserving biometric protocols, classifying them into seven distinct models based on their application scenarios. In this review, we explain in detail how the concept of authentication and the various types of biometric techniques is used for user identification. then, we discuss the various ways these techniques can be combined to create a truly multimodal authentication system. All authentication systems rely on authentication factors or pieces of evidence that prove a person is who they say they are. biometric authentication specifically uses physical and behavioral modalities to identify people.
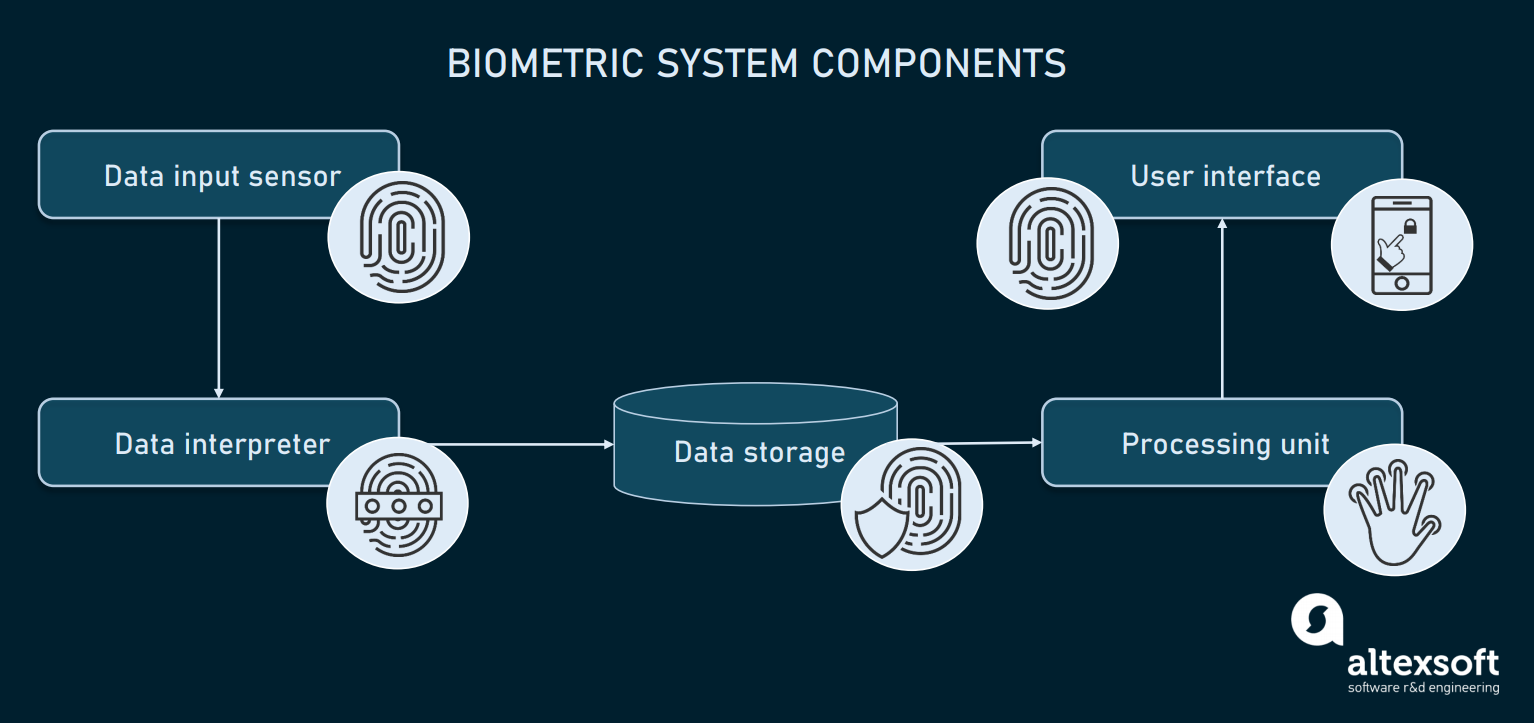
Biometric Data Person Authentication And Identification Altexsoft In this review, we explain in detail how the concept of authentication and the various types of biometric techniques is used for user identification. then, we discuss the various ways these techniques can be combined to create a truly multimodal authentication system. All authentication systems rely on authentication factors or pieces of evidence that prove a person is who they say they are. biometric authentication specifically uses physical and behavioral modalities to identify people. For authentication, there must be alternative methods of proving someone’s identity when biometric verification fails or is not possible, in order to ensure that people are not denied access to rights and services for which they are eligible and entitled. In this study, we have used iris and ecg data for authentication since they are useful in determining a person's lifelessness, while attackers can alter other biometrics like veins, palm prints, and fingerprints. Biometric verification is the process of authenticating an individual’s identity using unique physiological or behavioral characteristics, such as fingerprints, facial features, or voice patterns. in 2026, it has become a critical defense against increasingly sophisticated digital fraud. Biometric authentication is a way to safeguard your personal and sensitive information with fingerprints, iris patterns, and facial or voice recognition to confirm identity. it offers a significant advantage over easily compromised passwords.
Comments are closed.