Binary And Patch Diffing For Bug Hunting And Weaponization
Binary Diffing Haiddy The ability to compare binary code enables many real world applications on scenarios where source code may not be available such as patch analysis, bug search, and malware detection and analysis. Diffalayze is a versatile toolkit for automating patch diffing of binary targets and enriching the results with deep dive analysis from large language models (llms).
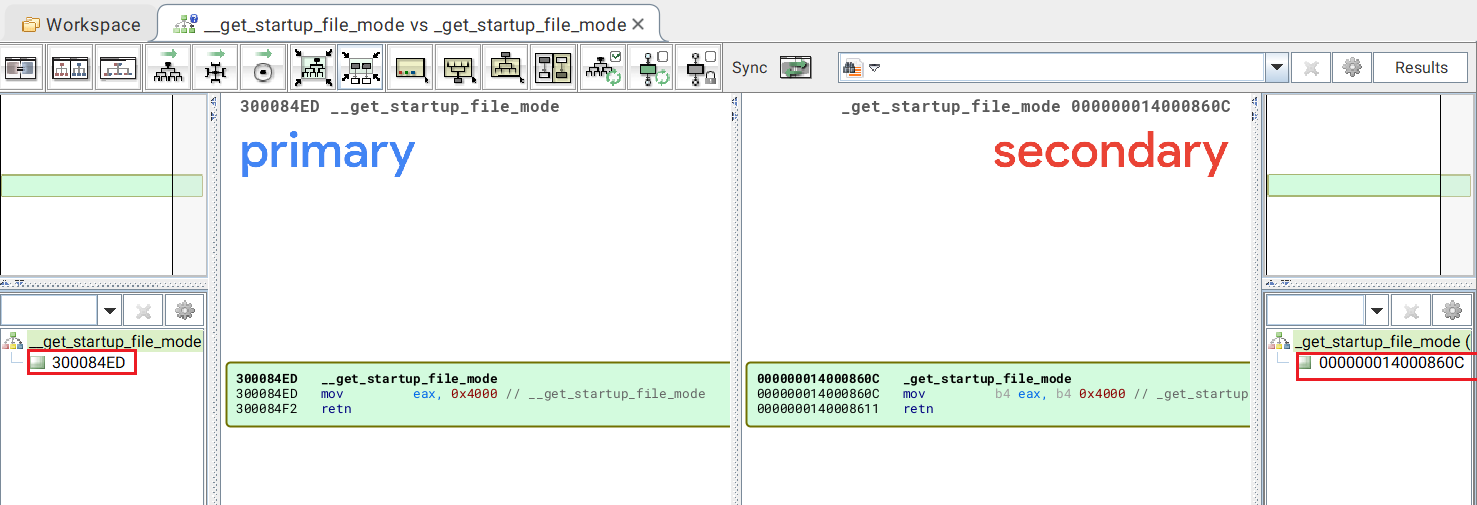
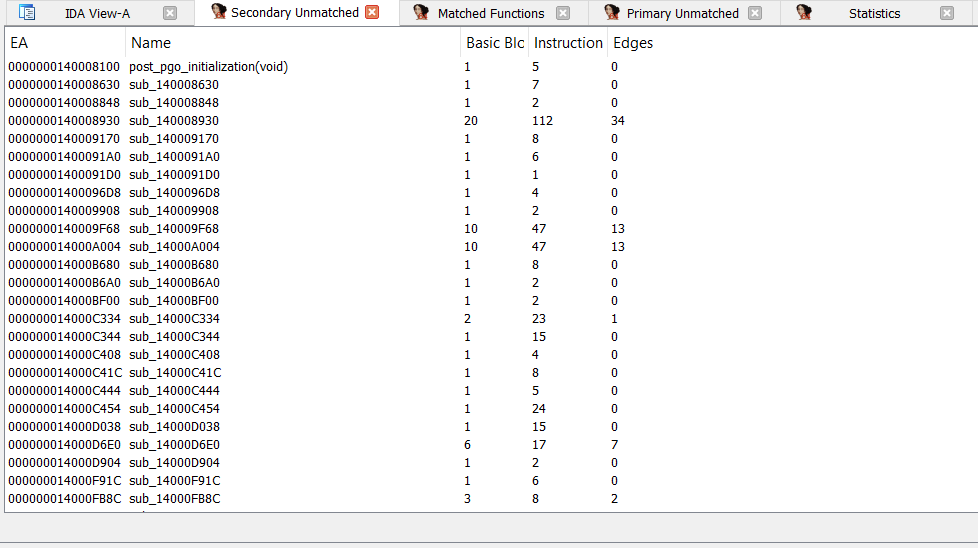
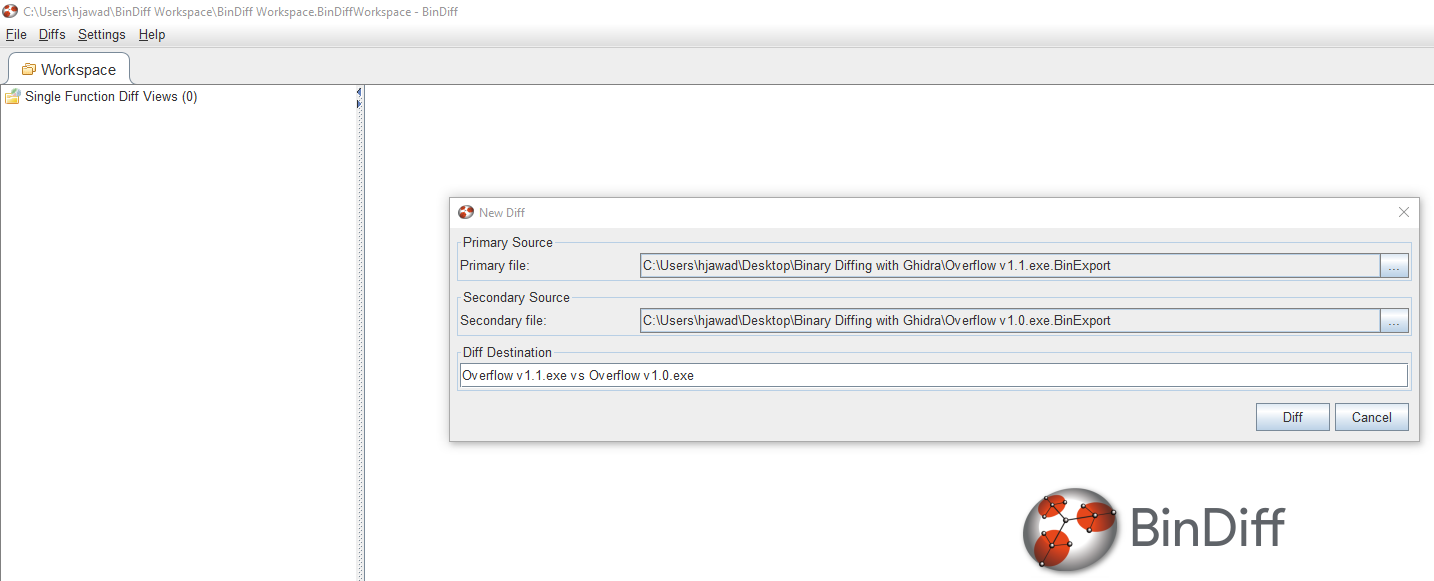
Binary Diffing Haiddy Deepdiff represents a major leap forward in security analysis. it helps security researchers, reverse engineers, and development teams to pinpoint vulnerable functions and generate precise diffing views across binary files with unmatched accuracy. Patch diffing remains a critical skill in cybersecurity, allowing researchers to identify vulnerabilities by comparing patched and unpatched software versions. in 2025, tools like bindiff and diaphora continue to evolve, now incorporating ai to enhance efficiency. Learn how to use ghidra’s patch diffing to compare two versions of a windows binary and identify the changes made to fix a vulnerability. you will learn how to root cause the vulnerability and understand its exploitation. To overcome this challenge, we propose a novel patch based vulnerability mining technique that leverages patch diffing analysis to accurately locate vulnerable code and conduct effective vulnerability mining, making the discovery process more efficient.

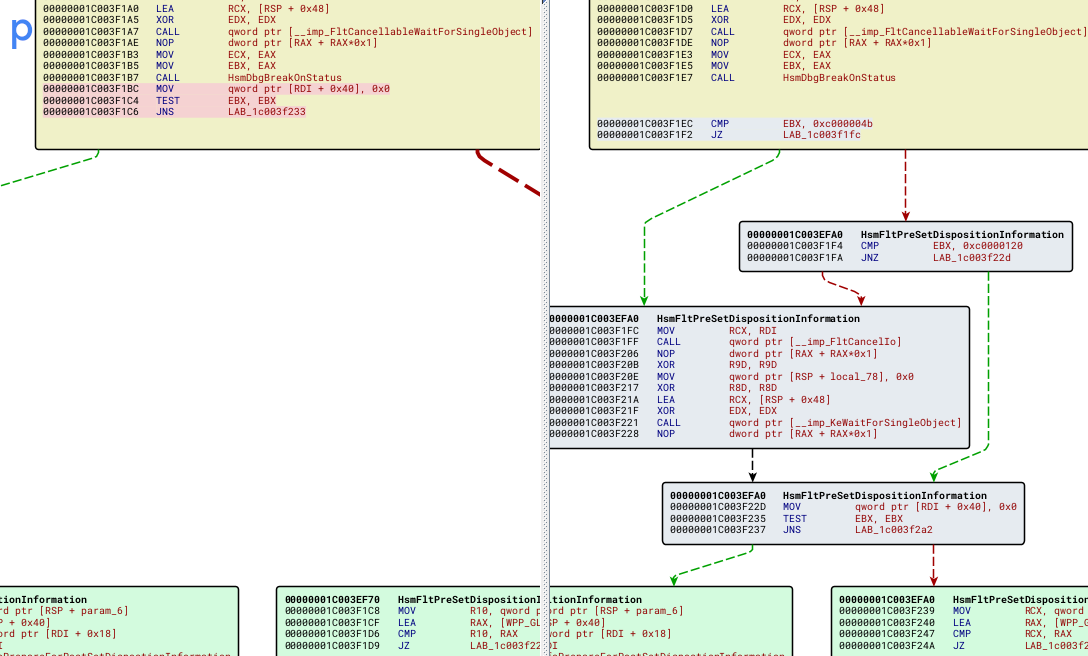
Modern Binary Patch Diffing R Blueteamsec Learn how to use ghidra’s patch diffing to compare two versions of a windows binary and identify the changes made to fix a vulnerability. you will learn how to root cause the vulnerability and understand its exploitation. To overcome this challenge, we propose a novel patch based vulnerability mining technique that leverages patch diffing analysis to accurately locate vulnerable code and conduct effective vulnerability mining, making the discovery process more efficient. By mastering binary patch diffing an essential skill for reverse engineering, vulnerability research, and malware analysis you'll gain the ability to identify security relevant changes in closed source binaries and uncover the underlying issues that make them exploitable. Researchers use binary diffing to compare known vulnerable binaries to post patch binaries in an attempt to suss out how a vulnerability was patched by the author. I had hoped i might find a recently patched vulnerability with an available poc that could simply trigger the bug. if a poc wasn't available, then maybe a blog post somewhere doing a root cause analysis so i could build my own poc to trigger the bug, and then later attempt to weaponize it. Learn the fundamentals of binary patch diffing with step by step examples, tools, and practical python implementations for reverse engineering and security analysis.
Patch Diffing In The Dark Patch Diffing In The Dark Cve 2021 1657 By mastering binary patch diffing an essential skill for reverse engineering, vulnerability research, and malware analysis you'll gain the ability to identify security relevant changes in closed source binaries and uncover the underlying issues that make them exploitable. Researchers use binary diffing to compare known vulnerable binaries to post patch binaries in an attempt to suss out how a vulnerability was patched by the author. I had hoped i might find a recently patched vulnerability with an available poc that could simply trigger the bug. if a poc wasn't available, then maybe a blog post somewhere doing a root cause analysis so i could build my own poc to trigger the bug, and then later attempt to weaponize it. Learn the fundamentals of binary patch diffing with step by step examples, tools, and practical python implementations for reverse engineering and security analysis.
Patch Diffing With Ghidra Low Level Shenanigans I had hoped i might find a recently patched vulnerability with an available poc that could simply trigger the bug. if a poc wasn't available, then maybe a blog post somewhere doing a root cause analysis so i could build my own poc to trigger the bug, and then later attempt to weaponize it. Learn the fundamentals of binary patch diffing with step by step examples, tools, and practical python implementations for reverse engineering and security analysis.
Windows Patch Diffing With Ghidra And Bindiff Rick S Blog
Comments are closed.