Best Practices For Zero Trust Workload Security On Eks Clusters

Best Practices For Zero Trust Workload Security On Eks Clusters In this post, we‘ll dive into how you can apply zero trust workload access controls along with microsegmentation for your workloads that run on amazon eks, and provide specific examples. Eks security best practices [cheat sheet] this 14 page cheat sheet is packed with actionable advice that you can put can in place immediately. you'll learn how to improve the security posture of your eks environment, from initial setup to ongoing monitoring and compliance.
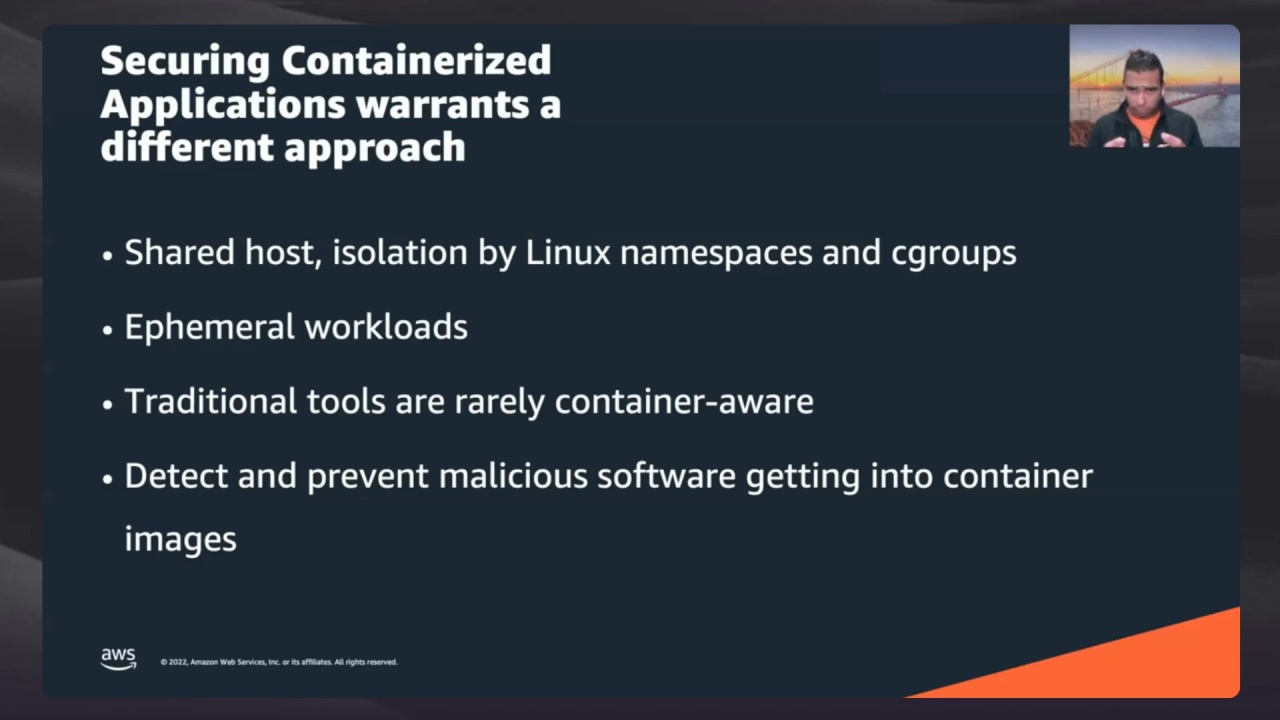
Zero Trust Workload Security Best Practices For Amazon Eks Workloads Learn how to secure aws eks workloads using zero trust principles and kubernetes network policies. explore best practices and real world security strategies. You will come away from this workshop with an understanding of how others in your industry are securing and observing cloud native applications in aws, along with best practices that you can implement in your organization. Besides providing a detailed walkthrough on how you can enforce zero trust workload access and microsegmentation for your eks workloads, this blog is also written with tigera’s aws devdays workshop in mind—meaning applicable examples and scenarios are included so you can follow along. Building resilient and secure eks clusters requires more than just spinning up nodes and deploying applications. this guide is designed for devops engineers, security professionals, and platform teams who need practical, battle tested strategies.

Implementing Zero Trust Workload Security On Amazon Eks With Calico Besides providing a detailed walkthrough on how you can enforce zero trust workload access and microsegmentation for your eks workloads, this blog is also written with tigera’s aws devdays workshop in mind—meaning applicable examples and scenarios are included so you can follow along. Building resilient and secure eks clusters requires more than just spinning up nodes and deploying applications. this guide is designed for devops engineers, security professionals, and platform teams who need practical, battle tested strategies. In today’s security conscious world, exposing your kubernetes api server to the internet is a risk many organizations can’t afford. whether you’re handling sensitive financial data, healthcare. This approach helps build secure and production ready kubernetes platforms for bfsi workloads. Learn to secure a private amazon eks cluster using cloudflare zero trust and warp. set up tunnels, bastion hosts, and secure kubernetes access without exposure. It covers critical aspects of protecting your eks clusters and workloads through multiple security domains, including identity and access management, pod security, network security, infrastructure protection, and more.

Aws Eks Security Best Practices What Is Eks In today’s security conscious world, exposing your kubernetes api server to the internet is a risk many organizations can’t afford. whether you’re handling sensitive financial data, healthcare. This approach helps build secure and production ready kubernetes platforms for bfsi workloads. Learn to secure a private amazon eks cluster using cloudflare zero trust and warp. set up tunnels, bastion hosts, and secure kubernetes access without exposure. It covers critical aspects of protecting your eks clusters and workloads through multiple security domains, including identity and access management, pod security, network security, infrastructure protection, and more.
Comments are closed.