Best Practices For Effective Implementation Of Zero Trust Architecture
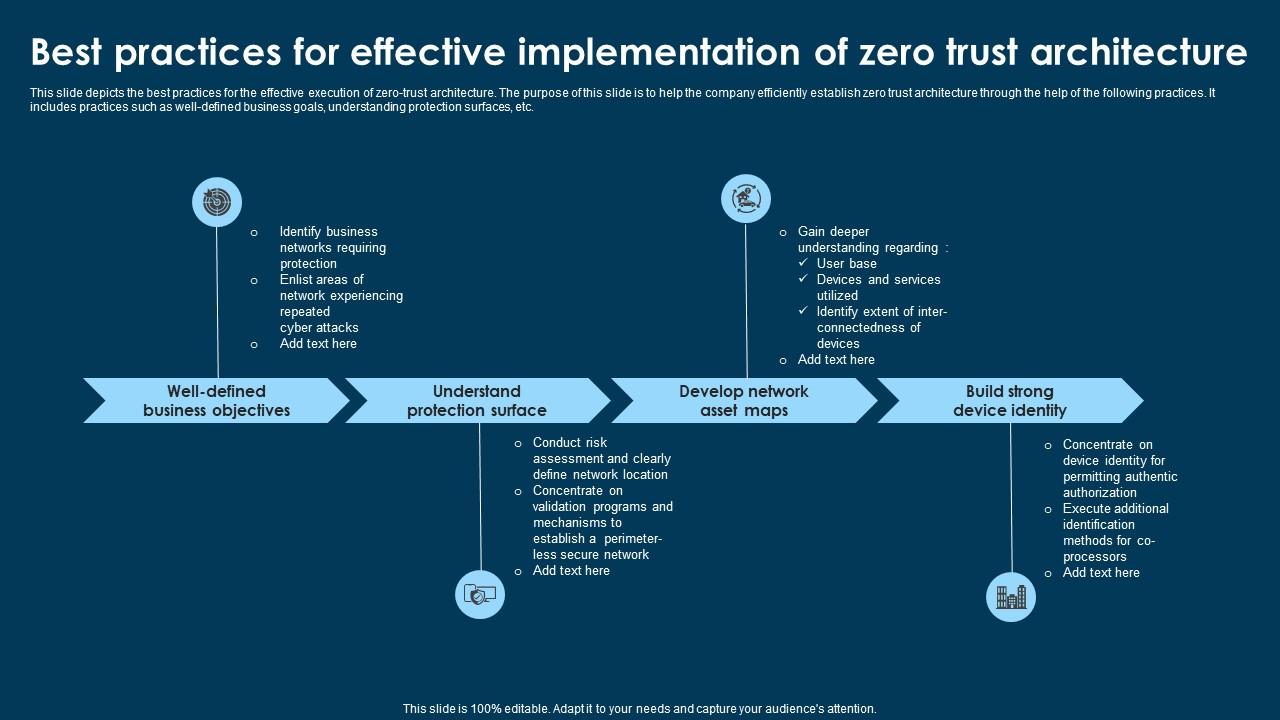
Best Practices For Effective Implementation Of Zero Trust Architecture Learn how to implement zero trust architecture with best practices, overcome challenges, and ensure compliance for robust cybersecurity. This paper explores the implementation of zero trust architecture, detailing its core principles, components, challenges, and best practices.

Rh Isac Zero Trust Architecture Zta How To Get Started Rh Isac In this guide, we’ll break down everything you need to know about zero trust implementation, from core principles and architecture to step by step deployment and best practices. To help shift from strategy to practice, we’ll clarify key zero trust concepts, explain the most influential models, explore top benefits, and share best practices in this complete guide to zero trust. This publication outlines results and best practices from the nccoe effort to work with 24 vendors to demonstrate end to end zero trust architectures. two resources of nist sp 1800 35 have been released. Best practices for implementing zero trust architecture include implementing least privilege access, continuous monitoring and assessment, and using multi factor authentication to verify user and device identities.

Zero Trust Architecture This publication outlines results and best practices from the nccoe effort to work with 24 vendors to demonstrate end to end zero trust architectures. two resources of nist sp 1800 35 have been released. Best practices for implementing zero trust architecture include implementing least privilege access, continuous monitoring and assessment, and using multi factor authentication to verify user and device identities. Guide to implementing zero trust architecture. covers identity verification, micro segmentation, least privilege access, and practical deployment strategies. When applied in zero trust architecture (zta), it’s one of the most effective routes to increase a company’s cybersecurity status effectively. here are some of the best practices for zero trust adoption that should help your transition. Learn how to implement zero trust security and the steps you need to take. understand why implementation involves a policy of never trusting and always verifying the authenticity and privileges of devices and users. This blog summarizes key insights from the sans strategy guide, navigating the path to a state of zero trust in 2024, providing a detailed overview of the challenges, strategies, and best practices for implementing zero trust in today's complex digital environment.

Zero Trust Architecture Importance And Practical Implementation Guide to implementing zero trust architecture. covers identity verification, micro segmentation, least privilege access, and practical deployment strategies. When applied in zero trust architecture (zta), it’s one of the most effective routes to increase a company’s cybersecurity status effectively. here are some of the best practices for zero trust adoption that should help your transition. Learn how to implement zero trust security and the steps you need to take. understand why implementation involves a policy of never trusting and always verifying the authenticity and privileges of devices and users. This blog summarizes key insights from the sans strategy guide, navigating the path to a state of zero trust in 2024, providing a detailed overview of the challenges, strategies, and best practices for implementing zero trust in today's complex digital environment.
Comments are closed.