Benefits Of Identity Based Access Control
Why Companies Need Identity And Access Management Iam Benefits of identity based access control. by tying access to unique, authenticated identities, ibac ensures that only verified users or systems can access sensitive resources. permissions can be defined at a fine level, allowing organizations to assign access on a per user or per device basis. Discover the benefits of identity based access control (iam) for enhancing security, improving efficiency, and reducing costs in your organization.

Benefits Of Identity Based Access Control Iac Instasafe What are the benefits of identity based access control? ibac ensures precise access control, enhances security, and minimizes the risk of unauthorized access by linking permissions directly to individual identities. Every access choice is based on confirmed identity, according to ibac. ibac explicitly links access permissions to the verified individual identification, in contrast to methods that depend on broad roles or intricate policies. Learn what identity based access control is, its benefits, key components, and how it supports secure, scalable access in cloud native environments. Discover the top 7 benefits of identity and access management (iam). learn how iam solutions enhance security posture, automate lifecycle management, and more.

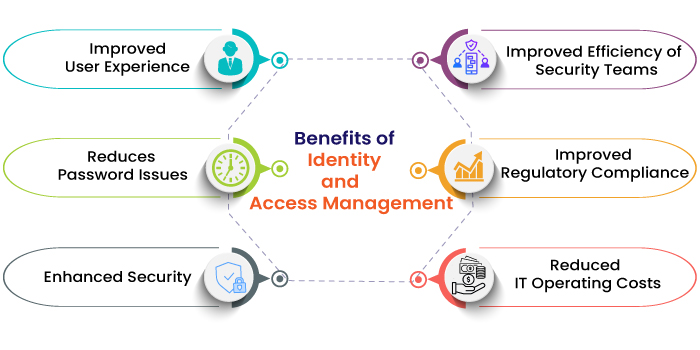
Iam Benefits Challenges Learn what identity based access control is, its benefits, key components, and how it supports secure, scalable access in cloud native environments. Discover the top 7 benefits of identity and access management (iam). learn how iam solutions enhance security posture, automate lifecycle management, and more. Learn the core concepts of identity and access management (iam), including authentication, authorization, and identity providers, to secure resources effectively. Identity and access management (iam) enables enterprises to securely control user access, prevent data breaches, boost productivity with sso and automation, streamline compliance, reduce it costs, and enhance the overall user experience. Listed below are the 7 significant identity and access management benefits that your organization can gain through the implementation of identity and access management:. Discover the 8 key benefits of identity and access management (iam) for enhancing security. learn how iam can protect your organization effectively.

Infographic Key Business Benefits Of Identity And Access Management Learn the core concepts of identity and access management (iam), including authentication, authorization, and identity providers, to secure resources effectively. Identity and access management (iam) enables enterprises to securely control user access, prevent data breaches, boost productivity with sso and automation, streamline compliance, reduce it costs, and enhance the overall user experience. Listed below are the 7 significant identity and access management benefits that your organization can gain through the implementation of identity and access management:. Discover the 8 key benefits of identity and access management (iam) for enhancing security. learn how iam can protect your organization effectively.
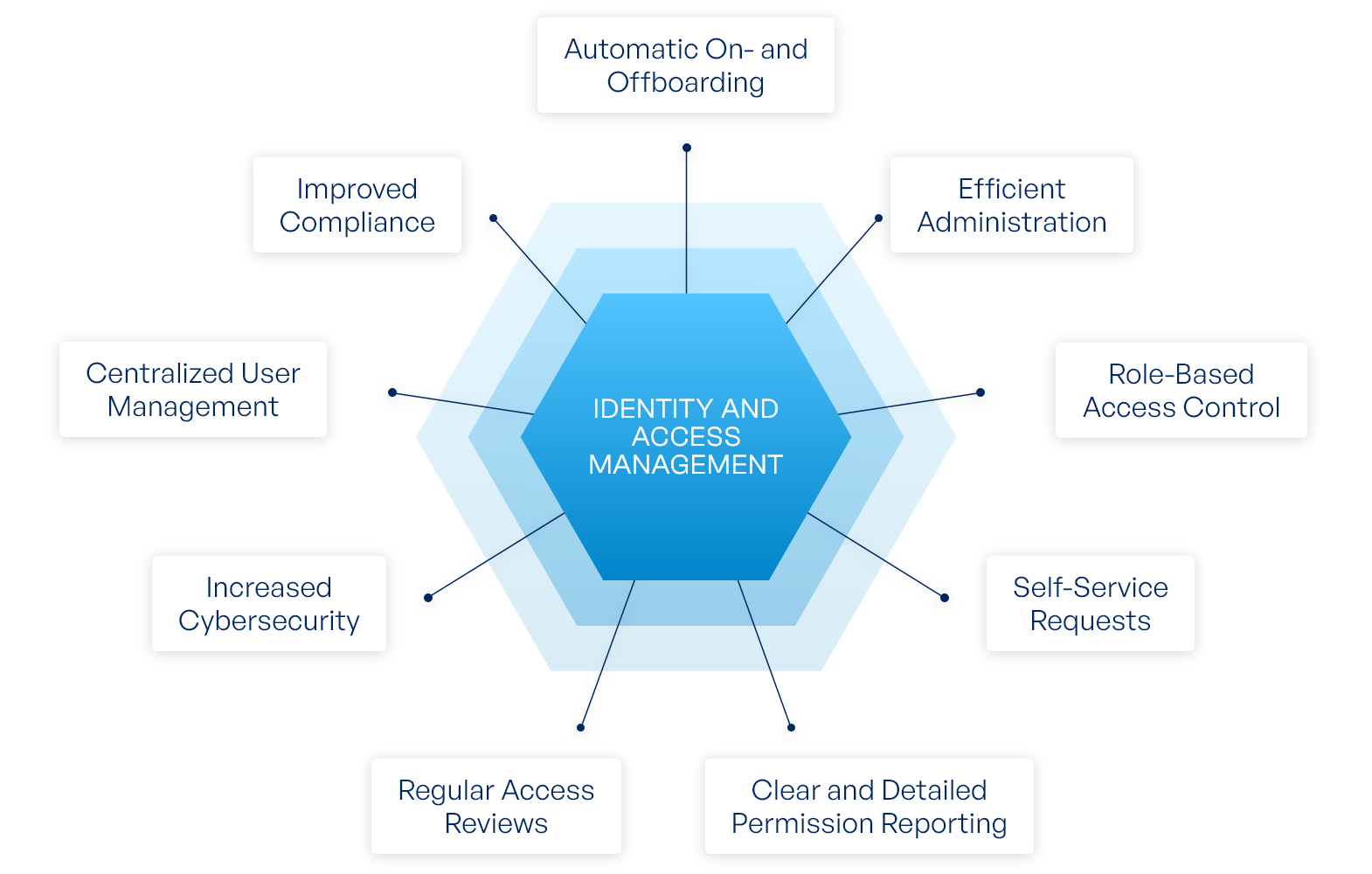
Octree Iam Listed below are the 7 significant identity and access management benefits that your organization can gain through the implementation of identity and access management:. Discover the 8 key benefits of identity and access management (iam) for enhancing security. learn how iam can protect your organization effectively.

Facial Recognition For Access Control
Comments are closed.