Before Vs After Zero Trust Network Access Implementation Software
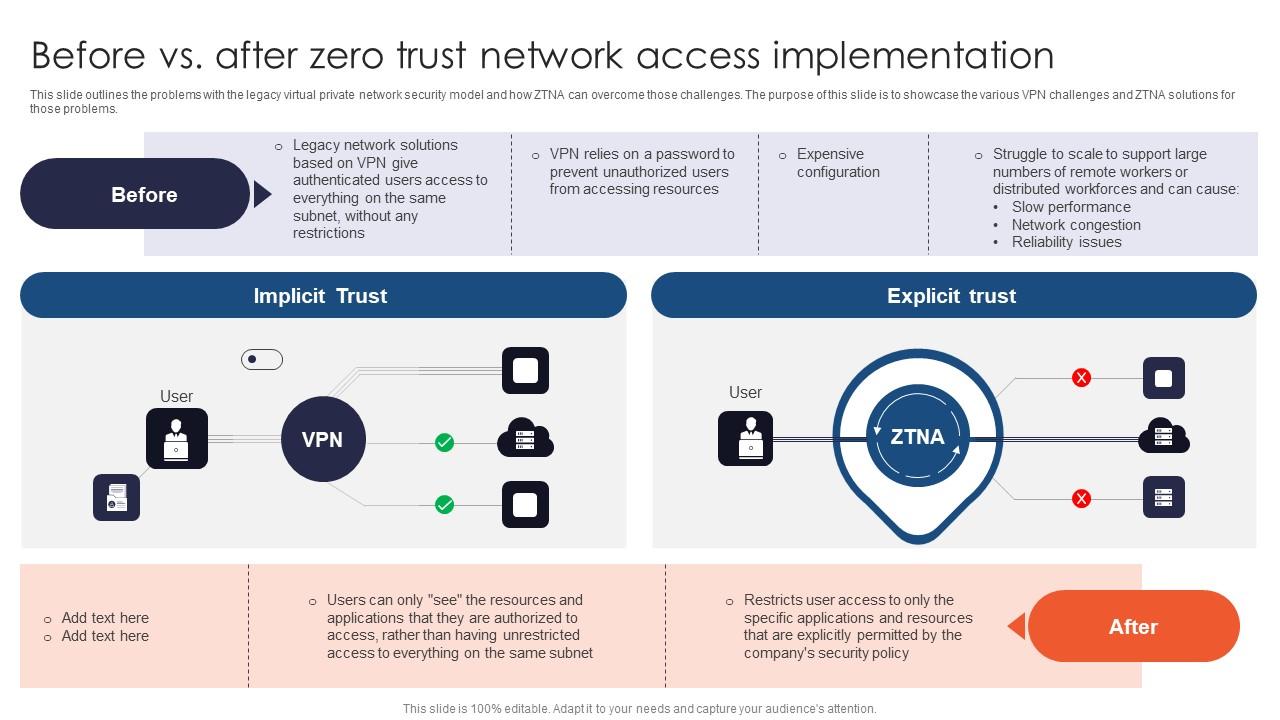
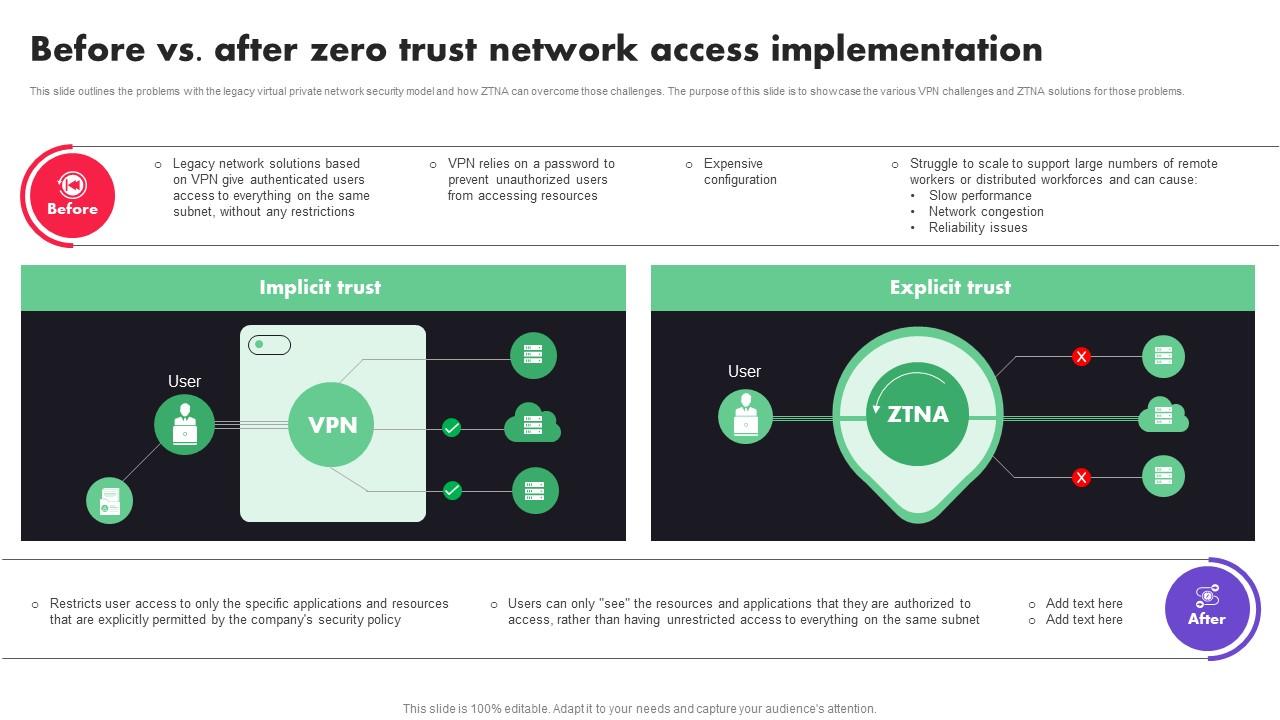
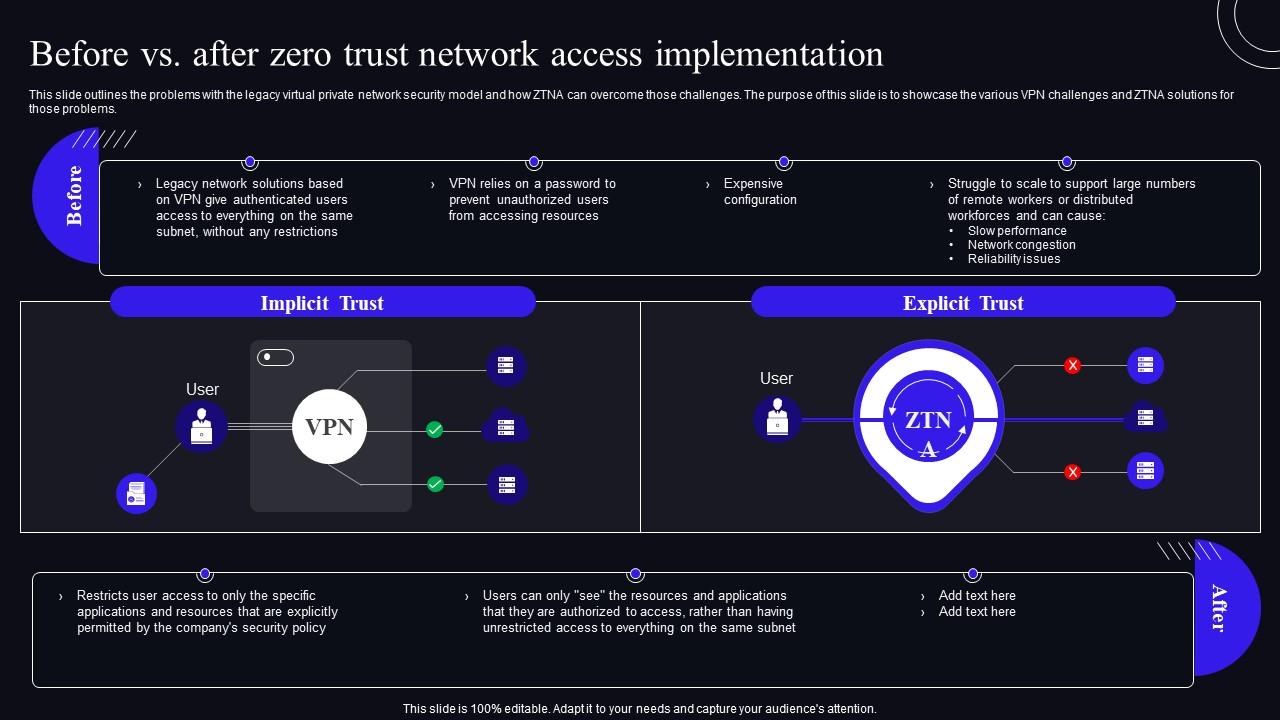
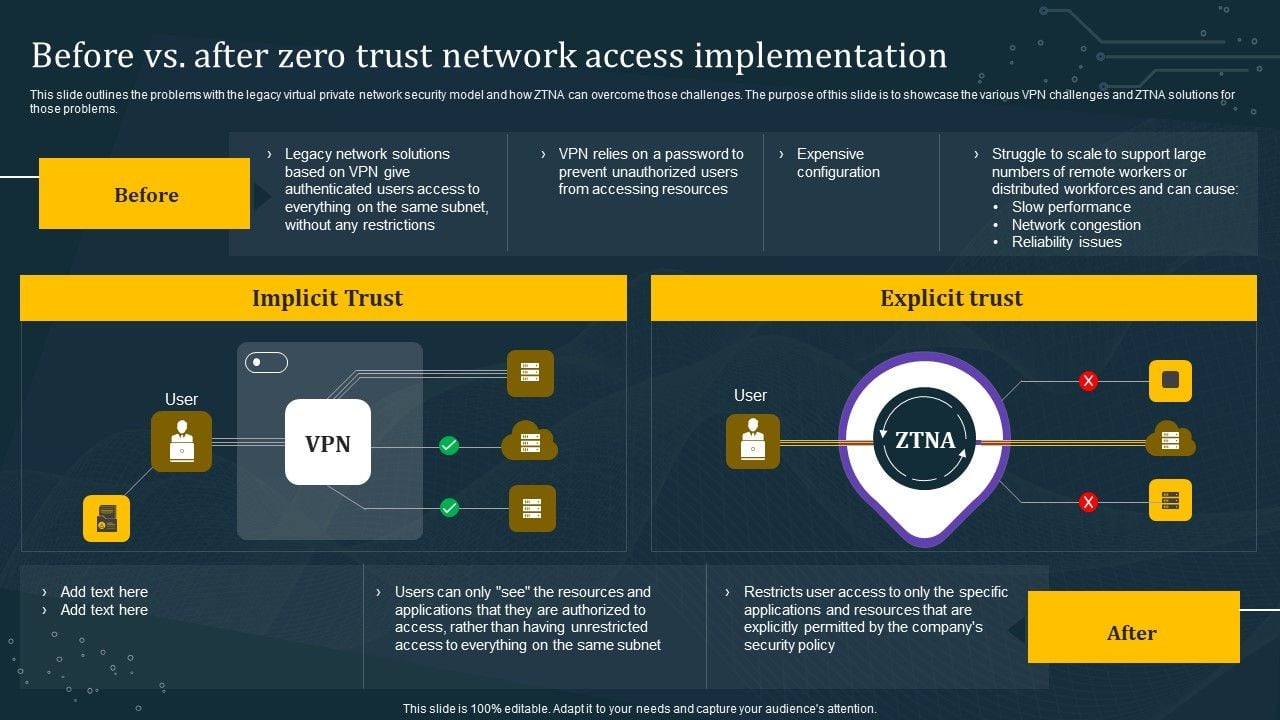
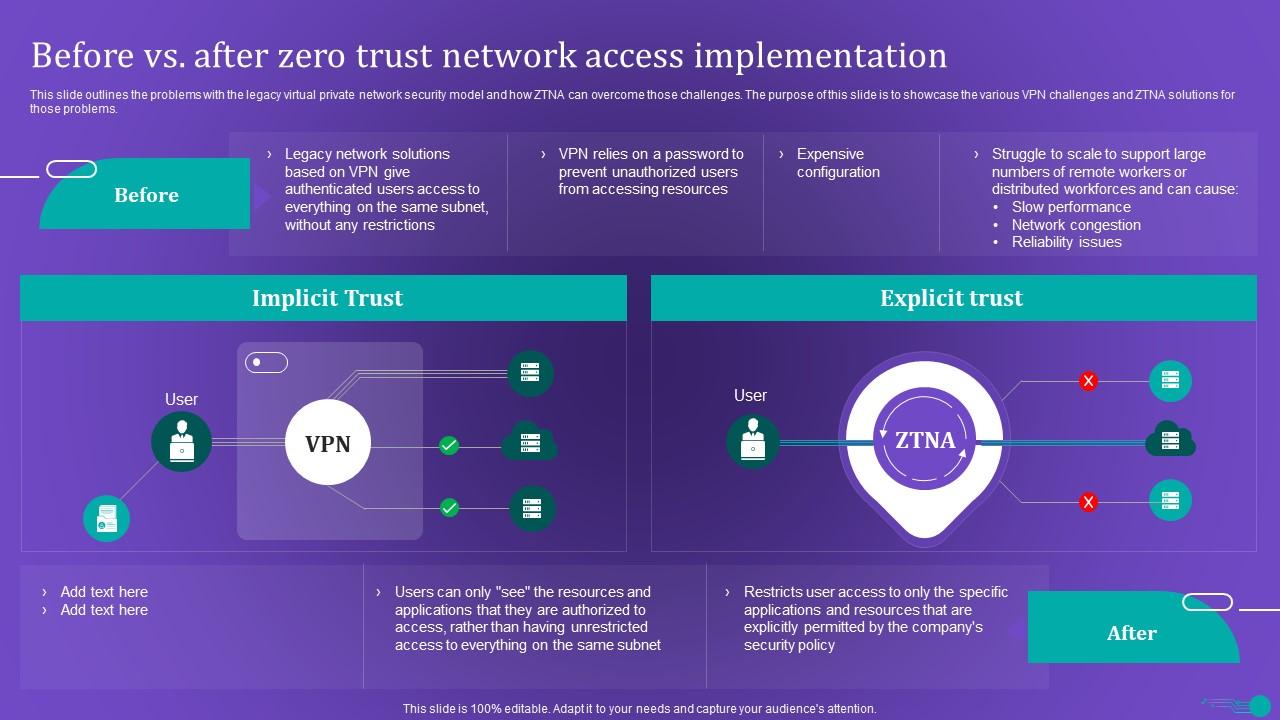
Zero Trust Network Access Before Vs After Zero Trust Network Access Impleme This slide outlines the problems with the legacy virtual private network security model and how ztna can overcome those challenges. the purpose of this slide is to showcase the various vpn challenges and ztna solutions for those problems. Use our before vs after zero trust network access implementation software defined perimeter sdp to effectively help you save your valuable time. they are readymade to fit into any presentation structure.
Before Vs After Zero Trust Network Access Implementation Ppt Sample Zero trust is easy to understand, but hard to implement, as it requires architectural changes, not just technical controls. let’s understand step by how to implement zero trust in practice. We show you the best zero trust networking software solutions. zero trust networking is a modern approach to cybersecurity that challenges traditional network security models, particularly the once popular “trust but verify” approach. Learn how to implement zero trust security and the steps you need to take. understand why implementation involves a policy of never trusting and always verifying the authenticity and privileges of devices and users. If you’re searching for the best zero trust networking software for 2025, here are my top picks. whether you’re standardizing on a single client or segmenting sensitive apps first, these platforms stood out for flexibility, scalability, and real world usability.
Before Vs After Zero Trust Network Access Implementation Zero Trust Learn how to implement zero trust security and the steps you need to take. understand why implementation involves a policy of never trusting and always verifying the authenticity and privileges of devices and users. If you’re searching for the best zero trust networking software for 2025, here are my top picks. whether you’re standardizing on a single client or segmenting sensitive apps first, these platforms stood out for flexibility, scalability, and real world usability. This roadmap was built by security experts to provide a vendor agnostic zero trust architecture and example implementation timeline. the timeline assumes that an organization is beginning their zero trust journey from scratch, but is meant to be useful for all organizations. After evaluating over 20 zero trust software solutions in their free versions, we’ve shortlisted eight that deliver high value even in their open source offerings. 1. pomerium. an identity aware reverse proxy that provides secure access to internal applications without the need for a corporate vpn. Cloudnuro complements network access control (nac) tools by serving as an enterprise saas management platform that extends zero trust enforcement beyond the network perimeter. This document provides guidance on the various zero trust frameworks and their relationship to the cisco zero trust framework. for each of the zero trust frameworks a mapping to cisco product is provided.
Before Vs After Zero Trust Network Access Implementation Background Pdf This roadmap was built by security experts to provide a vendor agnostic zero trust architecture and example implementation timeline. the timeline assumes that an organization is beginning their zero trust journey from scratch, but is meant to be useful for all organizations. After evaluating over 20 zero trust software solutions in their free versions, we’ve shortlisted eight that deliver high value even in their open source offerings. 1. pomerium. an identity aware reverse proxy that provides secure access to internal applications without the need for a corporate vpn. Cloudnuro complements network access control (nac) tools by serving as an enterprise saas management platform that extends zero trust enforcement beyond the network perimeter. This document provides guidance on the various zero trust frameworks and their relationship to the cisco zero trust framework. for each of the zero trust frameworks a mapping to cisco product is provided.
Ztna Before Vs After Zero Trust Network Access Implementation Ppt Slide Cloudnuro complements network access control (nac) tools by serving as an enterprise saas management platform that extends zero trust enforcement beyond the network perimeter. This document provides guidance on the various zero trust frameworks and their relationship to the cisco zero trust framework. for each of the zero trust frameworks a mapping to cisco product is provided.

Zero Trust Network Access 7 0 Architecture Guide Pdf Proxy Server
Comments are closed.