Bd760bd32d4247f36809b976b7c86835 Jpg
Bfa3c6e990631126bf1cf47c84fceb23 Postimages Uncover it is a malware configuration extractor that can analyze files statically. You'll see a step by step process demonstrating how gemini powered agents quickly build a robust threat model, automate the hunt sequence, and operationalize the entire workflow. advanced threat hunting: turn natural language into vt api python code instantly!.

Raw Vs Jpeg Which Image Format Is Better And Why Raw Vs Jpeg Raw Using advanced hashing algorithms osforensics can create a digital identifier that can be used to identify a file. this identifier can be used both to verify a file has not been changed or to quickly find out if a file is part of a set of known files. Enter a file's sha256 to search talos' current file reputation system. the disposition search will return a file's reputation, file name, weighted reputation score (if available), and detection information, in addition to alternate detection names used by other vendors. This is fine for simple images, but it does not suit the compression of photographs, thus the jpeg standard was developed by the joint photographic expert group (jpeg), which is a subcommittee of the iso iec. After we executed a sample of mimic on our testing system, it encrypted files and appended their filenames with a ".quietplace " extension. for example, a file initially named " 1 " appeared as " 1 .quietplace ", " 2 " as " 2 .quietplace ", and so on. pcrisk removal guides 25932 mimic ransomware.
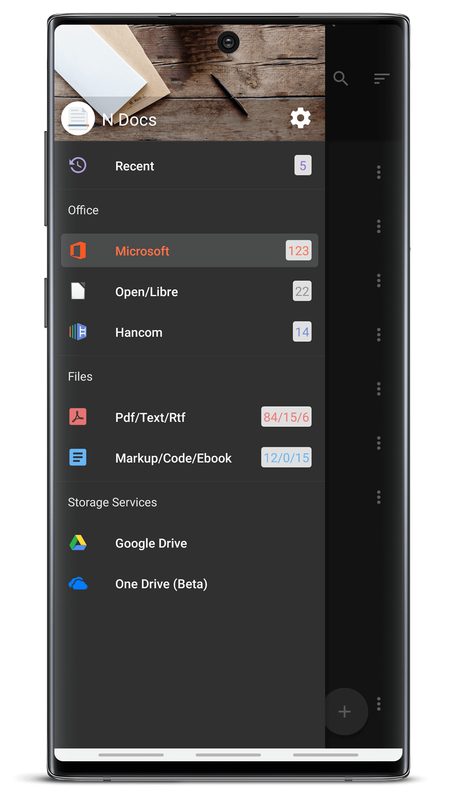
8ad9f920 22f3 4071 9208 A663e1b46d12 2 Converted This is fine for simple images, but it does not suit the compression of photographs, thus the jpeg standard was developed by the joint photographic expert group (jpeg), which is a subcommittee of the iso iec. After we executed a sample of mimic on our testing system, it encrypted files and appended their filenames with a ".quietplace " extension. for example, a file initially named " 1 " appeared as " 1 .quietplace ", " 2 " as " 2 .quietplace ", and so on. pcrisk removal guides 25932 mimic ransomware. All of gdi malwares, non gdi malwares, ransomwares, and more will be here! 🙂 n17pro3426 viewermade. Fileslockerdecrypter is a ransomware decryptor created by michael gillespie that decrypts files encrypted by the fileslocker ransomware. this decrypter works with version v1 and v2 of the. Filedetails , created by james william steven parker, is the most comprehensive and authoritative resource for identifying, understanding, and verifying files on your system or within software programs. Free browser tool to identify unknown files based on their contents. recognizes over 2000 file formats using libmagic. no installation necessary. just drag & drop!.
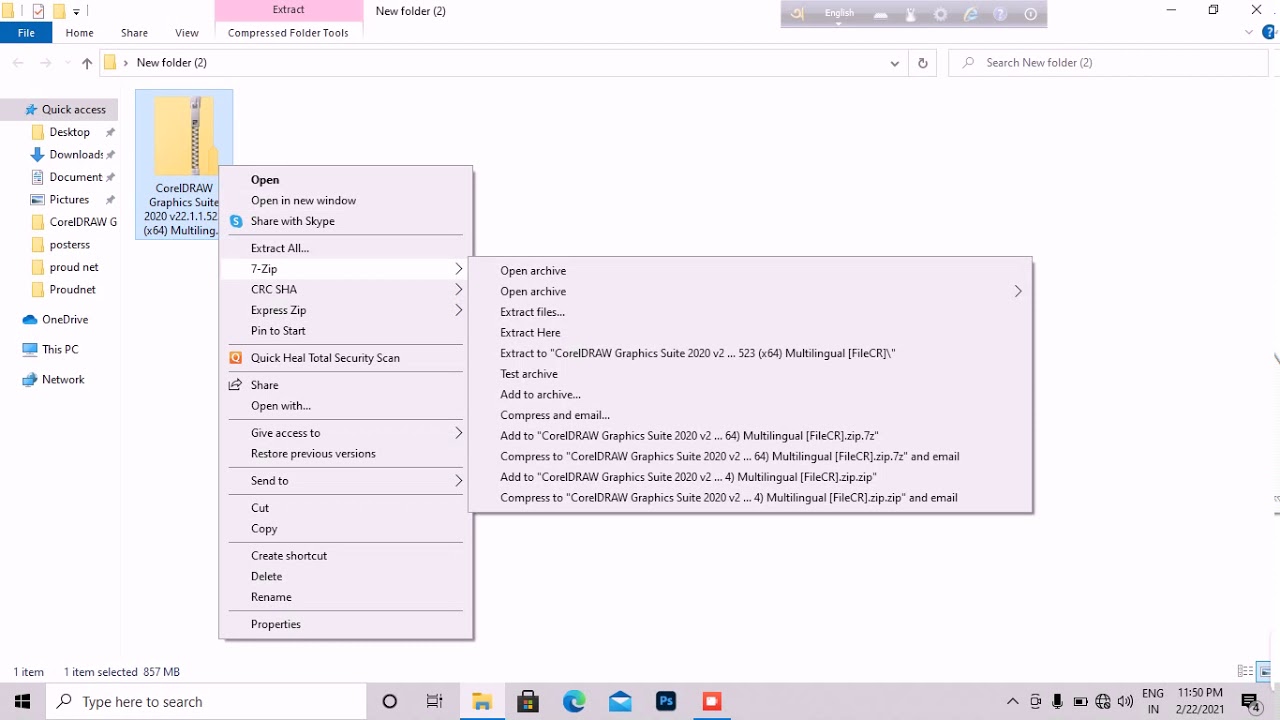
C4f2cb7f81064a149192644fa573bdd300 06 59 Youtube All of gdi malwares, non gdi malwares, ransomwares, and more will be here! 🙂 n17pro3426 viewermade. Fileslockerdecrypter is a ransomware decryptor created by michael gillespie that decrypts files encrypted by the fileslocker ransomware. this decrypter works with version v1 and v2 of the. Filedetails , created by james william steven parker, is the most comprehensive and authoritative resource for identifying, understanding, and verifying files on your system or within software programs. Free browser tool to identify unknown files based on their contents. recognizes over 2000 file formats using libmagic. no installation necessary. just drag & drop!.
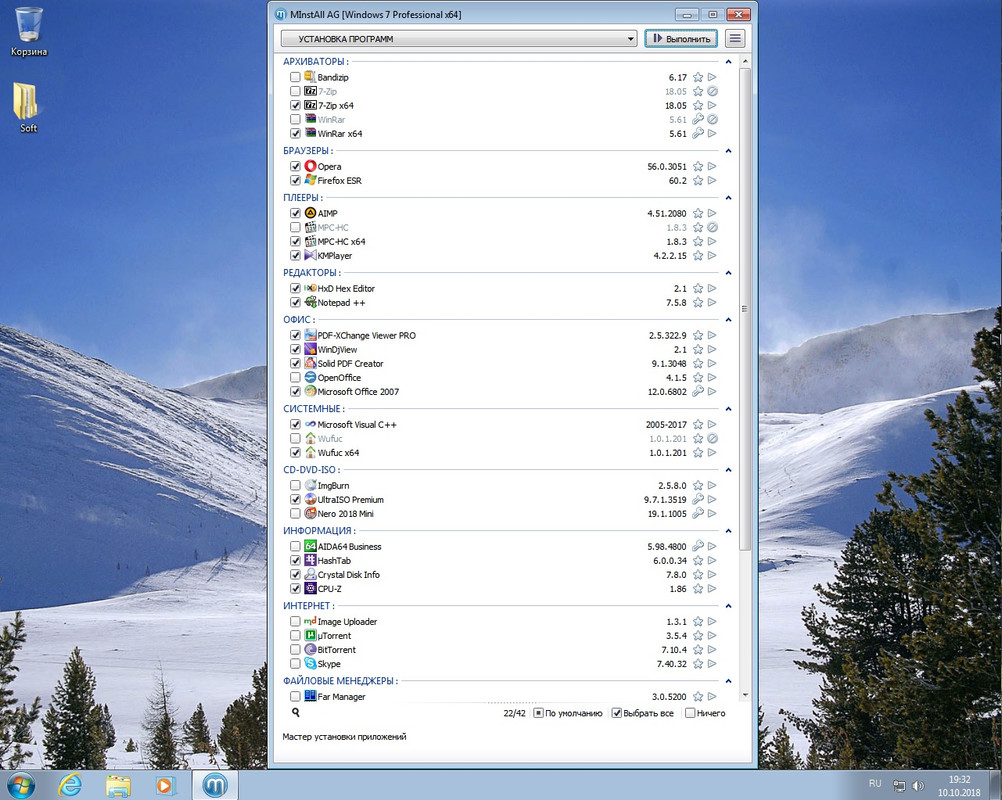
9cc0779473b463c0f56cddaaba45cb08 Postimages Filedetails , created by james william steven parker, is the most comprehensive and authoritative resource for identifying, understanding, and verifying files on your system or within software programs. Free browser tool to identify unknown files based on their contents. recognizes over 2000 file formats using libmagic. no installation necessary. just drag & drop!.

D75ada60d6e34a82b6eb46c923a84d37 Youtube
Comments are closed.