Bd3c6d557055f9f97316b2ec98966de3 Jpg
Bfa3c6e990631126bf1cf47c84fceb23 Postimages Search the world's information, including webpages, images, videos and more. google has many special features to help you find exactly what you're looking for. Uncover it is a malware configuration extractor that can analyze files statically.

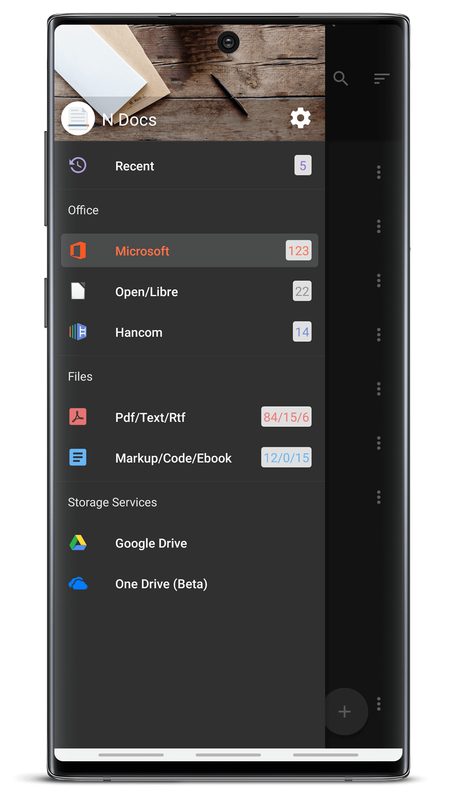
Preview File My software utility page contains a custom signature file based upon this list, for use with ftk, scalpel, simple carver, simple carver lite, and trid. there is also a raw csv file and json file of signatures. tim coakley's filesig.co.uk site, with filesig manager and simple carver. Join our upcoming webinar on november 6th at 17:00 pm cest and 11:00 am edt where we'll show you how to transform raw intelligence into a dynamic, actionable defense strategy. we’ll start with a real world scenario from google threat intelligence. View and convert files online securely with our online file viewer. content is displayed in a secure sandbox in your browser. share previews and convert files easily. All of gdi malwares, non gdi malwares, ransomwares, and more will be here! 🙂 n17pro3426 viewermade.

1be7bea28a6009b6a493696890c8a5d4 Jpg Wowshack View and convert files online securely with our online file viewer. content is displayed in a secure sandbox in your browser. share previews and convert files easily. All of gdi malwares, non gdi malwares, ransomwares, and more will be here! 🙂 n17pro3426 viewermade. Identify, view, and convert your files with one easy to use web utility. Free browser tool to identify unknown files based on their contents. recognizes over 2000 file formats using libmagic. no installation necessary. just drag & drop!. You'll see a step by step process demonstrating how gemini powered agents quickly build a robust threat model, automate the hunt sequence, and operationalize the entire workflow. advanced threat hunting: turn natural language into vt api python code instantly!. Cn 2 8 2 #3254 basic model by steve lerro and tyler bishop.
4914993731 5b79d565ce Jpg A Ki Blog Identify, view, and convert your files with one easy to use web utility. Free browser tool to identify unknown files based on their contents. recognizes over 2000 file formats using libmagic. no installation necessary. just drag & drop!. You'll see a step by step process demonstrating how gemini powered agents quickly build a robust threat model, automate the hunt sequence, and operationalize the entire workflow. advanced threat hunting: turn natural language into vt api python code instantly!. Cn 2 8 2 #3254 basic model by steve lerro and tyler bishop.
Comments are closed.