Bbse Lecture 2 Cryptographic Basics
Cse2203 Lecture 3 Modern Cryptography And Cryptographic Mechanisms Cryptographic basics 1:50 2.1 cryptographic hash functions 3:20 2.1.1 properties of cryptographic hash functions 6:39 2.1.2 additional properties of cryptographic hash functions 10:13 2.1.3. Lecture slides "blockchain based systems engineering" bbse slides 02 cryptographic basics.pdf at master · jin analytics bbse.

Lecture 1 1 Introduction Cryptography Updated Pdf Cryptography Смотрите видео онлайн «bbse lecture 2: cryptographic basics» на канале «js Для Тех, Кто Никогда Не Программировал» в хорошем качестве и бесплатно, опубликованное 29 ноября 2023 года в 1:22, длительностью 01:52:20. The document outlines a lecture on cryptographic building blocks essential for computer security, covering topics such as encryption and decryption, symmetric and public key encryption, and various cipher attack models. Basic cryptography how cryptography works symmetric cryptography public key cryptography online resources. Bbse lecture 1: relevance of blockchain based systems engineering sebisresearch • 1.4k views • 4 years ago.

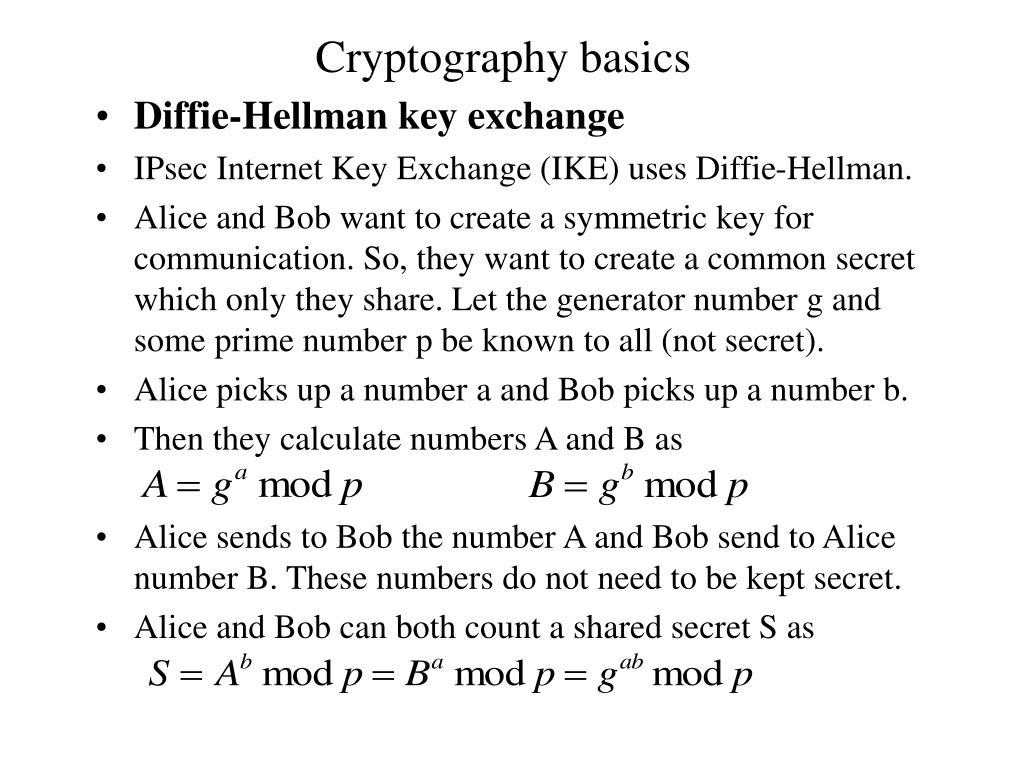
Lecture2 1 Part One About Cryptography Ppt Basic cryptography how cryptography works symmetric cryptography public key cryptography online resources. Bbse lecture 1: relevance of blockchain based systems engineering sebisresearch • 1.4k views • 4 years ago. To prevent cheating, they want to use their knowledge of cryptography to devise a commitment scheme based on hashing. to start out, they consider possible hash functions. Follows the more traditional form of cryptography with key lengths ranging from 40 to 256 bits. how do we securely distribute the shared secret key between the sender and receiver? what if you want to communicate with multiple people, and each communication needs to be confidential? how many keys do we have to manage? a key for each! key explosion!. • in 1976, diffie and hellman first proposed the idea of asymmetric cryptography in their article “new directions in cryptography”, which played an extremely important role in promoting the development of cryptography. Understand the basic concepts of cryptography, its goals, terminology, and how cryptographic systems work. this section explains the fundamentals of securing information and the basic components of cryptographic systems.
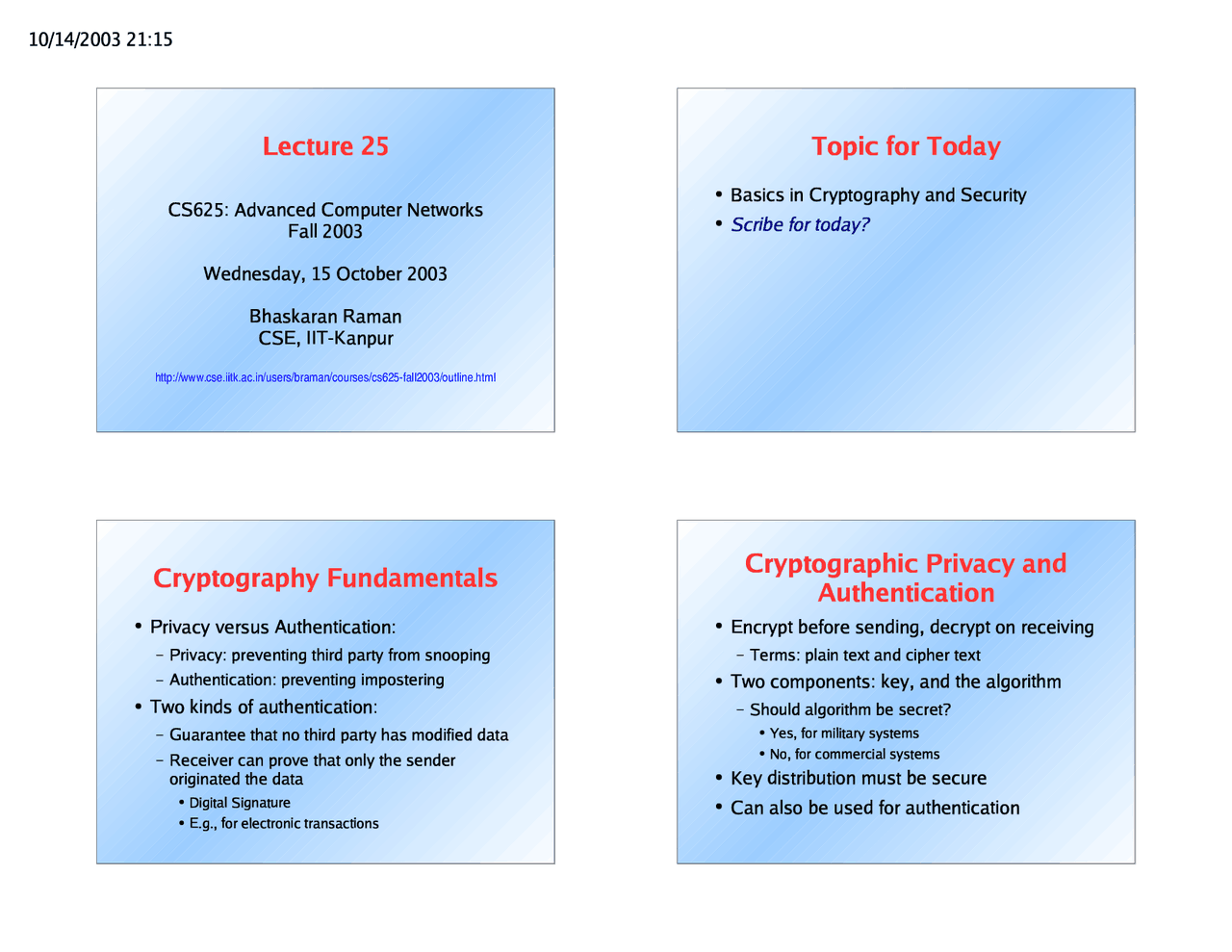
Basics In Cryptography And Security Main Concepts Slides Computer To prevent cheating, they want to use their knowledge of cryptography to devise a commitment scheme based on hashing. to start out, they consider possible hash functions. Follows the more traditional form of cryptography with key lengths ranging from 40 to 256 bits. how do we securely distribute the shared secret key between the sender and receiver? what if you want to communicate with multiple people, and each communication needs to be confidential? how many keys do we have to manage? a key for each! key explosion!. • in 1976, diffie and hellman first proposed the idea of asymmetric cryptography in their article “new directions in cryptography”, which played an extremely important role in promoting the development of cryptography. Understand the basic concepts of cryptography, its goals, terminology, and how cryptographic systems work. this section explains the fundamentals of securing information and the basic components of cryptographic systems.
Lecture 1 Pdf Cryptography Computer Science • in 1976, diffie and hellman first proposed the idea of asymmetric cryptography in their article “new directions in cryptography”, which played an extremely important role in promoting the development of cryptography. Understand the basic concepts of cryptography, its goals, terminology, and how cryptographic systems work. this section explains the fundamentals of securing information and the basic components of cryptographic systems.
Ppt Cryptographic Basics Powerpoint Presentation Free Download Id
Comments are closed.