Bbse Exercise 1 Cryptographic Basics

Basics Pdf Exercise 1: cryptographic basicsblockchain based systems engineering (english)0:00 1. cryptographic basics0:04 1.1 properties of hash functions4:12 1.2 rock,. Lecture slides "blockchain based systems engineering" bbse slides 02 cryptographic basics.pdf at master · jin analytics bbse.

02 Cryptographic Basics Flashcards Quizlet In a nutshell: each letter of the keyword relations picks out 1 of the 26 possible substitution alphabets given in the vigen`ere tableau. thus, any message encrypted by a vigen`ere cipher is a collection of as many simple substitution ciphers as there are letters in the keyword. Online cryptography course preview: this page contains all the lectures in the free cryptography course. to officially take the course, including homeworks, projects, and final exam, please visit the course page at coursera. Basic cryptography how cryptography works symmetric cryptography public key cryptography online resources. Understand the basic concepts of cryptography, its goals, terminology, and how cryptographic systems work. this section explains the fundamentals of securing information and the basic components of cryptographic systems.
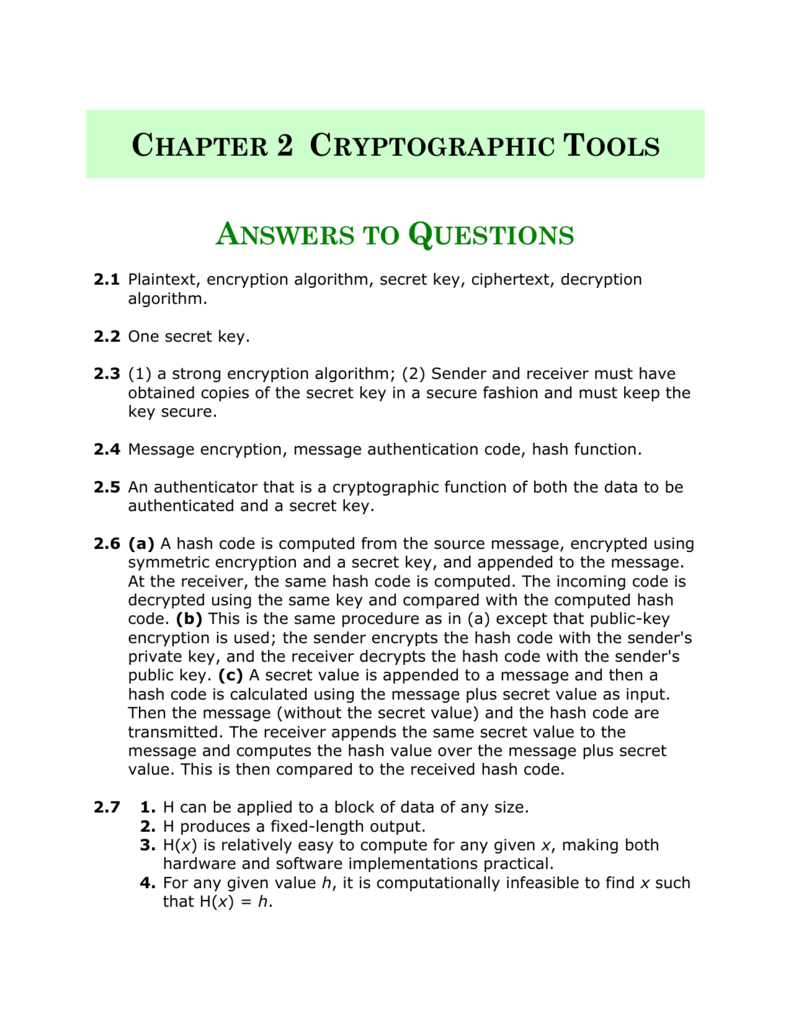
Chapter 2 Cryptographic Tools Basic cryptography how cryptography works symmetric cryptography public key cryptography online resources. Understand the basic concepts of cryptography, its goals, terminology, and how cryptographic systems work. this section explains the fundamentals of securing information and the basic components of cryptographic systems. To prevent cheating, they want to use their knowledge of cryptography to devise a commitment scheme based on hashing. to start out, they consider possible hash functions. 1) the document contains answers to practice questions for a cryptography exam. it discusses the basic requirements of cryptosystems like security, endpoint security, and secure key management. Rail fence cipher – another kind of transposition cipher in which the words are spelled out as if they were a rail fence. • the system must not be required to be secret, and it must be able to fall into the hands of the enemy without inconvenience. no system is unbreakable!. This tutorial is meant for students of computer science who aspire to learn the basics of cryptography. it will be helpful for networking professionals as well who would like to incorporate various cryptographic algorithms to ensure secure data communication over their networks.
Comments are closed.