Balancing Security And Performance Encrypted Traffic Decryption For
What Makes A Strong Firewall Palo Alto Networks Over 80% of cyber attacks use encryption today to hide malicious activity, which reduces the efficacy of network security detection unless it decrypts the traffic. To strike the right balance between security and efficiency, consider using hybrid encryption methods or hardware accelerated encryption. these approaches safeguard essential data while keeping performance impacts to a minimum.
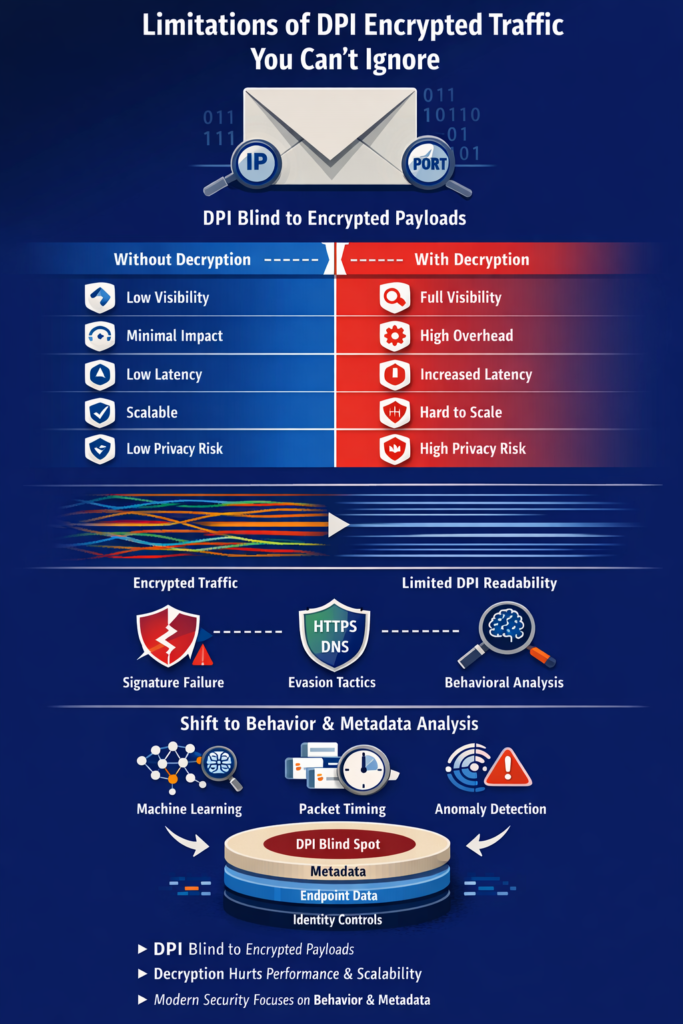
Limitations Of Dpi Encrypted Traffic You Can T Ignore Network Threat This paper explores the balance between security and performance in cloud encryption, discussing the key encryption methods and technologies employed by major cloud service providers. This study focuses on evaluating the performance of two prominent tools, ssldump and tshark, in decrypting and inspecting encrypted network traffic, assuming an environment where decryption keys are available. The fast mode spoke to ivan shefrin, executive director of comcast business managed security services on new encryption technologies and their impact on today's networks. Discover how encryption impacts cloud application speed. learn to balance data protection with performance, explore algorithm choices, and find solutions for secure, responsive cloud services.

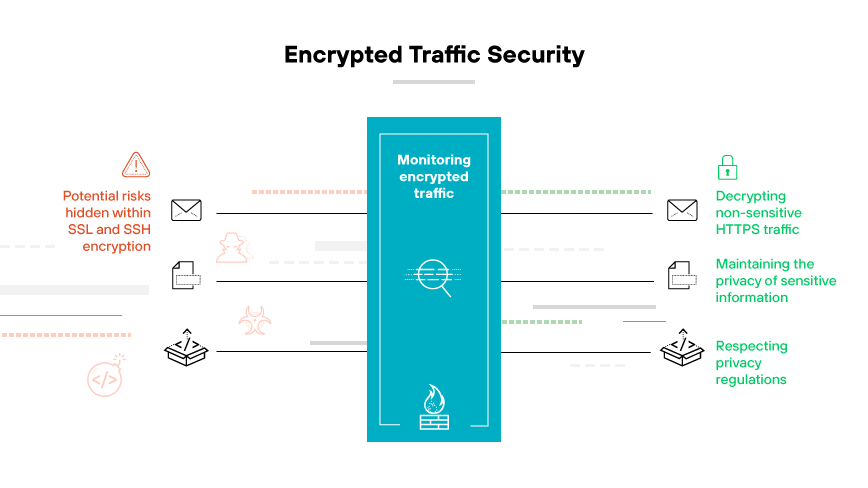
Encrypted Traffic Inspection The fast mode spoke to ivan shefrin, executive director of comcast business managed security services on new encryption technologies and their impact on today's networks. Discover how encryption impacts cloud application speed. learn to balance data protection with performance, explore algorithm choices, and find solutions for secure, responsive cloud services. As a result, there is a fundamental need for methodologies based on intelligent analysis of patterns and attributes of encrypted network traffic. to satisfy security requirements in such a context, we propose an application of deep learning models for enhanced intrusion detection systems (ids). Abstract t ical role in fighting against the abuse by encrypted network trafic. unfortunately, operating a tls middlebox often in curs a huge computational overhead as it mu t translate and relay encrypted trafic from one endpoint to the other. we observe that even a simple t. Explore how next generation firewalls inspect encrypted traffic efficiently, balancing deep security with minimal performance impact. The proposed system dynamically selects and adjusts encryption methods and key strengths based on data sensitivity and the communication context, ensuring a balance between security and.
Comments are closed.