Avoiding Text Message Phishing Scams

Thousands Of Messages Shed Light On Texting Scams Futurity Scammers use email or text messages to trick you into giving them your personal and financial information. but there are several ways to protect yourself. Smishing is like phishing, except it’s sent to your phone. learn what smishing is and how to avoid scams!.

Phishing Scams 6 Best Tips For Phishing Protection Learn how to spot a text message scam before it compromises your identity or worse. all of our content is written by humans, not robots. when we get a text message to our phone, we don’t read it with the same level of scrutiny as an email. That’s exactly why scammers love them. text based scams (often called “smishing”) are one of the fastest growing ways attackers try to get your information, your passwords, or your money. and they work – largely because they catch people off guard. let’s break down what these scams look like, how they work, and how to shut them down. Learn how to avoid smishing attacks with practical tips to recognize fake texts, and protect sensitive information. stay safe from scams targeting individuals and businesses. Learn how to recognize and avoid phishing scams. discover common phishing tactics, red flags, and how trend micro scamcheck’s ai powered anti scam app can protect you from email, sms, and voice phishing.

Recognizing And Avoiding Text Phishing Scams Learn how to avoid smishing attacks with practical tips to recognize fake texts, and protect sensitive information. stay safe from scams targeting individuals and businesses. Learn how to recognize and avoid phishing scams. discover common phishing tactics, red flags, and how trend micro scamcheck’s ai powered anti scam app can protect you from email, sms, and voice phishing. Learn how to protect yourself from phone text scams (smishing) with essential tips and key points to safeguard your personal information. Never click links, reply to text messages or call numbers you don't recognize. do not respond, even if the message requests that you "text stop" to end messages. delete all suspicious texts. make sure your smart device os and security apps are updated to the latest version. To prevent phishing scams, always double check urls, enable two factor authentication, use antivirus software, and ignore suspicious emails. if you fall for a phishing scam, act quickly by changing your passwords, contacting your bank, and reporting the scam to authorities. Learn how to protect yourself from text message fraud, also known as smishing. discover tips to spot scams, avoid malicious links, and safeguard your personal information from cybercriminals.
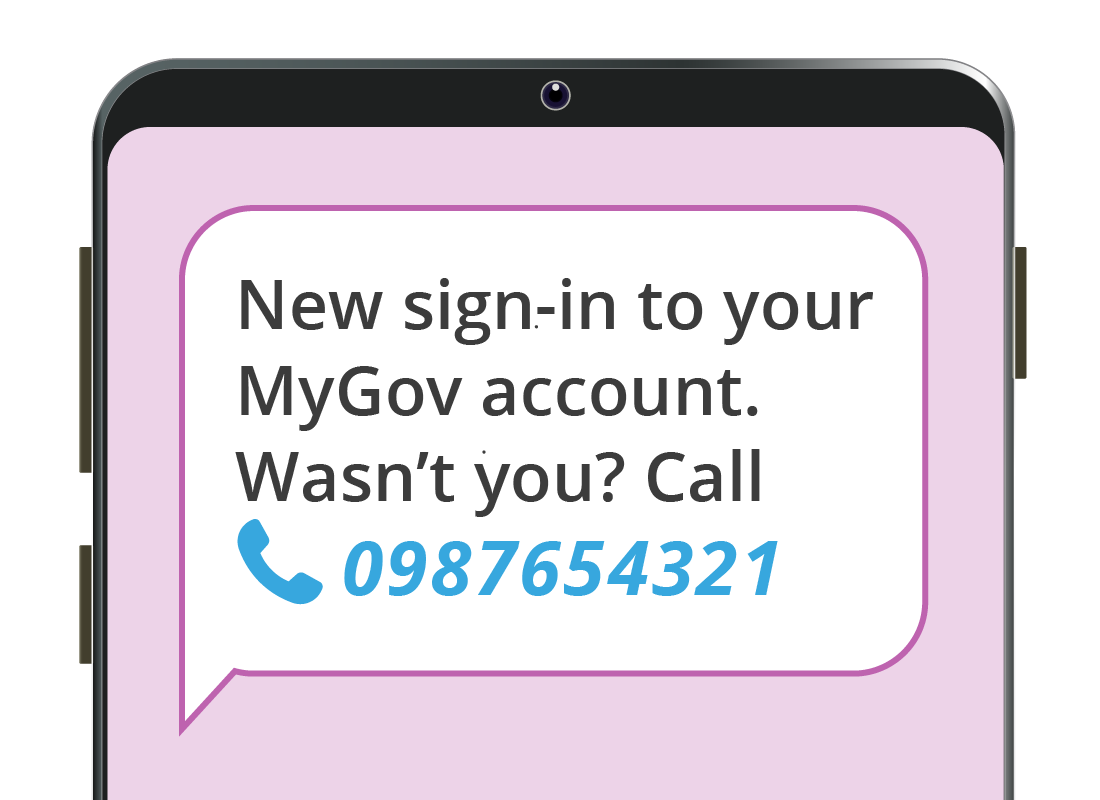
How To Identify A Phishing Scam Learning Module Phishing Scams Learn how to protect yourself from phone text scams (smishing) with essential tips and key points to safeguard your personal information. Never click links, reply to text messages or call numbers you don't recognize. do not respond, even if the message requests that you "text stop" to end messages. delete all suspicious texts. make sure your smart device os and security apps are updated to the latest version. To prevent phishing scams, always double check urls, enable two factor authentication, use antivirus software, and ignore suspicious emails. if you fall for a phishing scam, act quickly by changing your passwords, contacting your bank, and reporting the scam to authorities. Learn how to protect yourself from text message fraud, also known as smishing. discover tips to spot scams, avoid malicious links, and safeguard your personal information from cybercriminals.

11 Ways Of How To Avoid Text Message Scams Anyclaims To prevent phishing scams, always double check urls, enable two factor authentication, use antivirus software, and ignore suspicious emails. if you fall for a phishing scam, act quickly by changing your passwords, contacting your bank, and reporting the scam to authorities. Learn how to protect yourself from text message fraud, also known as smishing. discover tips to spot scams, avoid malicious links, and safeguard your personal information from cybercriminals.
Comments are closed.