Avoid These Cryptography Mistakes In Informatics

Avoid These Cryptography Mistakes In Informatics Learn how to secure your informatics data with cryptography and avoid common mistakes and pitfalls, such as using weak algorithms, misconfiguring tools, and ignoring key management. This article provides a detailed exploration of cryptographic failures, their causes, types, real world examples, and strategies to prevent them. understanding cryptographic failures.

Avoid Making These Cybersecurity Mistakes Bca Identify which data is sensitive according to privacy laws, regulatory requirements, or business needs. store your most sensitive keys in a hardware or cloud based hsm. use well trusted implementations of cryptographic algorithms whenever possible. don't store sensitive data unnecessarily. Our application security and data are directly affected when our algorithms fail, keys are exposed, or poor key management, protocols, or implementations are used incorrectly. we fail to properly protect transmitted or stored data. when it fails, it really fails. By understanding the differences between design flaws and implementation mistakes, and by following best practices when designing and implementing cryptographic systems, we can avoid the consequences of failure and ensure the security of our data and systems. Cryptographic failures (previously called “sensitive data exposure” in the owasp top ten) refer to vulnerabilities that occur due to the incorrect implementation, configuration, or use of.
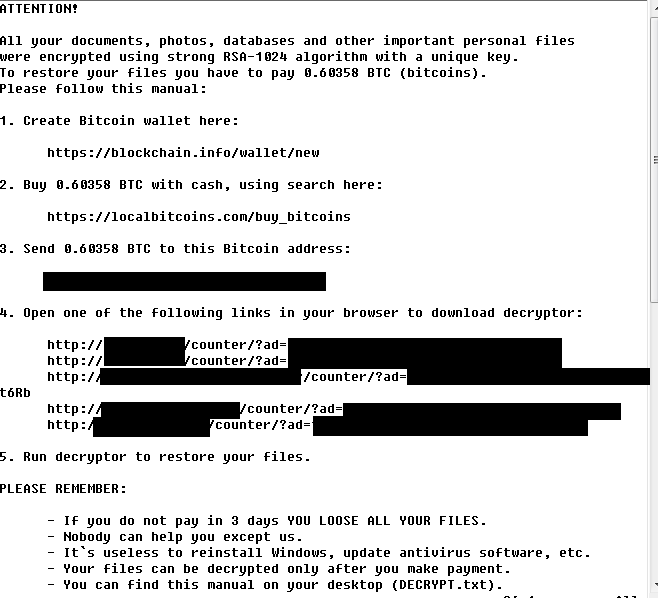
Virus Bulletin Vb2016 Preview Cryptography Mistakes In Malware By understanding the differences between design flaws and implementation mistakes, and by following best practices when designing and implementing cryptographic systems, we can avoid the consequences of failure and ensure the security of our data and systems. Cryptographic failures (previously called “sensitive data exposure” in the owasp top ten) refer to vulnerabilities that occur due to the incorrect implementation, configuration, or use of. Learn what cryptographic failures are, see real world examples, and get owasp best practices to secure data in transit & at rest. Learn what cryptographic failures are, why they expose sensitive data, and how to avoid weak encryption in your apps. The most common cryptography mistakes developers make — using encryption for password storage, outdated algorithms, skipping authenticated encryption, hardcoded keys, and more. practical explanations and safer alternatives for each. Cryptographic failures occur when applications, systems, or teams fail to protect sensitive data properly using cryptography — either by not using it where needed, using it incorrectly, or mishandling keys and related secrets.
Understanding Cryptography Types Techniques And Countermeasures For Learn what cryptographic failures are, see real world examples, and get owasp best practices to secure data in transit & at rest. Learn what cryptographic failures are, why they expose sensitive data, and how to avoid weak encryption in your apps. The most common cryptography mistakes developers make — using encryption for password storage, outdated algorithms, skipping authenticated encryption, hardcoded keys, and more. practical explanations and safer alternatives for each. Cryptographic failures occur when applications, systems, or teams fail to protect sensitive data properly using cryptography — either by not using it where needed, using it incorrectly, or mishandling keys and related secrets.
Comments are closed.