Avoid Malware Scanners That Use Insecure Hashing
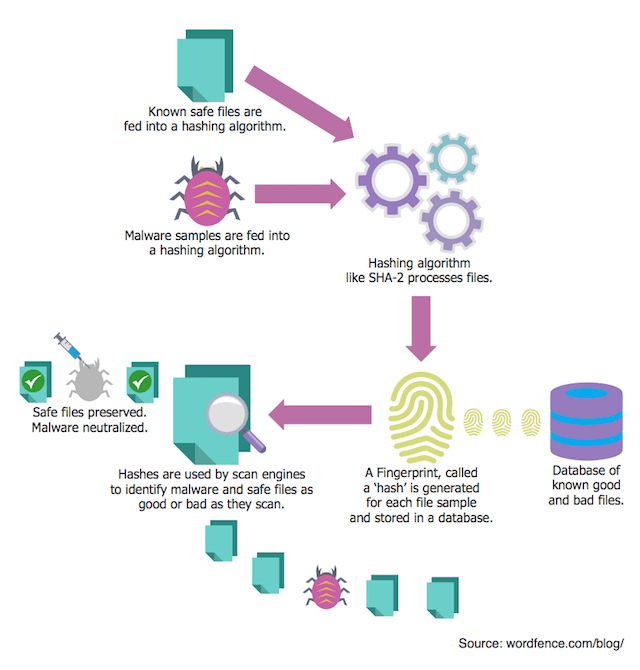
Avoid Malware Scanners That Use Insecure Hashing Eworldlinx This issue may allow an attacker to hide malware that is undetectable to scanners using the md5 hashing algorithm. below i will explain how hashes are used in the security industry, what the problem is and how to solve it. Several popular security products in the wordpress space use md5 to verify safe files and detect malicious files. using this weak hashing algorithm creates a security hole that an attacker can use to craft malware that avoids detection by these scanners.
Avoid Malware Scanners That Use Insecure Hashing Md5 and sha 1 are cryptographically broken and vulnerable to collision attacks. learn why these hashing algorithms are unsafe and what secure alternatives to use. This issue may allow an attacker to hide malware that is undetectable to scanners using the md5 hashing algorithm. below i will explain how hashes are used in the security industry, what the problem is and how to solve it. i’ll also point you to research demonstrating this issue and further reading. Many scanning systems make use of perceptual hash functions, which have several features that make them ideal for identifying pictures. most importantly, they are resilient to small changes in the image content, such as re encoding or changing the size of an image. Even if high grade ciphers are today supported and normally used, some misconfiguration in the server can be used to force the use of a weak cipher or at worst no encryption permitting to an attacker to gain access to the supposed secure communication channel.
Avoid Malware Scanners That Use Insecure Hashing Many scanning systems make use of perceptual hash functions, which have several features that make them ideal for identifying pictures. most importantly, they are resilient to small changes in the image content, such as re encoding or changing the size of an image. Even if high grade ciphers are today supported and normally used, some misconfiguration in the server can be used to force the use of a weak cipher or at worst no encryption permitting to an attacker to gain access to the supposed secure communication channel. When it comes to password security, using the right hashing algorithm is critical. while md5 and sha are outdated and insecure, modern algorithms like scrypt and bcrypt provide robust protection against brute force and rainbow table attacks. In this post i’m going to discuss a major problem that exists with several wordpress malware scanners: the use of weak hashing algorithms for good and bad file identification. While traditional hash based detection methods have limitations, yara rules offer a powerful way to identify and categorize different malware variants. by creating your custom yara rules, you can shield your organization from these evolving threats. Effective methods include using strong hash functions (e.g., sha 256), enforcing minimum key lengths, adopting secure protocols, and implementing secure coding standards that mandate strong encryption algorithms.
Avoid Malware Scanners That Use Insecure Hashing When it comes to password security, using the right hashing algorithm is critical. while md5 and sha are outdated and insecure, modern algorithms like scrypt and bcrypt provide robust protection against brute force and rainbow table attacks. In this post i’m going to discuss a major problem that exists with several wordpress malware scanners: the use of weak hashing algorithms for good and bad file identification. While traditional hash based detection methods have limitations, yara rules offer a powerful way to identify and categorize different malware variants. by creating your custom yara rules, you can shield your organization from these evolving threats. Effective methods include using strong hash functions (e.g., sha 256), enforcing minimum key lengths, adopting secure protocols, and implementing secure coding standards that mandate strong encryption algorithms.
Comments are closed.