Automated Static Application Security Testing Sast With Semgrep Using Github Actions

Understanding Semgrep A Powerful Open Source Sast Tool For Developers This repository contains an example workflow showcasing the integration of semgrep, a powerful static analysis tool, within a github actions workflow for performing static application security testing (sast). We’ll dive into the benefits of using semgrep as a static analysis tool, discuss its key features, and most importantly, learn how to integrate it into our github actions workflows.
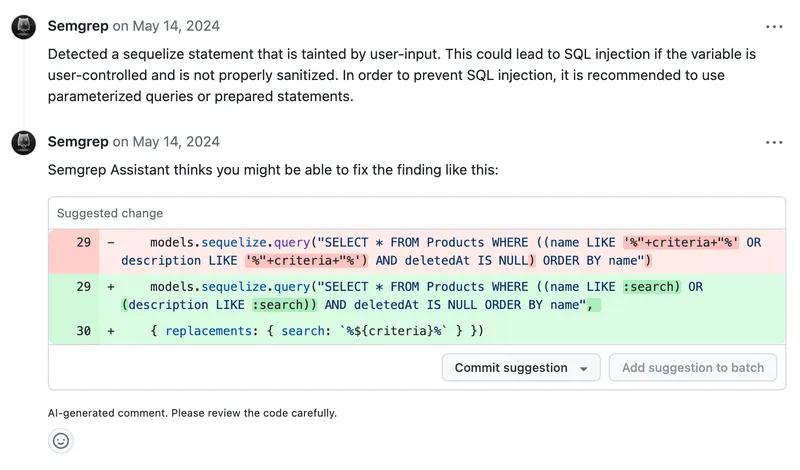
Static Application Security Testing Sast Semgrep 🔍 in this video, we’ll set up static application security testing (sast) with semgrep in github actions to automatically scan your code for vulnerabilities. Set up the semgrep github action for automated code scanning. covers workflow yaml, rulesets, pr comments, sarif upload, custom rules, and caching. This skill facilitates the professional integration of static application security testing (sast) into github ci cd workflows. it guides users through configuring codeql and semgrep to perform automated code scanning on every pull request and push, ensuring that vulnerabilities are identified early in the development lifecycle. What makes a better static application security testing (sast) tool? learn how semgrep code produces fewer false positives for developer friendly workflows.

Static Application Security Testing Sast Semgrep This skill facilitates the professional integration of static application security testing (sast) into github ci cd workflows. it guides users through configuring codeql and semgrep to perform automated code scanning on every pull request and push, ensuring that vulnerabilities are identified early in the development lifecycle. What makes a better static application security testing (sast) tool? learn how semgrep code produces fewer false positives for developer friendly workflows. Learn how teams can leverage the power of github advanced security’s code scanning and github actions to integrate the right security testing tools at the right time. The semgrep analyzer performs static application security testing (sast) scanning on repositories. it supports 30 languages. we developed an analyzer that wraps semgrep to integrate with code secure. semgrep severify filter (semgrep severity). option: info, warning, error. semgrep app token. see more here. scan with pro engine. Over the past few days, i’ve been diving deep into static application security testing (sast) – setting up a complete environment on kali linux to automatically detect vulnerabilities in code. Since this is our first time adopting sast, we started with a learning focused trial using the free semgrep community edition.

Static Application Security Testing Sast Semgrep Learn how teams can leverage the power of github advanced security’s code scanning and github actions to integrate the right security testing tools at the right time. The semgrep analyzer performs static application security testing (sast) scanning on repositories. it supports 30 languages. we developed an analyzer that wraps semgrep to integrate with code secure. semgrep severify filter (semgrep severity). option: info, warning, error. semgrep app token. see more here. scan with pro engine. Over the past few days, i’ve been diving deep into static application security testing (sast) – setting up a complete environment on kali linux to automatically detect vulnerabilities in code. Since this is our first time adopting sast, we started with a learning focused trial using the free semgrep community edition.
Comments are closed.