Automated Security And Zero Trust
A Complete Suite Of Zero Trust Security Tools To Help Get The Most From Ai This guide will walk you through the steps required to manage visibility, automation, and orchestration following the principles of a zero trust security framework. This guidance contains an abstract definition of zero trust architecture (zta) and gives general deployment models and use cases where zero trust could improve an enterprise’s overall information technology security posture.

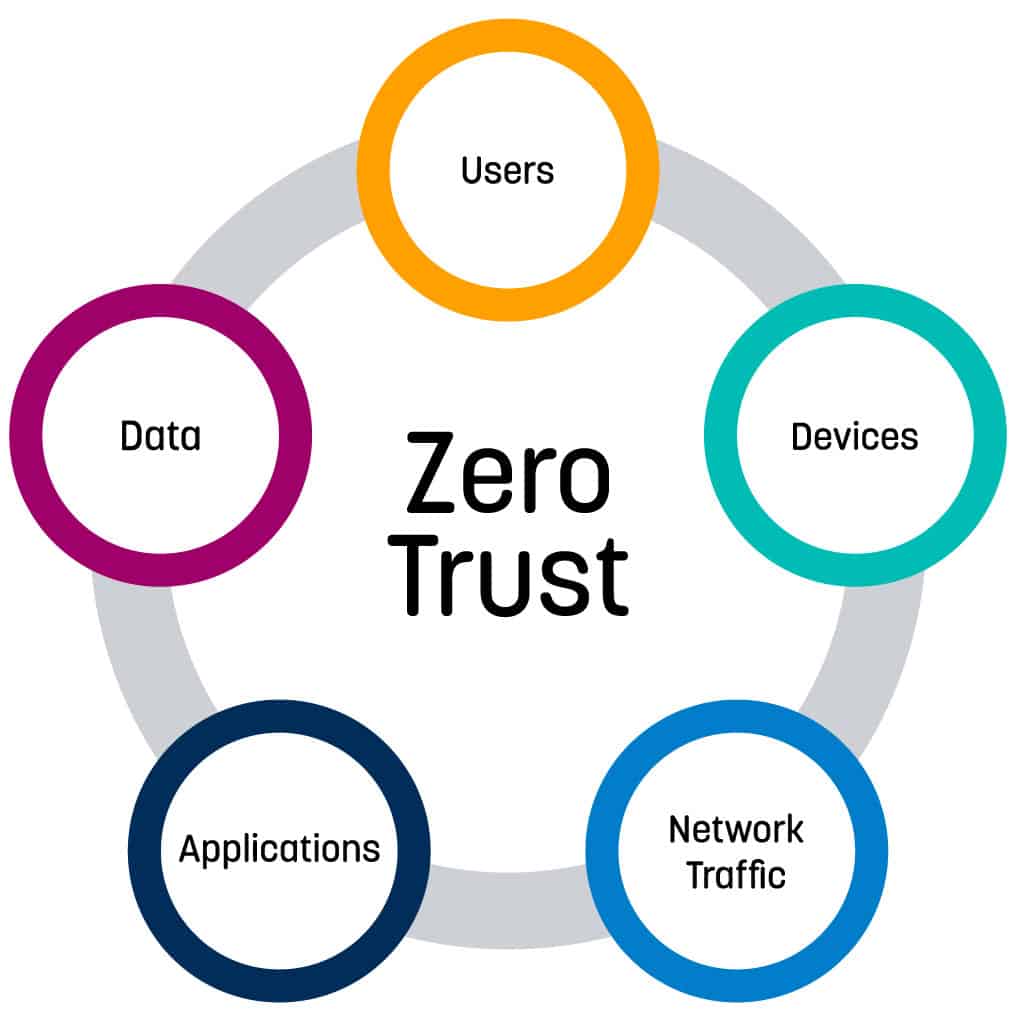
Automated Security And Zero Trust That’s where automated zero trust security comes in, ensuring consistent protection without relying on human oversight. by combining automation with the principles of zero trust, businesses can eliminate blind spots and respond to threats in real time. Interactive planning tool zero trust workshop a new web application to plan your zero trust deployment across all seven pillars — identity, devices, data, network, infrastructure, security operations, and ai. prioritize tasks in a first then structure and generate automated summaries and implementation plans. Automation is the key to making zero trust work at scale. without automated security controls, organizations would be overwhelmed by manual access approvals and threat responses. in this article, we’ll explore how zero trust and automation work together to enforce security policies, mitigate threats, and protect enterprise systems. This article explores the synergy between ai and zero trust, highlighting how ai driven technologies can enhance identity verification, behavioral analytics, access control, and anomaly.

Zero Trust Security A Complete Guide Automation is the key to making zero trust work at scale. without automated security controls, organizations would be overwhelmed by manual access approvals and threat responses. in this article, we’ll explore how zero trust and automation work together to enforce security policies, mitigate threats, and protect enterprise systems. This article explores the synergy between ai and zero trust, highlighting how ai driven technologies can enhance identity verification, behavioral analytics, access control, and anomaly. This publication provides an in depth breakdown of the key principles and technologies associated with zero trust visibility, analytics, orchestration, and automation. it provides practical guidance for integrating these capabilities into an organization’s security infrastructure. Learn how zero trust principles can secure ai agents, prevent misuse, and protect data in autonomous systems without slowing innovation. Deloitte’s zero trust access managed service combines proprietary technology, domain experience, and industry insights to provide a powerful approach that accelerates zero trust adoption with greater efficiency, security, and value. Without automated capabilities, organizations face an impossible choice: either compromise on zero trust principles or accept unsustainable operational overhead. the solution lies in building automation directly into the foundation of your zero trust architecture from day one.

Implementing Zero Trust Security A Guide For Modern Businesses This publication provides an in depth breakdown of the key principles and technologies associated with zero trust visibility, analytics, orchestration, and automation. it provides practical guidance for integrating these capabilities into an organization’s security infrastructure. Learn how zero trust principles can secure ai agents, prevent misuse, and protect data in autonomous systems without slowing innovation. Deloitte’s zero trust access managed service combines proprietary technology, domain experience, and industry insights to provide a powerful approach that accelerates zero trust adoption with greater efficiency, security, and value. Without automated capabilities, organizations face an impossible choice: either compromise on zero trust principles or accept unsustainable operational overhead. the solution lies in building automation directly into the foundation of your zero trust architecture from day one.
Embracing A Zero Trust Security Model Logrhythm Deloitte’s zero trust access managed service combines proprietary technology, domain experience, and industry insights to provide a powerful approach that accelerates zero trust adoption with greater efficiency, security, and value. Without automated capabilities, organizations face an impossible choice: either compromise on zero trust principles or accept unsustainable operational overhead. the solution lies in building automation directly into the foundation of your zero trust architecture from day one.
Comments are closed.