Authentication Vs Authorization Understanding The Difference
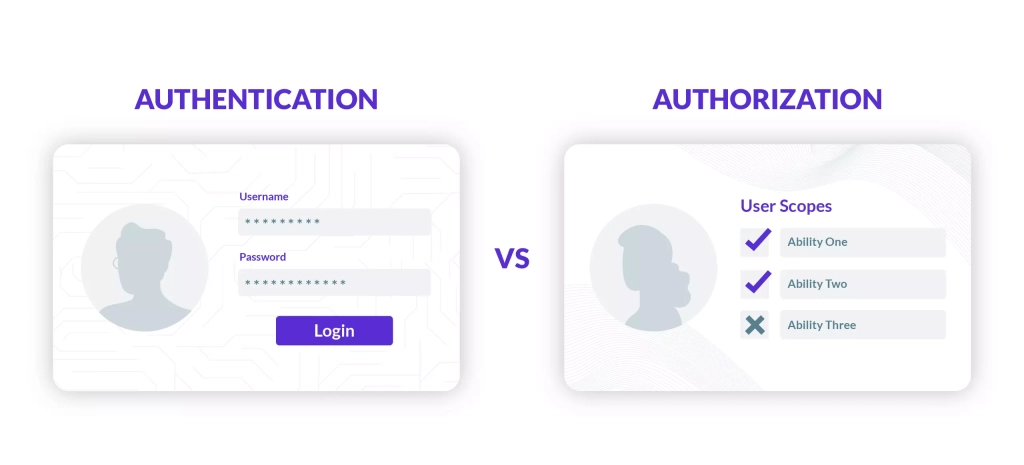
Understanding The Difference Authentication Vs Authorization Authentication and authorization are key security steps that ensure only the right users access a system and can perform permitted actions. authentication verifies who you are, and authorization determines what you can do. This article will help you understand what authentication and authorization are, and how to differentiate between these two important aspects of application security.
Authentication Vs Authorization Differences Best Practices Learn the key differences authentication vs authorization, and how both are essential for secure systems and data protection in your business. Authentication verifies a user’s identity. authorization gives the user the right level of access to system resources. the authentication process relies on credentials, such as passwords or fingerprint scans, that users present to prove they are who they claim to be. Understanding authentication and authorization is crucial for building secure, user friendly systems. authentication ensures users are who they say they are, while authorization ensures they can only do what they’re allowed to. Authentication ensures that users are who they claim to be, while authorization ensures they can only access what they're permitted to see or do. understanding these concepts and implementing them correctly is fundamental to identity and access management.

Authentication Vs Authorization What S The Difference Understanding authentication and authorization is crucial for building secure, user friendly systems. authentication ensures users are who they say they are, while authorization ensures they can only do what they’re allowed to. Authentication ensures that users are who they claim to be, while authorization ensures they can only access what they're permitted to see or do. understanding these concepts and implementing them correctly is fundamental to identity and access management. Authentication establishes who you are, while authorization dictates what you are allowed to do once your identity is confirmed. together, they form the foundation of access control and data security in the digital world. Authentication ensures that users are who they claim to be, while authorization ensures they can only access what they’re permitted to see or do. understanding these concepts and implementing them correctly is fundamental to identity and access management. Authentication confirms your identity by validating who you are, while authorization controls your access by determining what you can see and do. authentication usually requires a username and password. authorization may limit system access and feature rights based on user type or permissions level. Authentication vs authorization: what's the difference? authentication and authorization are often mentioned together, yet they solve very different security problems. this guide breaks down authentication vs authorization with clear definitions, technical workflows, and real world iam examples.

Authentication Vs Authorization Understanding The Difference Authentication establishes who you are, while authorization dictates what you are allowed to do once your identity is confirmed. together, they form the foundation of access control and data security in the digital world. Authentication ensures that users are who they claim to be, while authorization ensures they can only access what they’re permitted to see or do. understanding these concepts and implementing them correctly is fundamental to identity and access management. Authentication confirms your identity by validating who you are, while authorization controls your access by determining what you can see and do. authentication usually requires a username and password. authorization may limit system access and feature rights based on user type or permissions level. Authentication vs authorization: what's the difference? authentication and authorization are often mentioned together, yet they solve very different security problems. this guide breaks down authentication vs authorization with clear definitions, technical workflows, and real world iam examples.
Comments are closed.