Authentication Method In Web Api Part 31

9 Popular Api Authentication Methods To Secure Api In this video, you will learn about different authentication methods used in web apis. authentication is the process of verifying the identity of a user before allowing access to resources. In this series of articles, we'll look at some options for securing a web api from unauthorized users. this series will cover both authentication and authorization.
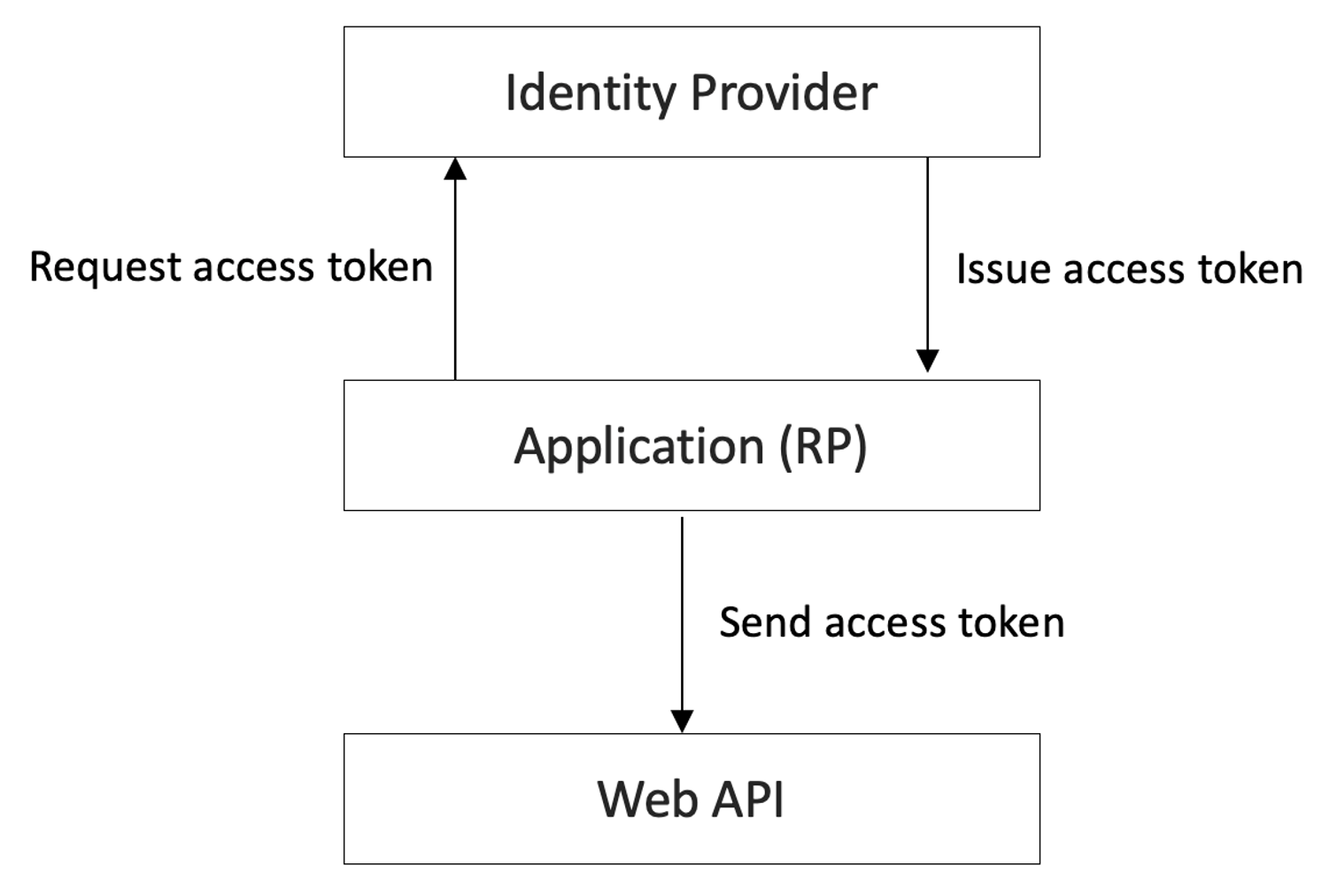
Web Api Authentication The web authentication api (webauthn) is an extension of the credential management api that enables strong authentication with public key cryptography, enabling passwordless authentication and secure multi factor authentication (mfa) without sms texts. For the web authentication specification to move beyond candidate recommendation we must show two browser implementations supporting the new features and extensions. the spec will be run through the level 3 on the web platform tests. Therefore, a clear understanding of the available rest api authentication methods is essential for developers, founders, and product teams alike. this guide provides a comprehensive breakdown of seven primary authentication methods, designed to help you make an informed choice. Authentication in a web api using json web tokens (jwt) is a common approach to securing apis. jwts are compact, url safe tokens that can be used for securely transmitting information.
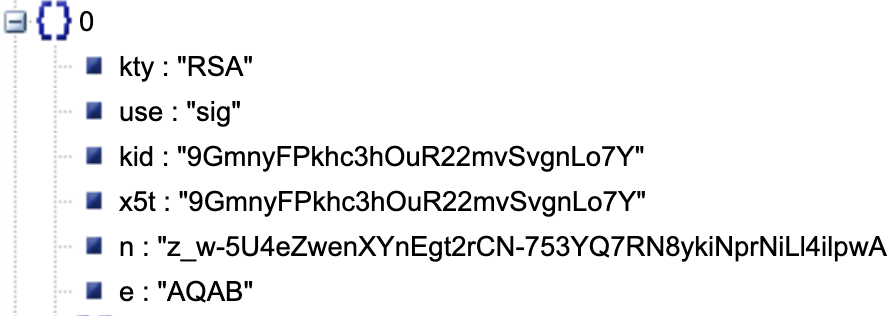
Web Api Authentication Therefore, a clear understanding of the available rest api authentication methods is essential for developers, founders, and product teams alike. this guide provides a comprehensive breakdown of seven primary authentication methods, designed to help you make an informed choice. Authentication in a web api using json web tokens (jwt) is a common approach to securing apis. jwts are compact, url safe tokens that can be used for securely transmitting information. This article will take you through the api authentication approaches, such as oauth 2.0, api keys, jwt (json web tokens), basic authentication, tls authentication, and openid connect (oidc). Authentication and authorization are critical to building secure web applications, including asp web api applications. authentication is the process of verifying the identity of a user. Your authentication service issues a jwt token that is signed using a secret that is also available in your api service. the reason they need to be there too is that you will need to verify the tokens received to make sure you created them. Learn how api authentication works in practice, from basic auth and api keys to bearer tokens and oauth 2.0, and when to use each method in your apis.
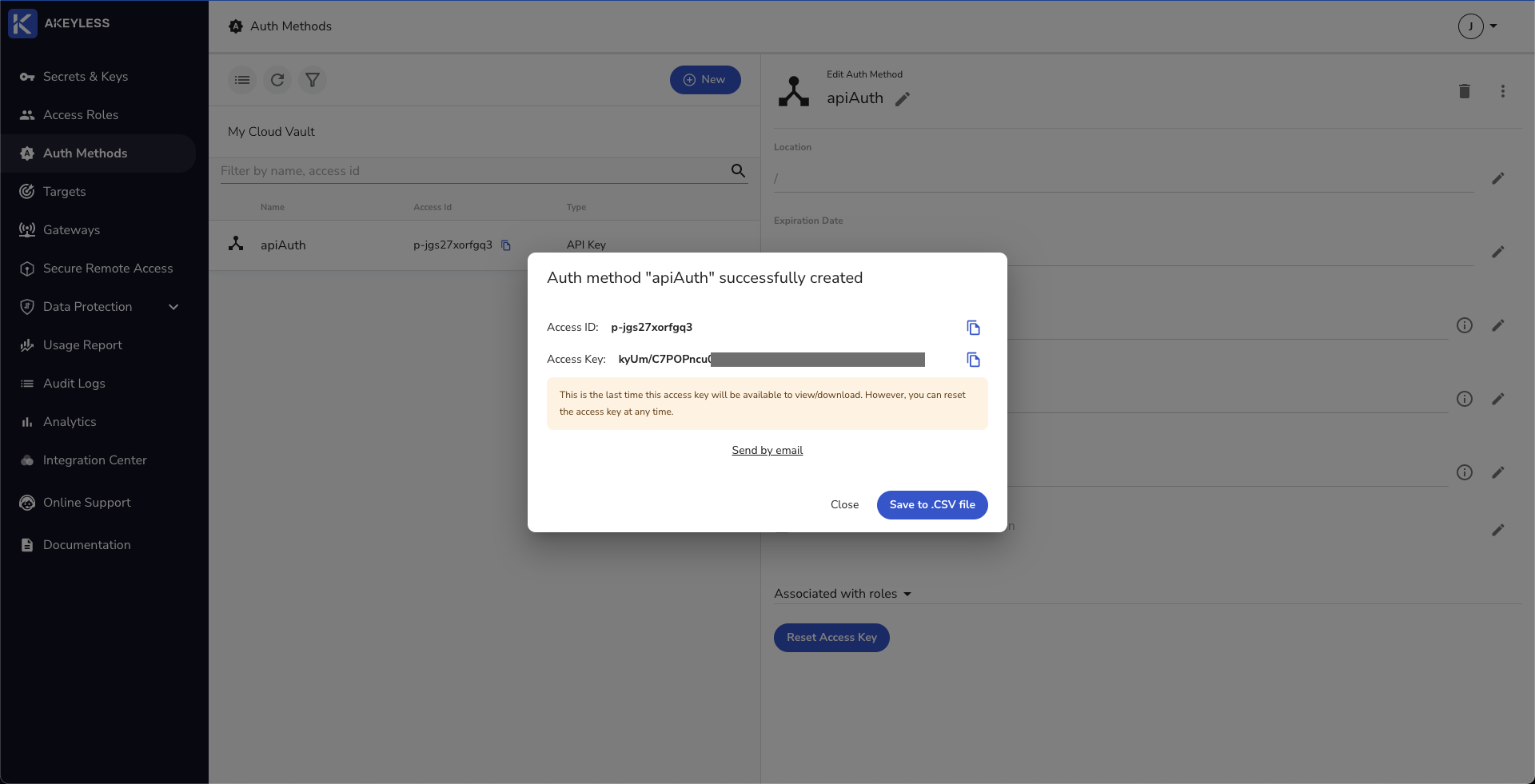
Authentication Methods This article will take you through the api authentication approaches, such as oauth 2.0, api keys, jwt (json web tokens), basic authentication, tls authentication, and openid connect (oidc). Authentication and authorization are critical to building secure web applications, including asp web api applications. authentication is the process of verifying the identity of a user. Your authentication service issues a jwt token that is signed using a secret that is also available in your api service. the reason they need to be there too is that you will need to verify the tokens received to make sure you created them. Learn how api authentication works in practice, from basic auth and api keys to bearer tokens and oauth 2.0, and when to use each method in your apis.
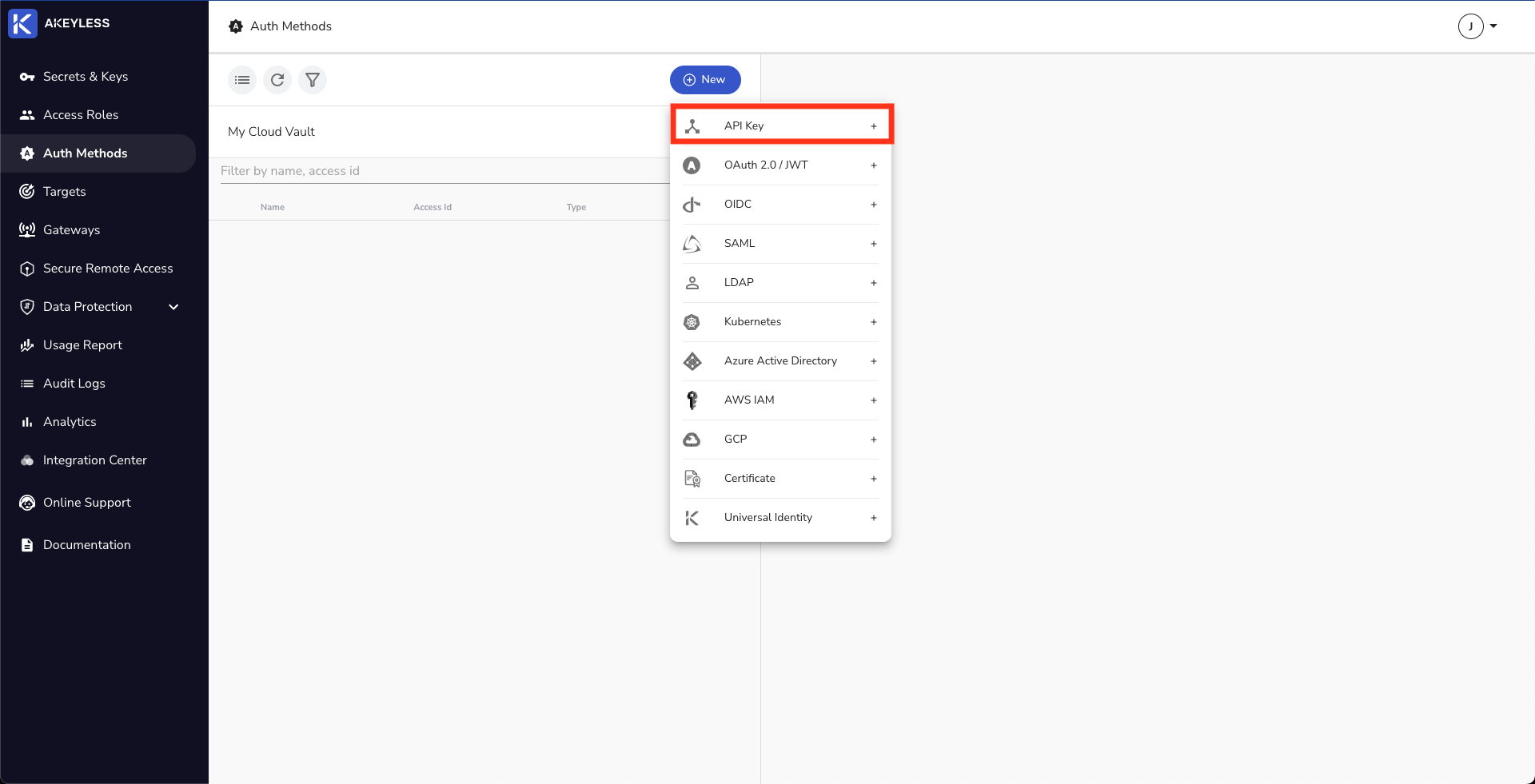
Authentication Methods Your authentication service issues a jwt token that is signed using a secret that is also available in your api service. the reason they need to be there too is that you will need to verify the tokens received to make sure you created them. Learn how api authentication works in practice, from basic auth and api keys to bearer tokens and oauth 2.0, and when to use each method in your apis.

9 Popular Api Authentication Methods To Secure Api
Comments are closed.