Authentication Header
301 Moved Permanently The http authorization request header can be used to provide credentials that authenticate a user agent with a server, allowing access to protected resources. When a client requests a protected resource without valid credentials, the server responds with 401 and includes one or more challenges in the www authenticate header. each challenge names an authentication scheme and provides parameters the client needs to construct credentials.
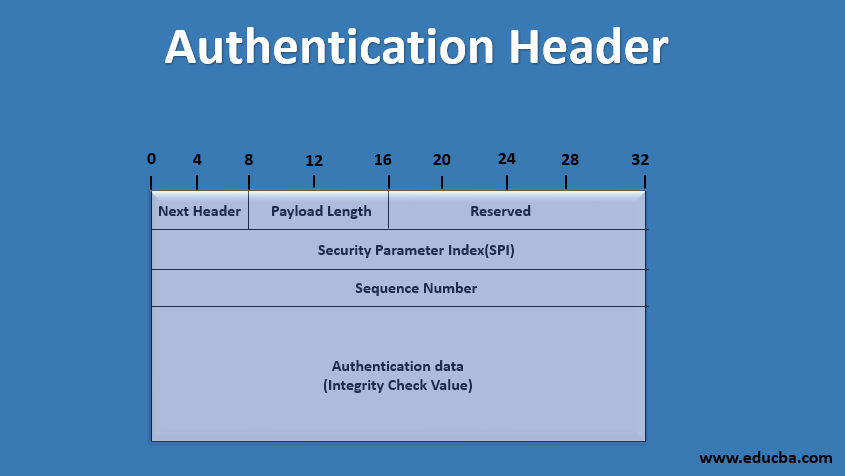
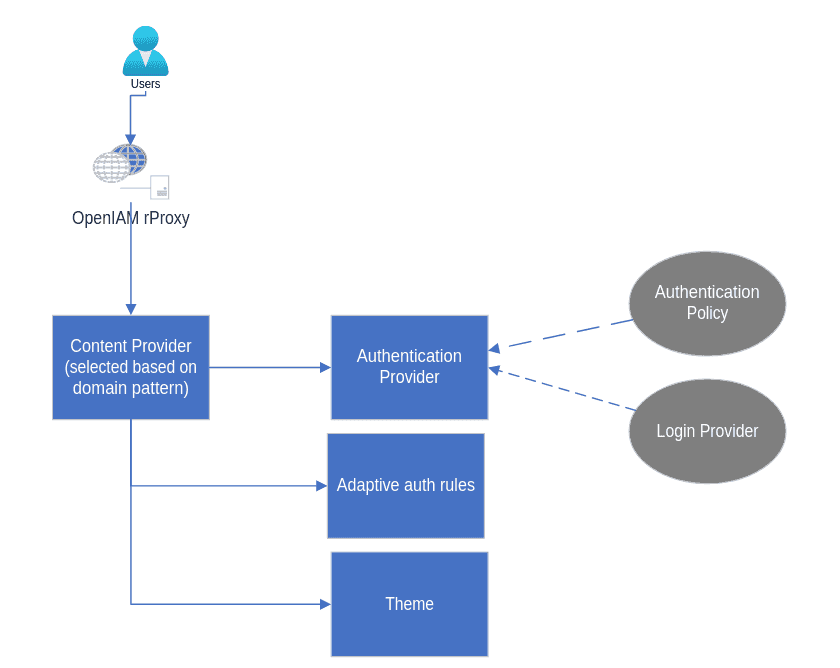
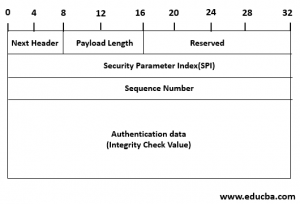
Authentication Header What Is Authentication Header 6 Formats What is an authentication header? the authentication header (ah) is a security protocol used within the ipsec suite. its primary function is to ensure that the message remains unmodified during transmission from the source and it confirms that the data originates from the expected source. The authorization header is an http header used to transmit credentials or tokens that authenticate a user, service, or application. it tells the server who is making the request and provides the credentials needed to verify access. Learn how to use http authorization header to access apis securely and efficiently, and how to handle common errors and challenges with it. Generate http request headers instantly. configure bearer token, api key, basic auth, content type, cache control, security headers, and custom headers. copy as raw.
Authentication Header What Is Authentication Header 6 Formats Learn how to use http authorization header to access apis securely and efficiently, and how to handle common errors and challenges with it. Generate http request headers instantly. configure bearer token, api key, basic auth, content type, cache control, security headers, and custom headers. copy as raw. The authorization header builder helps you construct correct authorization (and related) header values for basic, bearer, digest, and sometimes other schemes. you enter credentials or tokens and get the exact header string to use, with optional base64 or hash steps explained. use it to test api authentication, to debug "401 unauthorized" or "403 forbidden" when the issue is a malformed header. Generate an authorization header for http basic auth using a username and password. learn how basic auth works and how to use it with debugbear, a website performance monitoring tool. I realize this post is long dead, but i just want to point out in case you're not aware that by posting your authorization: header, you've essentially posted your password in the clear. Authorization headers are http headers that carry authentication credentials or tokens to authorize and validate requests. they provide a way to prove that the requester has the necessary permissions to access protected resources.
Basic Authentication Header Generator The authorization header builder helps you construct correct authorization (and related) header values for basic, bearer, digest, and sometimes other schemes. you enter credentials or tokens and get the exact header string to use, with optional base64 or hash steps explained. use it to test api authentication, to debug "401 unauthorized" or "403 forbidden" when the issue is a malformed header. Generate an authorization header for http basic auth using a username and password. learn how basic auth works and how to use it with debugbear, a website performance monitoring tool. I realize this post is long dead, but i just want to point out in case you're not aware that by posting your authorization: header, you've essentially posted your password in the clear. Authorization headers are http headers that carry authentication credentials or tokens to authorize and validate requests. they provide a way to prove that the requester has the necessary permissions to access protected resources.
Comments are closed.