Authentication Explained Simply Jwt Vs Oauth Vs Api Keys Vs Sso

Api Authentication Jwt Vs Oauth Vs Api Keys Daniel Martínez Vázquez In this article, we will take a deep dive into five common authentication methods: basic authentication, bearer tokens, oauth2, jwt, and sso. we will cover how they work, their advantages and disadvantages, and when to use each. In this post, we’ll explore the differences between jwt, oauth2, and api keys, how they work, real world examples, and guidance on choosing the right one for your project.
Api Authentication Methods Explained Api Keys Oauth Jwt Hmac A deep dive comparing api keys, oauth 2.0, jwt, and hmac for ctos. learn which api authentication method fits your enterprise sso and iam strategy. Understand when to use api keys, oauth tokens, and jwt for different api types. learn about their security implications and how they impact user experience. Choose your authentication method based on your use case. api keys work well for developer apis, jwt is great for modern web mobile apps, and oauth 2.0 is essential when third party access is needed. That’s where things like basic auth, bearer tokens, oauth2, jwt, and sso come in. let’s break them down in a way that makes sense for developers who want to ship securely without.
Jwt Vs Oauth2 Vs Api Keys Choosing The Right Authentication Strategy Choose your authentication method based on your use case. api keys work well for developer apis, jwt is great for modern web mobile apps, and oauth 2.0 is essential when third party access is needed. That’s where things like basic auth, bearer tokens, oauth2, jwt, and sso come in. let’s break them down in a way that makes sense for developers who want to ship securely without. A: use oauth 2.0 for user authentication in web applications, jwt for stateless token management, and api keys for simple service to service communication. choose based on your security requirements and complexity tolerance. Choosing the right api authentication method is critical for security, usability, and scalability. this guide compares major authentication approaches—api keys, oauth 2.0, jwt bearer tokens, basic auth, and mtls—with clear recommendations for when to use each. Explore various api authentication methods, their pros and cons, and find the right fit for your security and scalability needs. Compare api authentication methods — oauth 2.0, api keys, jwt, and mtls. when to use each, security tradeoffs, and implementation guidance updated for 2026.
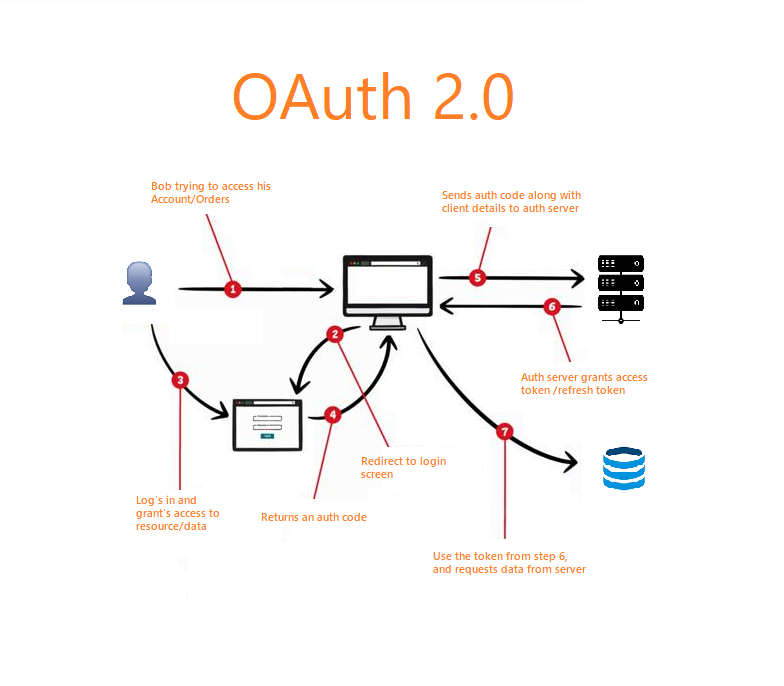
Api Authentication Demystified Mastering Oauth Api Keys And Jwt Like A: use oauth 2.0 for user authentication in web applications, jwt for stateless token management, and api keys for simple service to service communication. choose based on your security requirements and complexity tolerance. Choosing the right api authentication method is critical for security, usability, and scalability. this guide compares major authentication approaches—api keys, oauth 2.0, jwt bearer tokens, basic auth, and mtls—with clear recommendations for when to use each. Explore various api authentication methods, their pros and cons, and find the right fit for your security and scalability needs. Compare api authentication methods — oauth 2.0, api keys, jwt, and mtls. when to use each, security tradeoffs, and implementation guidance updated for 2026.
Api Authentication Demystified Mastering Oauth Api Keys And Jwt Like Explore various api authentication methods, their pros and cons, and find the right fit for your security and scalability needs. Compare api authentication methods — oauth 2.0, api keys, jwt, and mtls. when to use each, security tradeoffs, and implementation guidance updated for 2026.

Mastering Api Authentication Oauth Vs Jwt By Madhu Deepak Infosec
Comments are closed.