Authentication Concepts Stackable Documentation
Authentication Concepts Stackable Documentation Overview of stackable’s user authentication methods and configuration for ldap, oidc, tls, and static providers. Open source authentication that gets you started in minutes. 1. install the sdk. 2. use authentication. for other frameworks or detailed configuration, see the full setup guide. still have questions? check out our faq or join our discord. experimental: ai responses may not always be accurate—please verify important details.
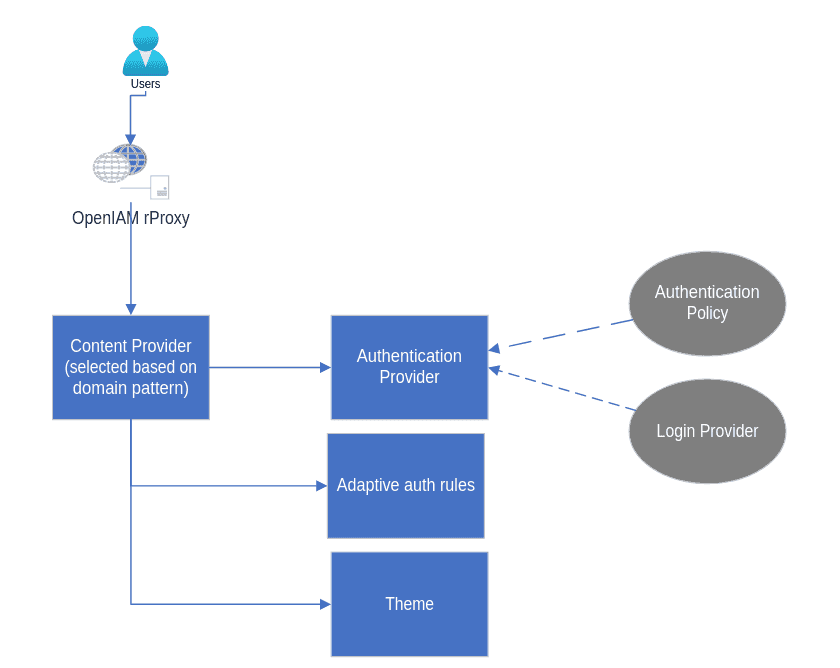
301 Moved Permanently Welcome to the stackable documentation. stackable allows you to model content for websites & apps easily and have this available through a secure modern api. all data is returned in json including errors. Security aspects include authenticating users when services are accessed and subsequently authorizing access to operations and data inside of the services. it also includes tls server verification. the operations section is directed at platform maintainers. Stack auth uses different authentication patterns depending on whether you're making requests from client side code (browser, mobile app) or server side code (your backend). security critical: never expose your secret server key (ssk ) in client side code, browser requests, or any publicly accessible location. For a conceptual overview of authentication on the stackable platform, read the authentication concepts page. the following example shows all possible attributes: the port of the ldap server. if tls is used defaults to 636 otherwise to 389. to learn more, you can follow the authentication with openldap tutorial.
Brand New Documentation Area Stackable Stack auth uses different authentication patterns depending on whether you're making requests from client side code (browser, mobile app) or server side code (your backend). security critical: never expose your secret server key (ssk ) in client side code, browser requests, or any publicly accessible location. For a conceptual overview of authentication on the stackable platform, read the authentication concepts page. the following example shows all possible attributes: the port of the ldap server. if tls is used defaults to 636 otherwise to 389. to learn more, you can follow the authentication with openldap tutorial. If you'd like to build your own version of the stack dashboard (or update project configuration programmatically), you can use the admin access type. for more information, see the concept documentation on stackapp. Stack auth provides a set of components for next.js applications. to get started with stack auth in your next.js application, follow the setup guide. to see the hooks and objects in the next.js sdk, see the sdk reference. Currently it is possible to configure a single form of authentication (of type tls) by adding one (and only one) entry in the authentication sequence as shown in the example below. additional authentication methods, such as kerberos, are not yet supported. The authentication mechanism needs to be configured only in the authenticationclass which is then referenced in the product. multiple different authentication providers are supported. learn more in the authentication concept documentation and the authentication with openldap tutorial.
Comments are closed.