Authentication And Authorization Crtr4u

03b Identification And Authentication Download Free Pdf Password Together, authentication and authorization create a strong security system. by ensuring only verified users can access resources, and then limiting their actions based on permissions, you can protect sensitive data and functionality. Understand the fundamentals of authentication, authorization, and how the microsoft identity platform simplifies these processes for developers.
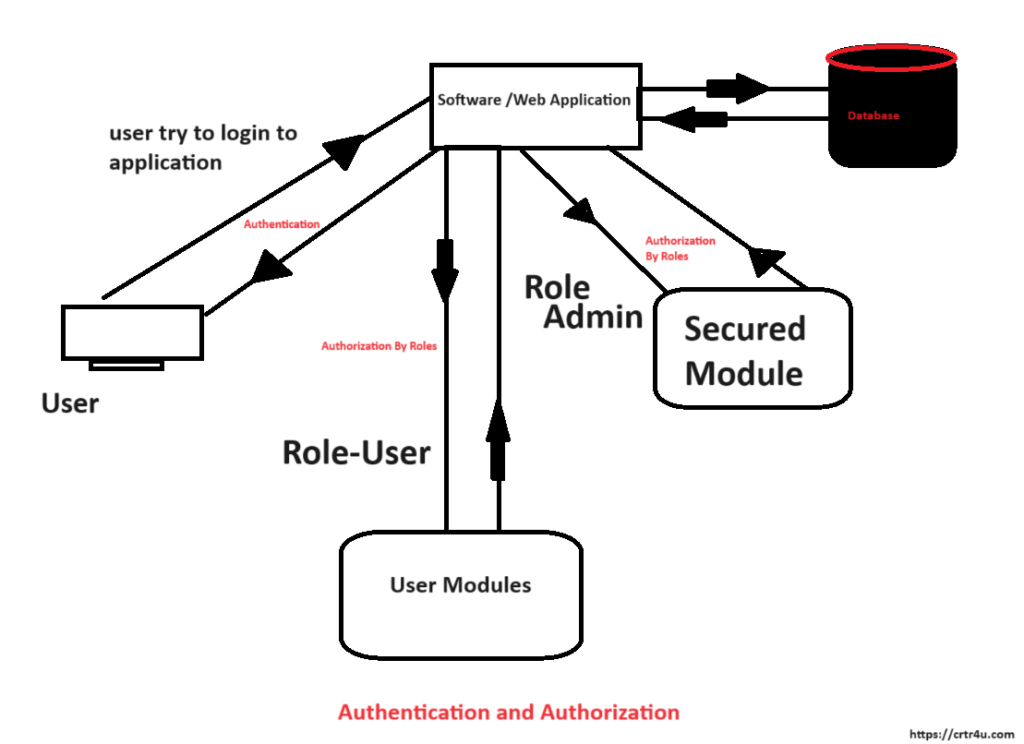
Authentication And Authorization Crtr4u Authentication and authorization are key security steps that ensure only the right users access a system and can perform permitted actions. authentication verifies who you are, and authorization determines what you can do. Authentication confirms identity before allowing access, ensuring only valid users or systems can interact. authorization controls what actions an authenticated user is allowed to perform within the system. timeouts set limits on how long a request waits before failing to prevent hanging processes. Better auth is framework agnostic authentication (and authorization) library for typescript. it provides a comprehensive set of features out of the box and includes a plugin ecosystem that simplifies adding advanced functionalities with minimal code in a short amount of time. whether you need 2fa, multi tenant support, or other complex features. Authentication memastikan bahwa hanya pengguna yang memiliki identitas valid yang dapat mengakses sistem, sementara authorization memastikan bahwa pengguna tersebut memiliki hak akses yang sesuai.

Authentication Vs Authorization What S The Difference Better auth is framework agnostic authentication (and authorization) library for typescript. it provides a comprehensive set of features out of the box and includes a plugin ecosystem that simplifies adding advanced functionalities with minimal code in a short amount of time. whether you need 2fa, multi tenant support, or other complex features. Authentication memastikan bahwa hanya pengguna yang memiliki identitas valid yang dapat mengakses sistem, sementara authorization memastikan bahwa pengguna tersebut memiliki hak akses yang sesuai. Get a 3 legged token with authorization code grant if you need an end user to authorize your app to act on the user’s behalf, please refer this walkthrough. the authorization code grant type is used to obtain both access tokens and refresh tokens and is optimized for confidential clients. Authentication verifies a user’s identity. authorization gives the user the right level of access to system resources. the authentication process relies on credentials, such as passwords or fingerprint scans, that users present to prove they are who they claim to be. Discover the key differences between authorization and authentication and how these two essential security processes keep users safe in the digital landscape. Rest endpoints filled with auth json data, dummyjson provides a free fake rest api with placeholder json data for development, testing, and prototyping. access realistic data quickly for your projects.

Differentiating Authorization And Authentication Stable Diffusion Online Get a 3 legged token with authorization code grant if you need an end user to authorize your app to act on the user’s behalf, please refer this walkthrough. the authorization code grant type is used to obtain both access tokens and refresh tokens and is optimized for confidential clients. Authentication verifies a user’s identity. authorization gives the user the right level of access to system resources. the authentication process relies on credentials, such as passwords or fingerprint scans, that users present to prove they are who they claim to be. Discover the key differences between authorization and authentication and how these two essential security processes keep users safe in the digital landscape. Rest endpoints filled with auth json data, dummyjson provides a free fake rest api with placeholder json data for development, testing, and prototyping. access realistic data quickly for your projects.
Comments are closed.