Attribute Based Security And Messaging

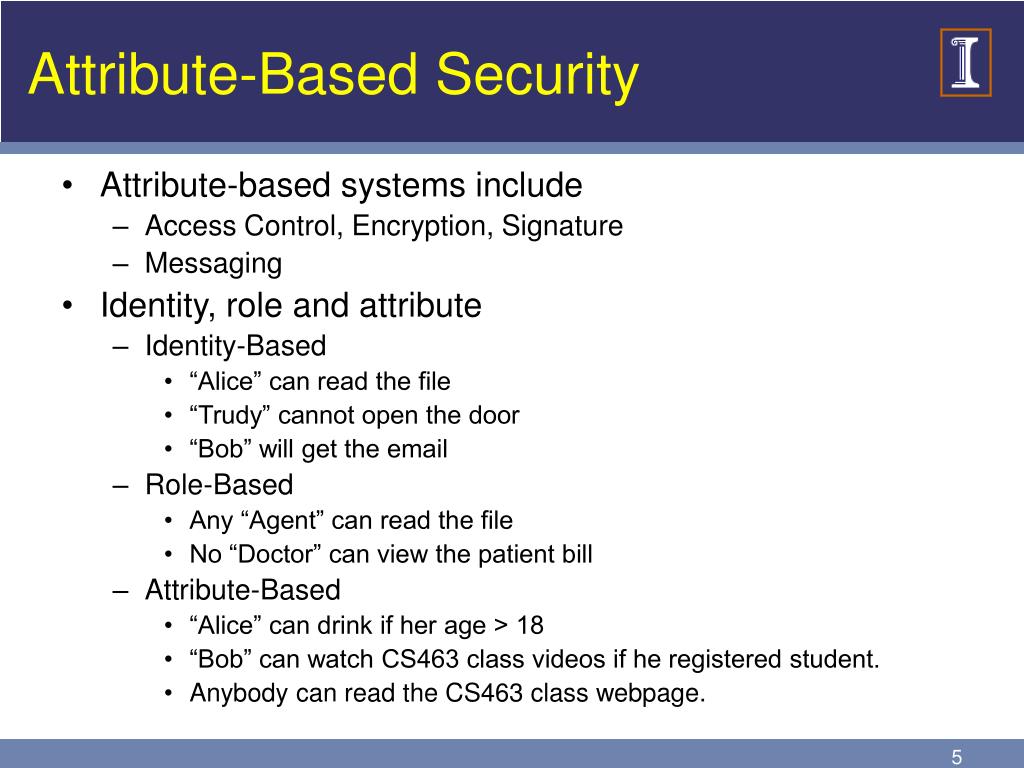
Attribute Based Messaging And Security Illinois Computer Security In this work we provide an alternative method of authentication in which the solicitors, instead of revealing their identity, only need to prove possession of certain attributes, dynamically defined by the group, to become a member. Attribute based encryption incorporates access control policies and attributes with encryption and decryption functions and a one to many authorization scheme that requires fewer keys than public key encryption.
Ppt 463 0 2 Attribute Based Security And Messaging Powerpoint Attribute based messaging (abm) enables messages to be addressed using attributes of recipients rather than an explicit list of recipients. such messaging offers benefits of efficiency, exclusiveness, and intensionality, but faces challenges in access control and confidentiality. Attribute based messaging (abm) enables messages to be addressed using attributes of recipients rather than an explicit list of recipients. such messaging offers benefits of efficiency,. Gain insights from nitin aggarwal, an associate partner with infosys consulting, on how enterprises could implement new ways of managing security in an enterprise, specifically around attribute based access controls (abac) to streamline compliance. Abstract internet of things (iot) networks has been widely deployed as the distributed computing and communication component in the smart city. the security problems in the distributed iot assisted computing architecture are still noteworthy and has not been solved satisfactorily.
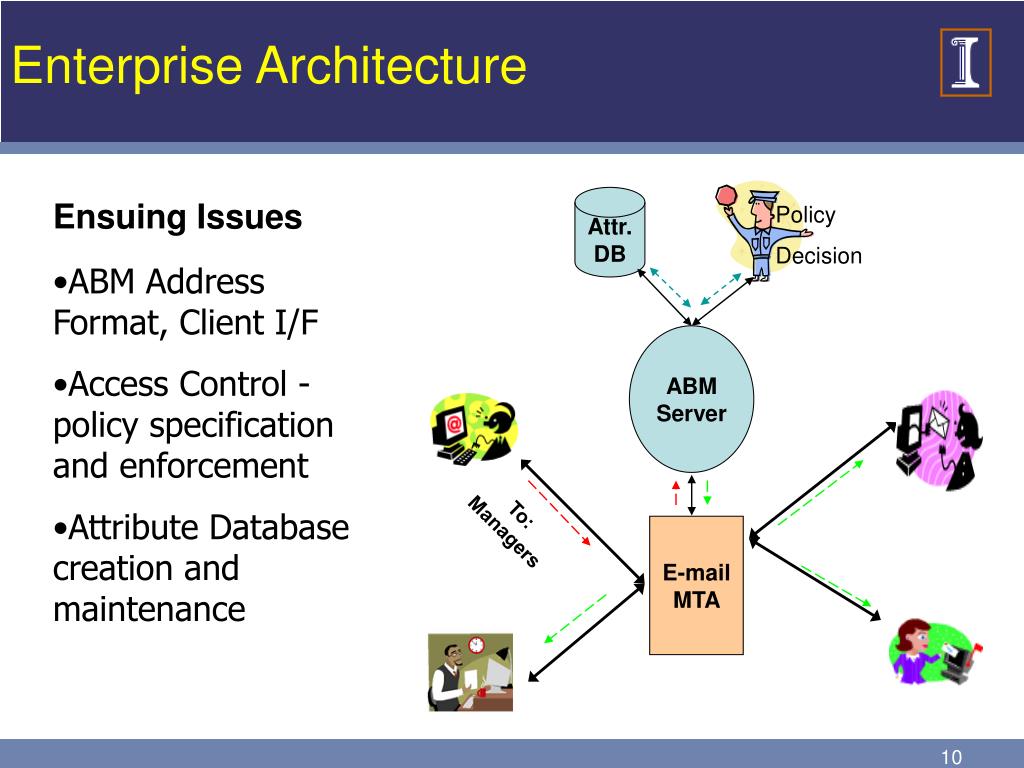
Ppt 463 0 2 Attribute Based Security And Messaging Powerpoint Gain insights from nitin aggarwal, an associate partner with infosys consulting, on how enterprises could implement new ways of managing security in an enterprise, specifically around attribute based access controls (abac) to streamline compliance. Abstract internet of things (iot) networks has been widely deployed as the distributed computing and communication component in the smart city. the security problems in the distributed iot assisted computing architecture are still noteworthy and has not been solved satisfactorily. Attribute based systems use attributes of principals and resources as they may exist, for instance, in an enterprise database, as a foundation for security and messaging operations. Messaging (email) based on attributes collected from an enterprise database is feasible and deployable for mid size enterprises. access control and confidentiality are manageable using attribute based security mechanisms. improved abe schemes with better revocation properties are needed. To address the issue of user privacy leakage, this study presents a novel privacy preserving access control algorithm, termed attribute trust based security (atst), which is designed to protect sensitive information. Messaging systems operating within the public cloud are gaining popularity. to protect message confidentiality from the public cloud including the public messaging servers, we propose to encrypt messages in messaging systems using attribute based encryption (abe).
Ppt 463 0 2 Attribute Based Security And Messaging Powerpoint Attribute based systems use attributes of principals and resources as they may exist, for instance, in an enterprise database, as a foundation for security and messaging operations. Messaging (email) based on attributes collected from an enterprise database is feasible and deployable for mid size enterprises. access control and confidentiality are manageable using attribute based security mechanisms. improved abe schemes with better revocation properties are needed. To address the issue of user privacy leakage, this study presents a novel privacy preserving access control algorithm, termed attribute trust based security (atst), which is designed to protect sensitive information. Messaging systems operating within the public cloud are gaining popularity. to protect message confidentiality from the public cloud including the public messaging servers, we propose to encrypt messages in messaging systems using attribute based encryption (abe).
Comments are closed.