Attribute Based Access Control Abac Enterprise Ready Implementation

Abac Attribute Based Access Control Pdf Mobile App Systems Learn everything you need to know about attribute based access control (abac) and develop an enterprise application to show the practical implementation of abac using permify and go. Attribute based access control (abac) redefines access management by using attributes tied to users, resources, and contexts to govern permissions dynamically. this article explores abac's role in enhancing security and flexibility within modern it infrastructures.
Fine Grained Attribute Based Access Control Aserto Our patented dynamic authorization technology and industry leading attribute based policy platform helps enterprises identify and pro tect sensitive data, monitor and control access to the data, and prevent regulatory violations – whether in the cloud or on premises. Learn how attribute based access control (abac) works with detailed policy examples for enterprise sso, ciam, and zero trust security architectures. Learn best practices for implementing abac (attribute based access control) in application authorization, including real world use cases and code examples. Implement attribute based access control for ai assistants and agents with clear steps, pdp peps, policies, rbac migration, and audit ready kpis.
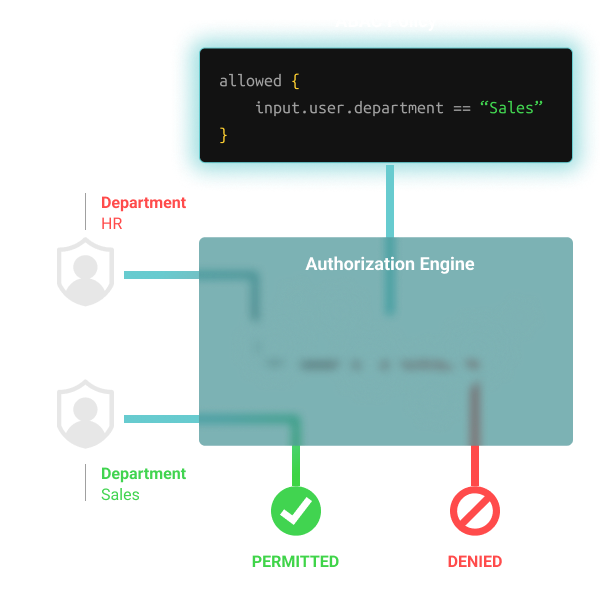
Implementing Attribute Based Access Control Abac Using Tags Learn best practices for implementing abac (attribute based access control) in application authorization, including real world use cases and code examples. Implement attribute based access control for ai assistants and agents with clear steps, pdp peps, policies, rbac migration, and audit ready kpis. Over the past decade, vendors have begun implementing attribute based access control (abac) like features in their security management and network operating system products, without general agreement as to what constitutes an appropriate set of abac features. Learn what attribute based access control (abac) is, how it works, and why it is essential for modern data security. Implementation of abac was announced as a priority objective for implementation by the us federal government, and the national institute of standards and technology (nist) issued a set of standard guidelines that define how to implement abac in an enterprise environment. In this piece, you will learn the process of implementing abac using open policy agent (opa) and understand how it all fits in when building fine grained permissions.

Attribute Based Access Control Abac 33 Download Scientific Diagram Over the past decade, vendors have begun implementing attribute based access control (abac) like features in their security management and network operating system products, without general agreement as to what constitutes an appropriate set of abac features. Learn what attribute based access control (abac) is, how it works, and why it is essential for modern data security. Implementation of abac was announced as a priority objective for implementation by the us federal government, and the national institute of standards and technology (nist) issued a set of standard guidelines that define how to implement abac in an enterprise environment. In this piece, you will learn the process of implementing abac using open policy agent (opa) and understand how it all fits in when building fine grained permissions.
Comments are closed.