Attackers Can Bypass Windows Security Using New Dll Hijacking
Hackers Find A Way Around Built In Windows Protections Fox News Dll hijacking happens when a windows app loads the wrong dll, often from a user writable folder, letting attackers run code inside a trusted process. this guide explains the main variations (search order, sideloading, phantom dll), plus detection and prevention checklists. Dll hijacking is a vulnerability where attackers replace a legitimate dynamic link library (dll) with a malicious one. this allows them to execute harmful code with the same privileges as the application, leading to risks like data theft, malware infection and full system compromise.

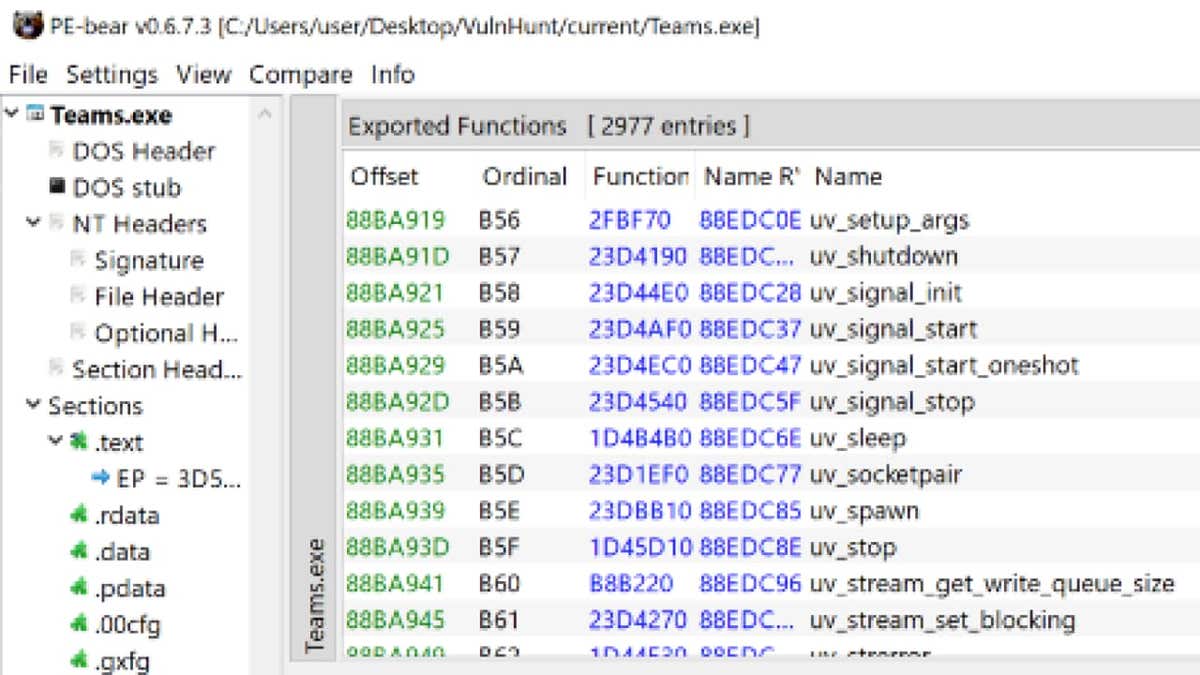
What Is Dll Hijacking And How To Prevent It Indusface Blog However, a new dll hijacking method has been discovered to be used by the threat actors, which uses the trusted winsxs folder and exploits it by the use of the traditional dll search order hijacking technique. this new method has been compatible with both windows 10 and 11. Recently, the cybersecurity researchers at a multi layered incident response company, security joes, discovered a new dll hijacking technique that enables threat actors to bypass windows. Security researchers have detailed a new variant of a dynamic link library (dll) search order hijacking technique that could be used by threat actors to bypass security mechanisms and achieve execution of malicious code on systems running microsoft windows 10 and windows 11. However, a new dll hijacking method has been discovered to be used by the threat actors, which uses the trusted winsxs folder and exploits it by the use of the traditional dll search order hijacking technique. this new method has been compatible with both windows 10 and 11.
What Is Dll Hijacking And How To Prevent It Indusface Blog Security researchers have detailed a new variant of a dynamic link library (dll) search order hijacking technique that could be used by threat actors to bypass security mechanisms and achieve execution of malicious code on systems running microsoft windows 10 and windows 11. However, a new dll hijacking method has been discovered to be used by the threat actors, which uses the trusted winsxs folder and exploits it by the use of the traditional dll search order hijacking technique. this new method has been compatible with both windows 10 and 11. Dll hijacking occurs when an attacker replacing or injecting a malicious dll file into the execution process of an application. windows applications frequently look for dlls in defined locations (for example, in the application directory, system folders). Uncover the latest threat to windows security with our exploration of a novel dll hijacking technique. learn how attackers can bypass defenses, executing stealthy and undetected breaches. Security researchers at securityjoes have published a paper detailing a new mechanism that allows threat actors to bypass windows 10 & windows 11 security controls by leveraging dlls commonly found in the trusted winsxs folder. Dll hijacking involves manipulating a trusted application into loading a malicious dll. this term encompasses several tactics like dll spoofing, injection, and side loading. it's mainly utilized for code execution, achieving persistence, and, less commonly, privilege escalation.
Comments are closed.