Attack Surface Management Definition Importance And Implementation
What Is Attack Surface Management Definition By Threatdotmedia Attack surface management is an important practice many businesses should employ to secure their machines and systems. to defeat them, you must think like them, so attack surface management does exactly this. Attack surface management is the broader, ongoing process that includes monitoring, but also involves identifying assets, assessing risk, prioritizing threats, and reducing exposure over time.
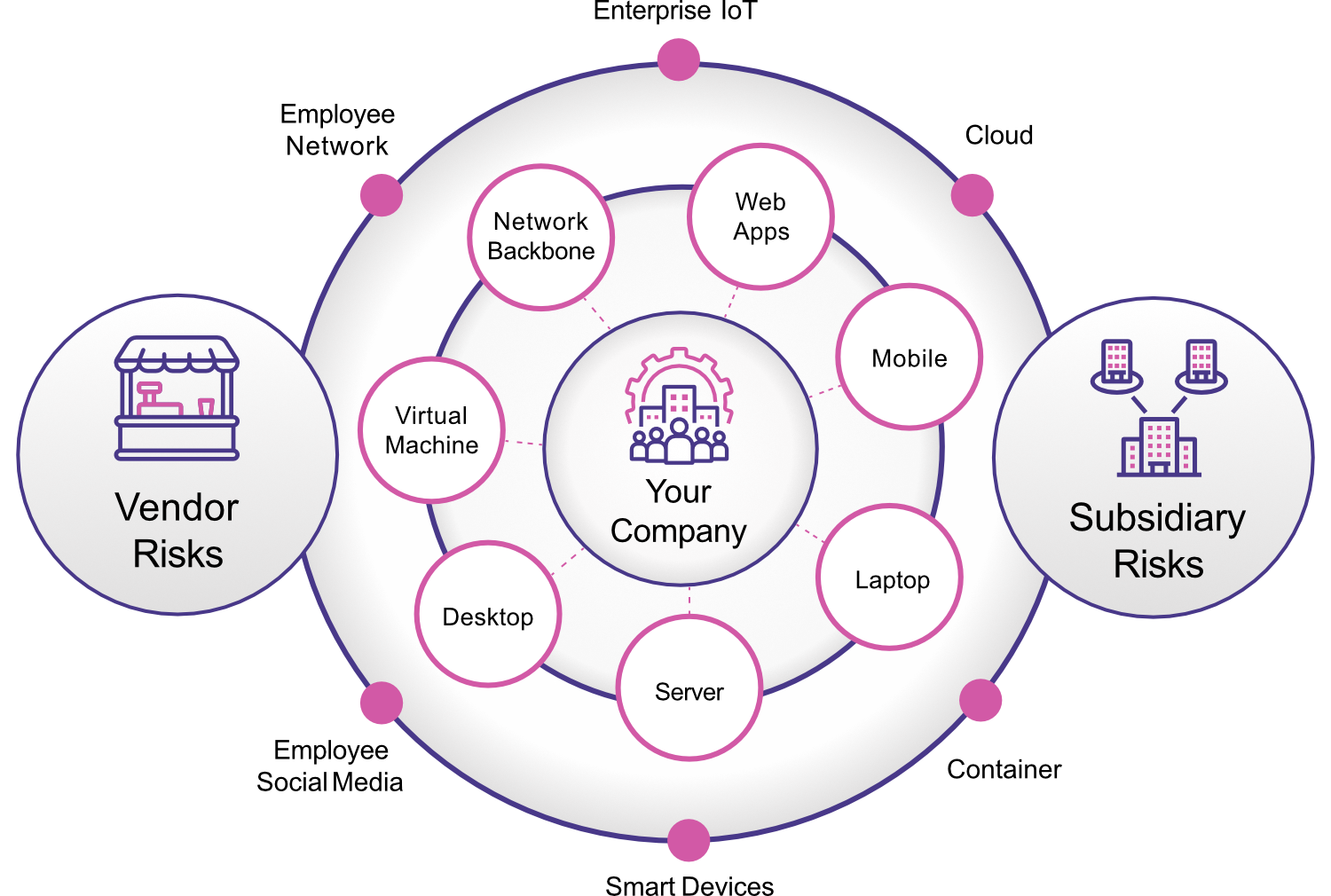
Attack Surface Management Complete Visibility Threat Protection This article will discuss how asm is critical to identifying and diminishing cyber attacks, with an emphasis on being as comprehensive as possible when discussing major components of asm, the importance of asm in proactive risk management, and best practices for deploying asm solutions. Learn how attack surface management (asm) identifies, analyzes, and reduces vulnerabilities across digital assets, enhancing security and risk mitigation. Attack surface management is an important practice many businesses should employ to secure their machines and systems. to defeat them, you must think like them, so attack surface management does exactly this. Attack surface management is essential to reducing risk across hybrid environments. attack surface management helps organizations find, catalog, prioritize, and monitor all potential entry points (attack vectors) across cloud, on premises, and saas environments.

Understanding The Importance Of Attack Surface Management Attack surface management is an important practice many businesses should employ to secure their machines and systems. to defeat them, you must think like them, so attack surface management does exactly this. Attack surface management is essential to reducing risk across hybrid environments. attack surface management helps organizations find, catalog, prioritize, and monitor all potential entry points (attack vectors) across cloud, on premises, and saas environments. Attack surface management is the continuous discovery, monitoring, evaluation, prioritization and remediation of attack vectors within an organization's it infrastructure. What is attack surface management? attack surface management (asm) is the continuous discovery, analysis, prioritization, remediation and monitoring of the cybersecurity vulnerabilities and potential attack vectors that make up an organization’s attack surface. Attack surface management (asm) calls on enterprises to continuously scan and identify possible exposures, recommend remediation steps and monitor an organization's it environment for emerging threats. Learn what attack surface management (asm) is, how it works, and why it’s vital for cybersecurity. discover types, examples, and tools to reduce digital risk.
Attack Surface Management The Importance Cynergy App Attack surface management is the continuous discovery, monitoring, evaluation, prioritization and remediation of attack vectors within an organization's it infrastructure. What is attack surface management? attack surface management (asm) is the continuous discovery, analysis, prioritization, remediation and monitoring of the cybersecurity vulnerabilities and potential attack vectors that make up an organization’s attack surface. Attack surface management (asm) calls on enterprises to continuously scan and identify possible exposures, recommend remediation steps and monitor an organization's it environment for emerging threats. Learn what attack surface management (asm) is, how it works, and why it’s vital for cybersecurity. discover types, examples, and tools to reduce digital risk.

Attack Surface Management Powerpoint And Google Slides Template Ppt Attack surface management (asm) calls on enterprises to continuously scan and identify possible exposures, recommend remediation steps and monitor an organization's it environment for emerging threats. Learn what attack surface management (asm) is, how it works, and why it’s vital for cybersecurity. discover types, examples, and tools to reduce digital risk.
Comments are closed.