Attack Path Analysis Explained Benefits Examples And Steps
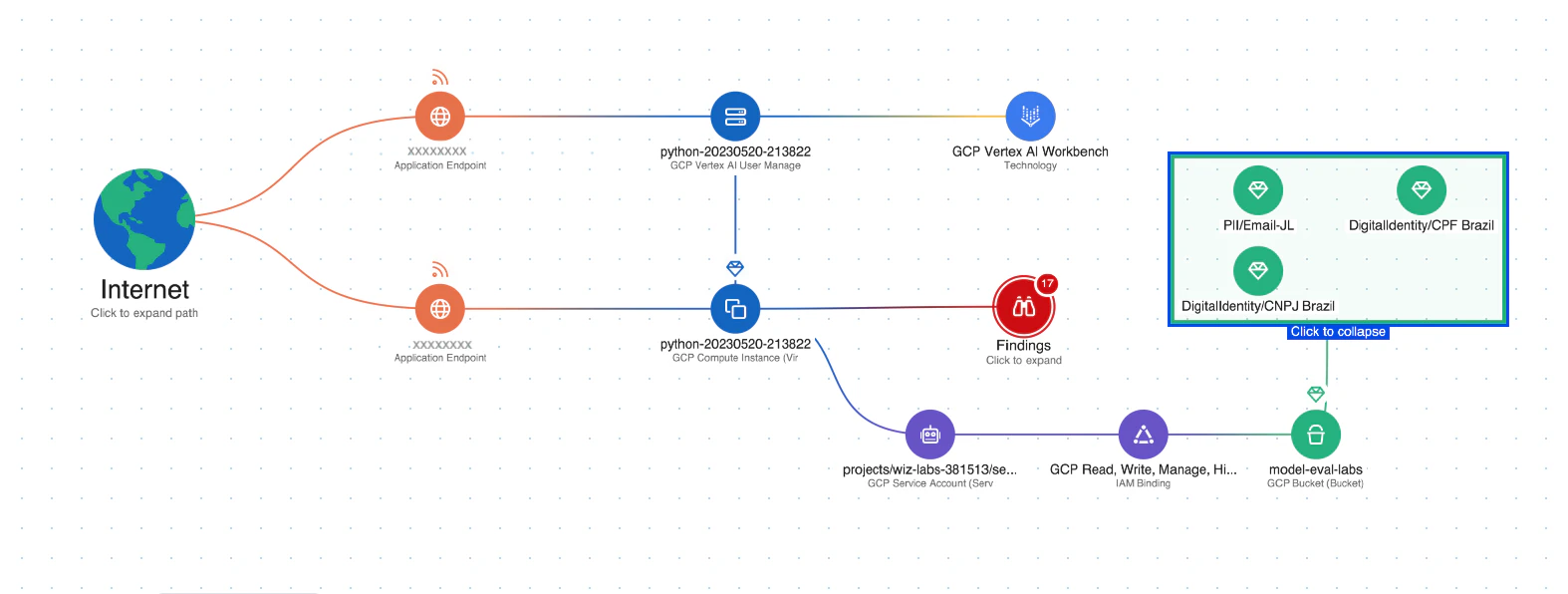
What Is Attack Path Analysis Wiz Attack path analysis (apa) is the process of identifying, mapping and analyzing potential attack routes within an it environment. it helps security professionals anticipate how adversaries could move across systems, highlighting weaknesses before they can be exploited. Learn what attack path analysis is, how it works, its benefits, challenges, best practices, and real world examples to enhance security.
Attack Path Analysis Reviews In 2025 This example illustrates how attack path analysis, powered by picus apv, enables security teams to map, prioritize, and proactively mitigate the critical steps adversaries take to escalate privileges and compromise high value assets like domain admins. Attack path analysis transforms reactive security into proactive defense by revealing how individual vulnerabilities combine to create serious threats. rather than managing thousands of isolated security findings, teams can focus on the combinations that actually matter. This guide cuts through the complexity to provide a straightforward, actionable approach to attack path mapping. you'll learn a systematic process for identifying the routes attackers might take to reach your most valuable assets—all explained in clear, practical terms that you can immediately apply to your environment. Attack path analysis (apa) helps you think like an attacker to stay ahead of threat actors and their constantly evolving tactics, techniques and procedures (ttps). with apa, you can visualize cyber threats to better understand how an attacker could move through your network.
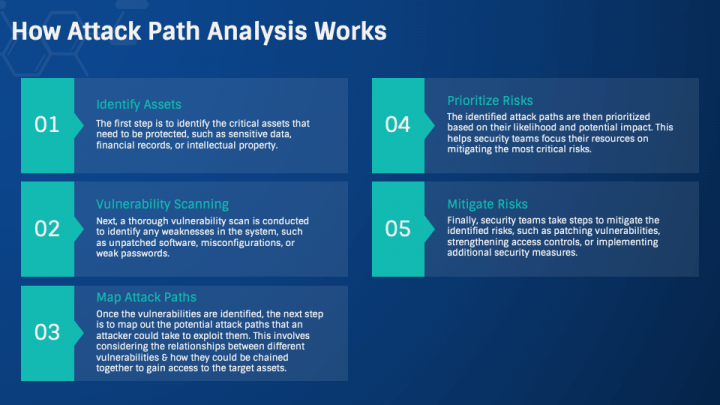
Attack Path Analysis Powerpoint And Google Slides Template Ppt Slides This guide cuts through the complexity to provide a straightforward, actionable approach to attack path mapping. you'll learn a systematic process for identifying the routes attackers might take to reach your most valuable assets—all explained in clear, practical terms that you can immediately apply to your environment. Attack path analysis (apa) helps you think like an attacker to stay ahead of threat actors and their constantly evolving tactics, techniques and procedures (ttps). with apa, you can visualize cyber threats to better understand how an attacker could move through your network. By shifting focus from individual flaws to the full structure of reachability, attack path analysis gives defenders a more accurate view of risk. in the next sections, we will explore why this matters in real breaches, how graph based models make it possible, and how to begin applying it in practice. Attack path mapping and analysis is the practice of identifying how a real attacker could move through your environment to reach high value assets, and prioritizing which paths matter most. By taking these practical steps, organizations can start mapping attack paths effectively. this proactive method boosts security and helps create a culture where everyone is aware of and ready for possible threats. This guide explains what attack paths are, how they work, why traditional vulnerability scanning misses them, and how modern penetration testing identifies and documents these multi step exploitation scenarios.
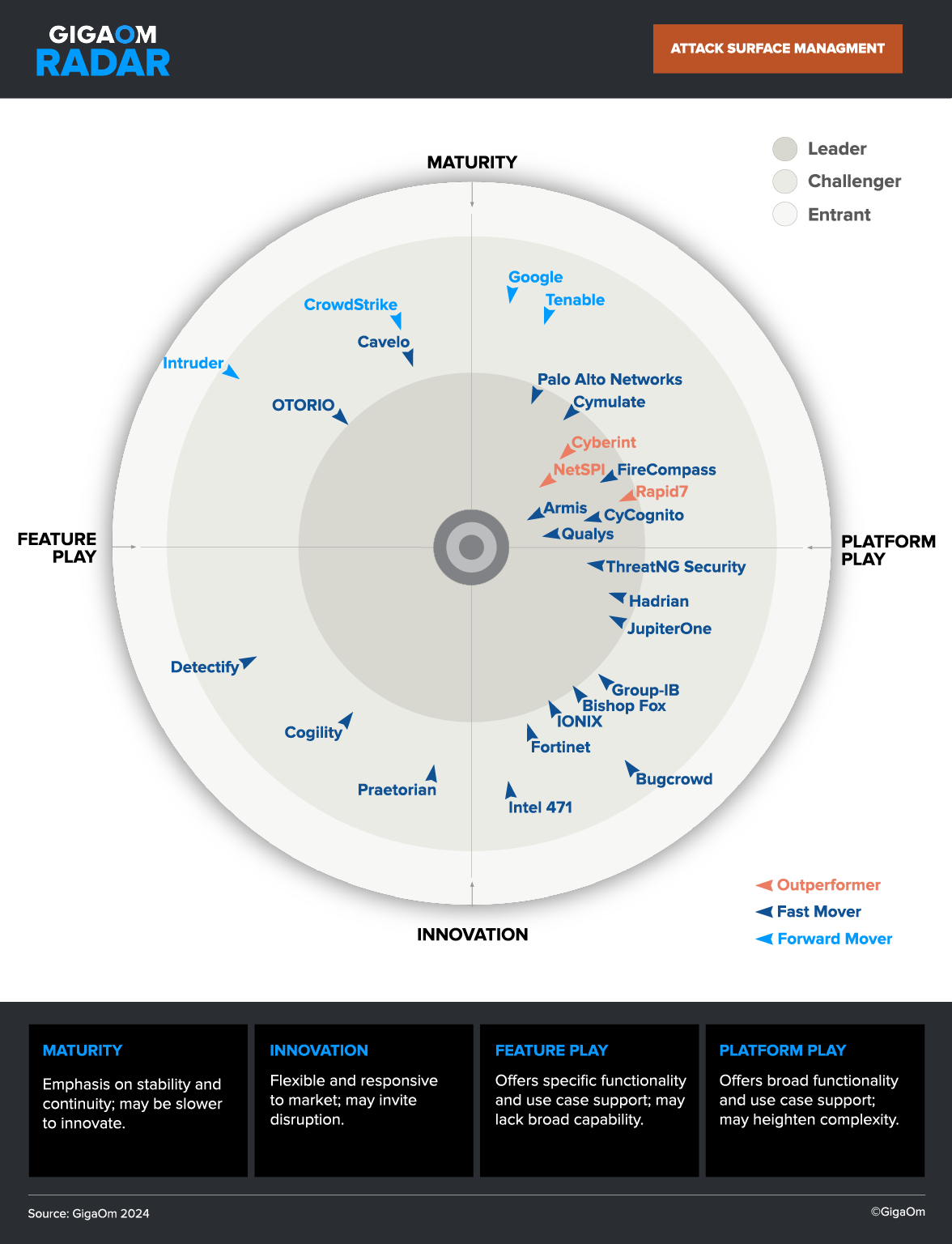
Attack Path Analysis How It Works Use Cases Best Practices Cycognito By shifting focus from individual flaws to the full structure of reachability, attack path analysis gives defenders a more accurate view of risk. in the next sections, we will explore why this matters in real breaches, how graph based models make it possible, and how to begin applying it in practice. Attack path mapping and analysis is the practice of identifying how a real attacker could move through your environment to reach high value assets, and prioritizing which paths matter most. By taking these practical steps, organizations can start mapping attack paths effectively. this proactive method boosts security and helps create a culture where everyone is aware of and ready for possible threats. This guide explains what attack paths are, how they work, why traditional vulnerability scanning misses them, and how modern penetration testing identifies and documents these multi step exploitation scenarios.
Attack Path Analysis How It Works Use Cases Best Practices Cycognito By taking these practical steps, organizations can start mapping attack paths effectively. this proactive method boosts security and helps create a culture where everyone is aware of and ready for possible threats. This guide explains what attack paths are, how they work, why traditional vulnerability scanning misses them, and how modern penetration testing identifies and documents these multi step exploitation scenarios.
Comments are closed.