Attack Attribution Targeted Or Random Attack

Attack Attribution Targeted Or Random Attack These technologies uncover subtle patterns and connections that human analysts might miss, learning from historical attack data to anticipate future attack vectors and attribute them with greater accuracy. One crucial aspect of attribution is discerning whether an attack was specifically targeted or part of a larger campaign aiming to compromise multiple organizations.
Github Opoyraz Whodunit Cyber Attack Attribution A Study To Develop We define cyber attribution as allocating a cyber attack to a specific attacker or group of attackers in a first step and unveiling the attacker’s real world identity in a second step. Let us now introduce the attacker dataset for attack attribution and investigation. unlike existing datasets, attacker offers highly detailed information through a more complex annotation process, providing context beyond words or tokens regarding their respective entity types. But is it? is this a productive understanding of attribution? — this article argues that attribution is what states make of it. to show how, we introduce the q model: designed to explain, guide, and improve the making of attribution. The paper discusses the state of the art regarding attribution abilities across both types of attack, provides recommendations for improved attribution, and lays out future research.
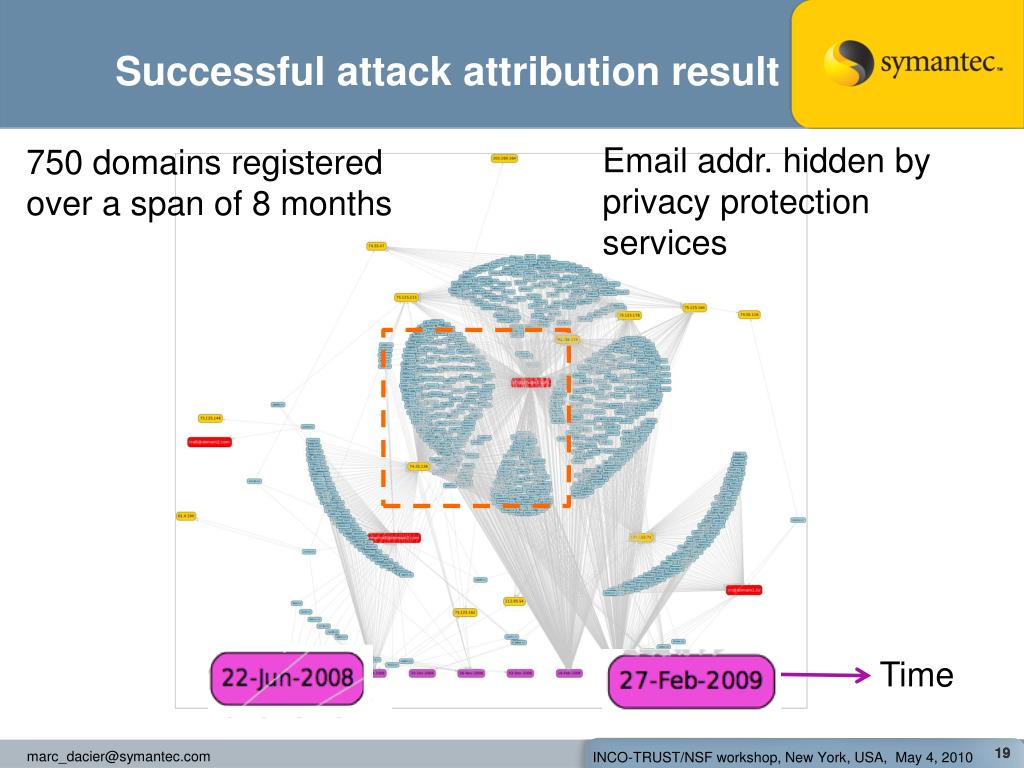
Ppt Attack Attribution Powerpoint Presentation Free Download Id But is it? is this a productive understanding of attribution? — this article argues that attribution is what states make of it. to show how, we introduce the q model: designed to explain, guide, and improve the making of attribution. The paper discusses the state of the art regarding attribution abilities across both types of attack, provides recommendations for improved attribution, and lays out future research. In this study, we address the problem of attacker attribution in complex, multi step network attack (msna) environments, aiming to identify the responsible attacker (e.g., ip address) for each sequence of security alerts, rather than merely detecting the presence or type of attack. A hacker inserted malware in axios, an open source web tool downloaded tens of millions of times weekly, in a widespread hack. Attributing a cyberattack is difficult, and of limited interest to companies that are targeted by cyberattacks. in contrast, secret services often have a compelling interest in finding out whether a state is behind the attack. [3]. Challenge: attack attribution is centralized upon detection of an attack, cooperating networks send all of their flows’ features to a central correlation node for matching.
Ppt Attack Attribution Powerpoint Presentation Free Download Id In this study, we address the problem of attacker attribution in complex, multi step network attack (msna) environments, aiming to identify the responsible attacker (e.g., ip address) for each sequence of security alerts, rather than merely detecting the presence or type of attack. A hacker inserted malware in axios, an open source web tool downloaded tens of millions of times weekly, in a widespread hack. Attributing a cyberattack is difficult, and of limited interest to companies that are targeted by cyberattacks. in contrast, secret services often have a compelling interest in finding out whether a state is behind the attack. [3]. Challenge: attack attribution is centralized upon detection of an attack, cooperating networks send all of their flows’ features to a central correlation node for matching.
Comments are closed.