Atm Hacking 2 1 Pdf Computers

Atm Hacking Latest News Photos Videos Wired 4 stages of emv transaction are being captured and released into a tunnel to speak to another atm or pos. the cash out device regurgitates the exact “send and receive” from a shimmed device to the cash out device. the shimmed device is told to hold while the tunneled transaction happens. Loading….

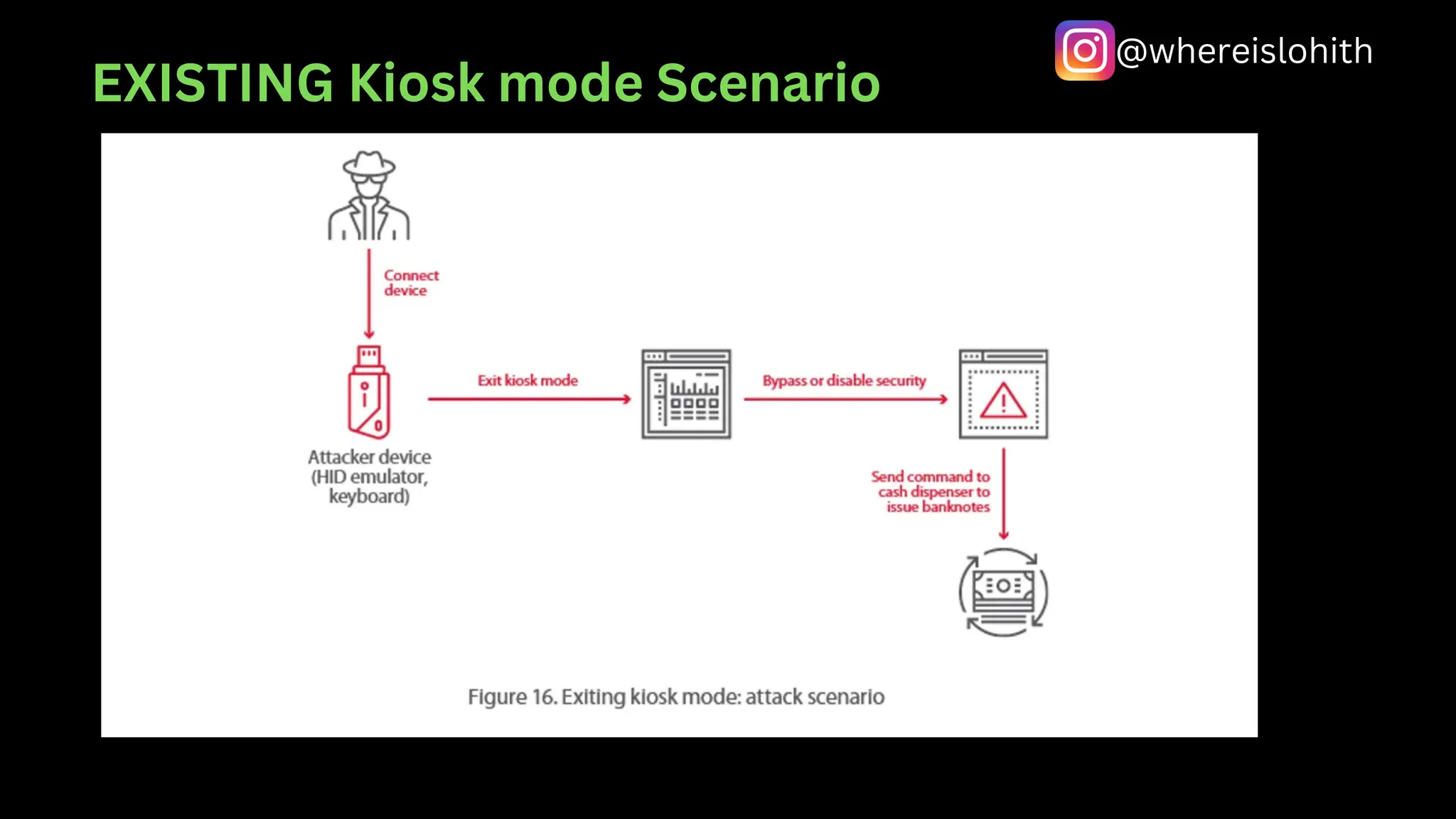
Atm Hacking 2 1 Pdf Atm hacking jackpotting is one such cyber crime where there is attack on an atm vending machine to steal away the money. it is called atm hacking as someone takes illegal control over the operation of atm and jackpotting as the atm vending machine vulnerably dispenses all the cash to the attacker. It details different types of atm hacking methods, such as skimming, jackpotting, and network attacks, noting the high level of vulnerability in many tested machines. Atm malware attacks in various parts of the world continue to make headlines and cause significant costs to the financial industry. in the bigger scale of things, their persistence demonstrates the concerns that are attached to digital atm security. Perform a penetration test of your atm applications peripherals hardware to gain a better understanding of the impact an atm security incident or breach would have on your systems – and learn if your existing security controls are working as intended.

Hacking An Atm Machine Is Something That Has Been There For A Very Long Atm malware attacks in various parts of the world continue to make headlines and cause significant costs to the financial industry. in the bigger scale of things, their persistence demonstrates the concerns that are attached to digital atm security. Perform a penetration test of your atm applications peripherals hardware to gain a better understanding of the impact an atm security incident or breach would have on your systems – and learn if your existing security controls are working as intended. In this case study we used a risk management framework to determine traditional and emerging atm crimes, and made recommendations on measures atm owners can put in place to mitigate both the. Atm hacking free download as pdf file (.pdf), text file (.txt) or read online for free. the document discusses various methods used in atm hacking, including skimming, jackpotting, blackbox attacks, and network usb based attacks. Contribute to dosx dev pdf development by creating an account on github. Oduce “next generation” secure atm systems. this presentation explains that a motivated attacker could bypass anti skimming anti shimming methods introduced to the latest generation atms, and perform emv nfc long range attacks that allow real t.

Atm Hacking 2 1 Pdf In this case study we used a risk management framework to determine traditional and emerging atm crimes, and made recommendations on measures atm owners can put in place to mitigate both the. Atm hacking free download as pdf file (.pdf), text file (.txt) or read online for free. the document discusses various methods used in atm hacking, including skimming, jackpotting, blackbox attacks, and network usb based attacks. Contribute to dosx dev pdf development by creating an account on github. Oduce “next generation” secure atm systems. this presentation explains that a motivated attacker could bypass anti skimming anti shimming methods introduced to the latest generation atms, and perform emv nfc long range attacks that allow real t.
Atm Hacking And Cyber Security Atm Security Pdf Contribute to dosx dev pdf development by creating an account on github. Oduce “next generation” secure atm systems. this presentation explains that a motivated attacker could bypass anti skimming anti shimming methods introduced to the latest generation atms, and perform emv nfc long range attacks that allow real t.
Asset Preview
Comments are closed.