Asymmetric Encryption Cryptography Tutorial 4 5
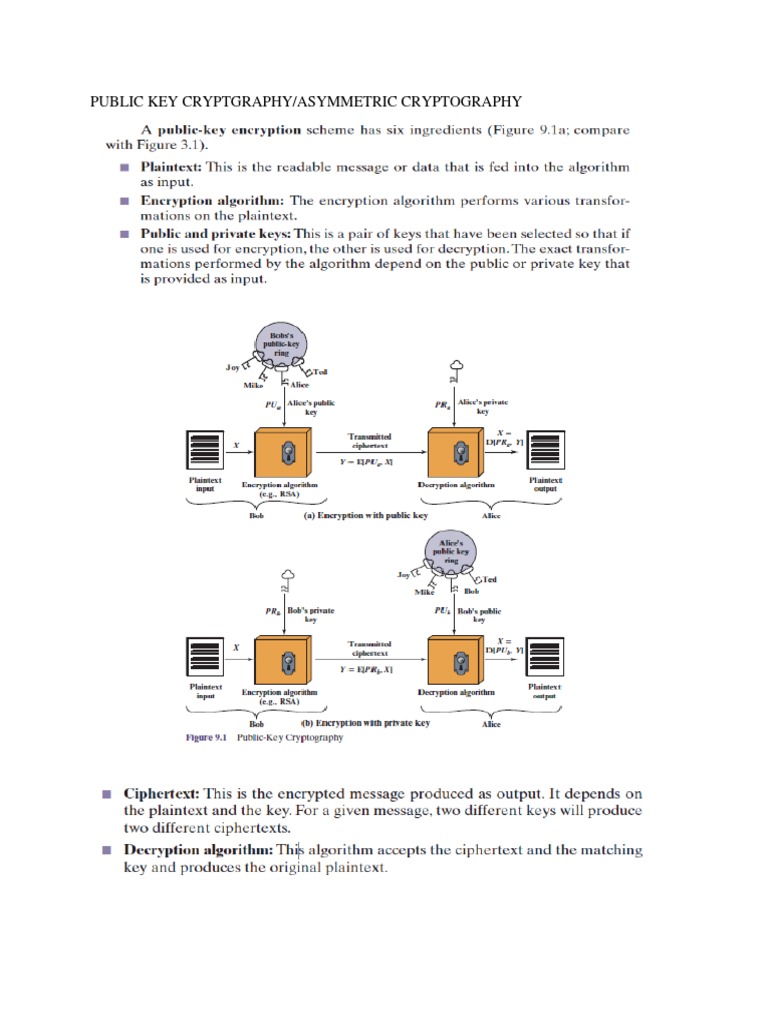
Asymmetric Cryptography Notes Pdf Pdf Public Key Cryptography In asymmetric key cryptography, there are two keys, also known as key pairs: a public key and a private key. the public key is publicly distributed. anyone can use this public key to encrypt messages, but only the recipient, who holds the corresponding private key, can decrypt those messages. Hey hackers!asymmetric encryption is the other main type of encryption. this module will be a little bit more chilled back, mainly some lecture.course home:.

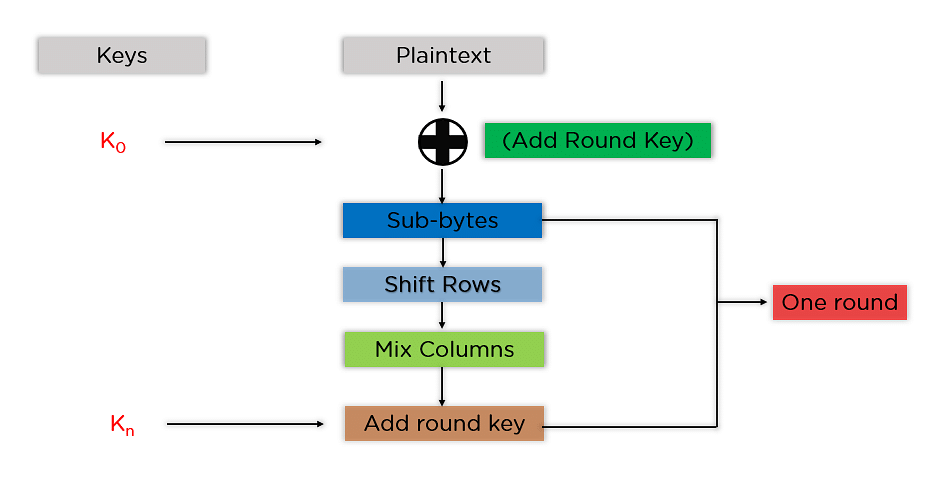
Asymmetric Encryption Pdf Public Key Cryptography Cryptography Popular public key cryptosystems (asymmetric crypto algorithms) like rsa (rivest–shamir–adleman), ecc (elliptic curve cryptography), diffie hellman, ecdh, ecdsa and eddsa, are widely used in the modern cryptography and we shall demonstrate most of them in practice with code examples. 🎯 day 5 mission summary understood the difference between symmetric and asymmetric encryption learned how hashing works and why it's one way studied common algorithms: aes, rsa, md5, sha 1, sha 256 understood the tls handshake process step by step learned how pki and certificate authorities establish trust. Asymmetric key cryptography is also called public key cryptography. it is the cryptographic algorithm which uses pairs or related keys; the keys are known as public and private keys. Discover how asymmetric encryption works, from rsa to elliptic curve cryptography (ecc). learn about key exchanges, digital signatures, and how public key cryptography secures online communications.
All You Need To Know About Asymmetric Encryption Asymmetric key cryptography is also called public key cryptography. it is the cryptographic algorithm which uses pairs or related keys; the keys are known as public and private keys. Discover how asymmetric encryption works, from rsa to elliptic curve cryptography (ecc). learn about key exchanges, digital signatures, and how public key cryptography secures online communications. Asymmetric cryptography for cissp: rsa, ecc, and pki explained with key concepts and real world uses for exam success. In this lesson we will look at asymmetric key cryptography which forms the basis of many secure network interactions today. Discover how asymmetric encryption powers modern cryptography, from digital identity to quantum threats, ensuring secure communication online. Chapter 4 of the it security document discusses asymmetric cryptography, highlighting the difference from symmetric key systems by allowing a public key to be shared while keeping a private key secure.
All You Need To Know About Asymmetric Encryption Asymmetric cryptography for cissp: rsa, ecc, and pki explained with key concepts and real world uses for exam success. In this lesson we will look at asymmetric key cryptography which forms the basis of many secure network interactions today. Discover how asymmetric encryption powers modern cryptography, from digital identity to quantum threats, ensuring secure communication online. Chapter 4 of the it security document discusses asymmetric cryptography, highlighting the difference from symmetric key systems by allowing a public key to be shared while keeping a private key secure.
All You Need To Know About Asymmetric Encryption Discover how asymmetric encryption powers modern cryptography, from digital identity to quantum threats, ensuring secure communication online. Chapter 4 of the it security document discusses asymmetric cryptography, highlighting the difference from symmetric key systems by allowing a public key to be shared while keeping a private key secure.
All You Need To Know About Asymmetric Encryption
Comments are closed.