Arkana Cryptography 101 Hashing

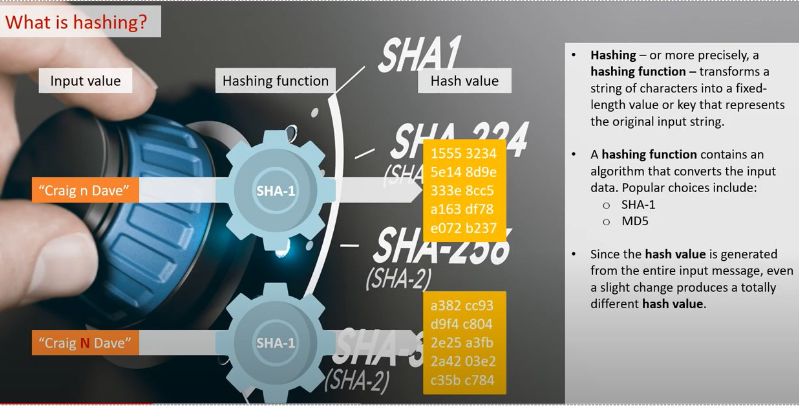
Free Video Advanced Cryptography Hashing Lecture 3 From Bill Hashing functions are an essential cryptographic primitive. join me in a deep dive into what they are, and what they are used for!. Plaintext data before encryption or hashing, often text but not always as it could be a photograph or other file instead. encoding this is not a form of encryption, just a form of data representation like base64 or hexadecimal. immediately reversible. hash a hash is the output of a hash function. hashing can also be used as a verb, "to hash", meaning to produce the hash value of some.

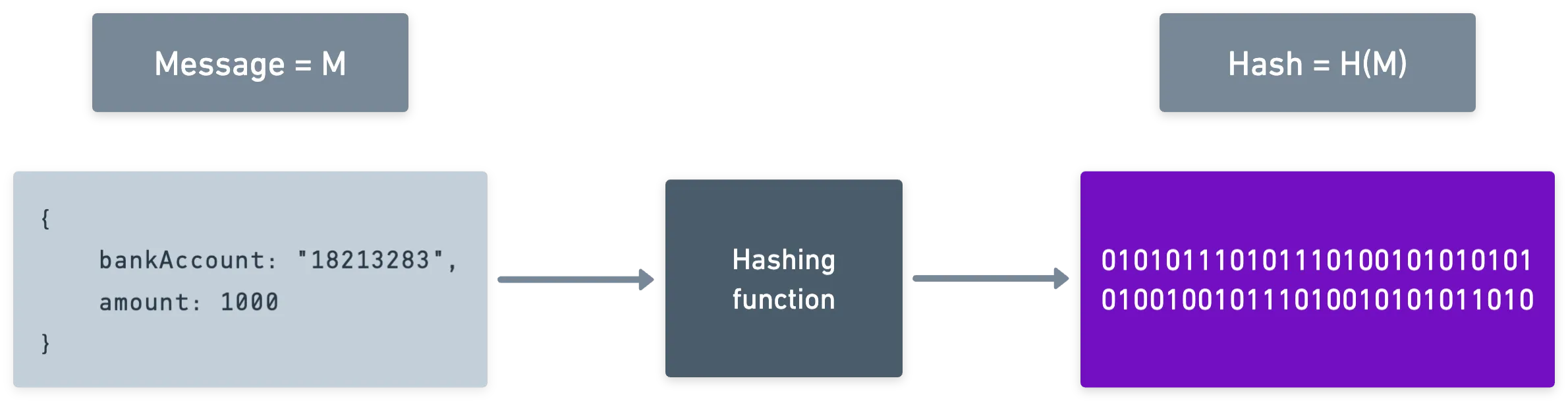
Free Video Cryptography Lab Introduction To Hashing Techniques From Now that we have a basic idea of what a hash function is in cryptography, let's break down the internal mechanics. the first act of the hashing algorithm is to divide the large input data into blocks of equal size. further, the algorithm applies the hashing process to the data blocks one by one. Hash functions play a fundamental role in cryptography they are used in a variety of cryptographic primitives and protocols. they are very difficult to design because of stringent security and performance requirements. Hash functions (hashing algorithms) used in computer cryptography are known as " cryptographic hash functions ". examples of such functions are sha 256 and sha3 256, which transform arbitrary input to 256 bit output. With this intuition in mind, let us introduce the solution to all of our problems: hash functions. at their core, hash functions are nothing more than functions that take an arbitrarily long bitstring and output a bitstring of fixed length.
Learn Cryptography In Just 3 Hrs Encryption Hashing Ssl Tls Pki Hash functions (hashing algorithms) used in computer cryptography are known as " cryptographic hash functions ". examples of such functions are sha 256 and sha3 256, which transform arbitrary input to 256 bit output. With this intuition in mind, let us introduce the solution to all of our problems: hash functions. at their core, hash functions are nothing more than functions that take an arbitrarily long bitstring and output a bitstring of fixed length. Learn what hashing in cryptography is, how it works, key algorithms like sha 256, real world uses, and best practices to keep your data secure. In practice, hash functions are used for “digesting” large data. for example, if you want to check the validity of a large file (potentially much larger than a few megabytes), you can check the hash value of that file with the expected hash. Hashing functions are an essential cryptographic primitive. join me in a deep dive into what they are, and what they are used for!. Because hashing is a one way function (i.e., it is impossible to "decrypt" a hash and obtain the original plaintext value), it is the most appropriate approach for password validation.
Encryption 101 Encryption Key Management By Monica Makau Xero Learn what hashing in cryptography is, how it works, key algorithms like sha 256, real world uses, and best practices to keep your data secure. In practice, hash functions are used for “digesting” large data. for example, if you want to check the validity of a large file (potentially much larger than a few megabytes), you can check the hash value of that file with the expected hash. Hashing functions are an essential cryptographic primitive. join me in a deep dive into what they are, and what they are used for!. Because hashing is a one way function (i.e., it is impossible to "decrypt" a hash and obtain the original plaintext value), it is the most appropriate approach for password validation.
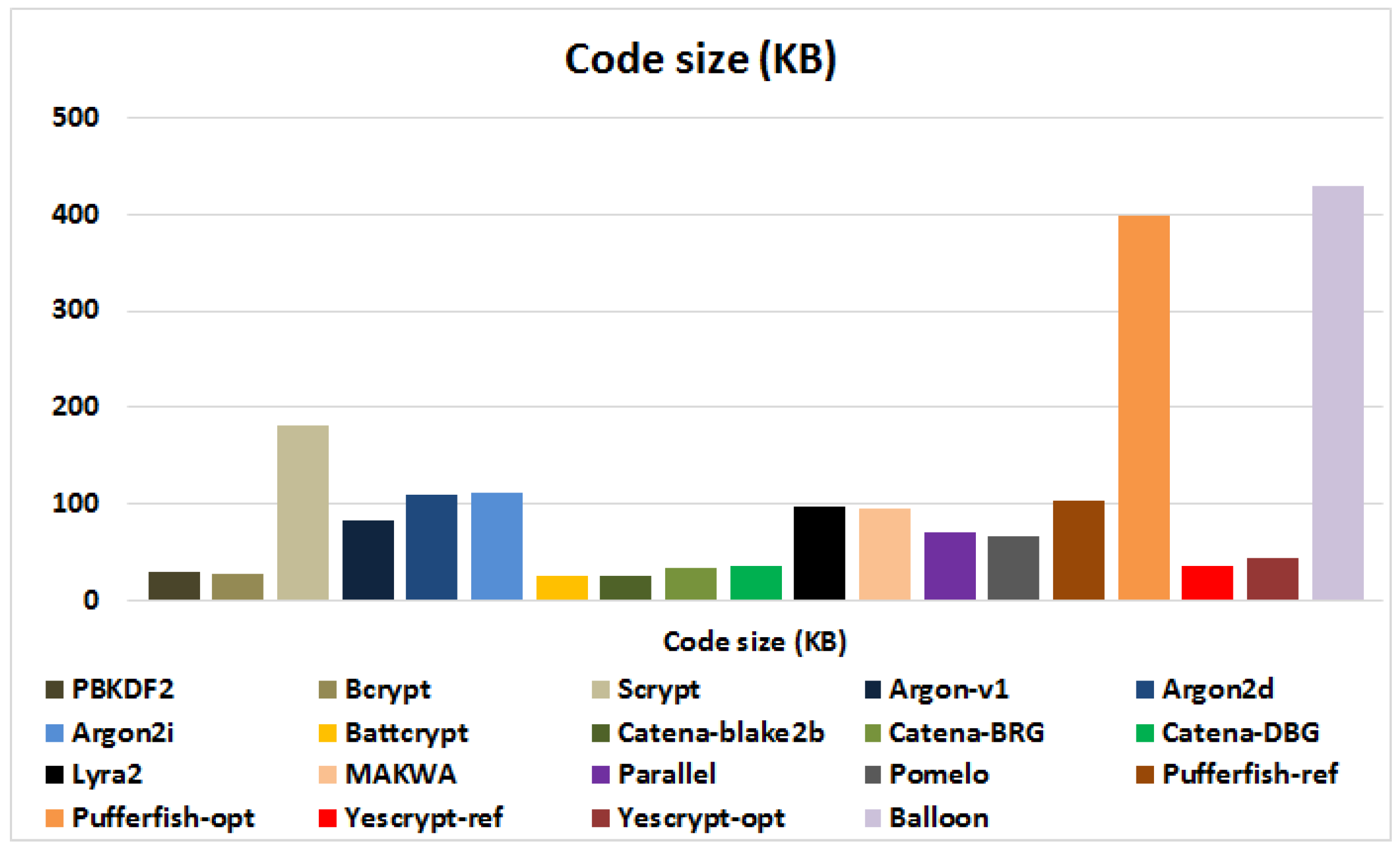
Password Hashing Status Hashing functions are an essential cryptographic primitive. join me in a deep dive into what they are, and what they are used for!. Because hashing is a one way function (i.e., it is impossible to "decrypt" a hash and obtain the original plaintext value), it is the most appropriate approach for password validation.
Arkana Cryptography 101 Hashing
Comments are closed.