Arbitrary Read And Write In Webkit Exploit

Angler Exploit Kit Generated By Admedia Gates Sans Isc This post showed how an attacker can (still) exploit the well known addrof and fakeobj primitives to gain arbitrary memory read write in webkit. for that the structureid mitigation had to be bypassed, while bypassing the gigacage was mostly optional (but fun). The webkit exploit establishes arbitrary memory read write primitives in the browser process, leaks module base addresses, and sets up return oriented programming (rop) chain execution to escalate to kernel level privileges.

Exploiting Arbitrary Read Write Linux Kernel Invictus Security This vulnerability, an out of bounds write issue, could allow attackers to execute unauthorized code on vulnerable devices. the vulnerability lies within webkit, a cross platform web browser engine used by safari and other applications across macos, ios, linux, and windows. A use after free vulnerability in apple's webkit engine affects multiple products including safari, ios, ipados, macos, watchos, tvos, and visionos versions prior to their respective 26.2 releases. processing maliciously crafted web content may lead to arbitrary code execution. By redirecting one instance's global value slot pointer to the other's, arbitrary addresses can be read and written through normal wasm global get set operations. But now it's time to put it all together and create an arbitrary memory read and write primitive. we are building here on the setup from last post. let's recap how the victim object looks like in memory. the victim object is an arraywithdoubles, so it has a butterfly that contains double elements.
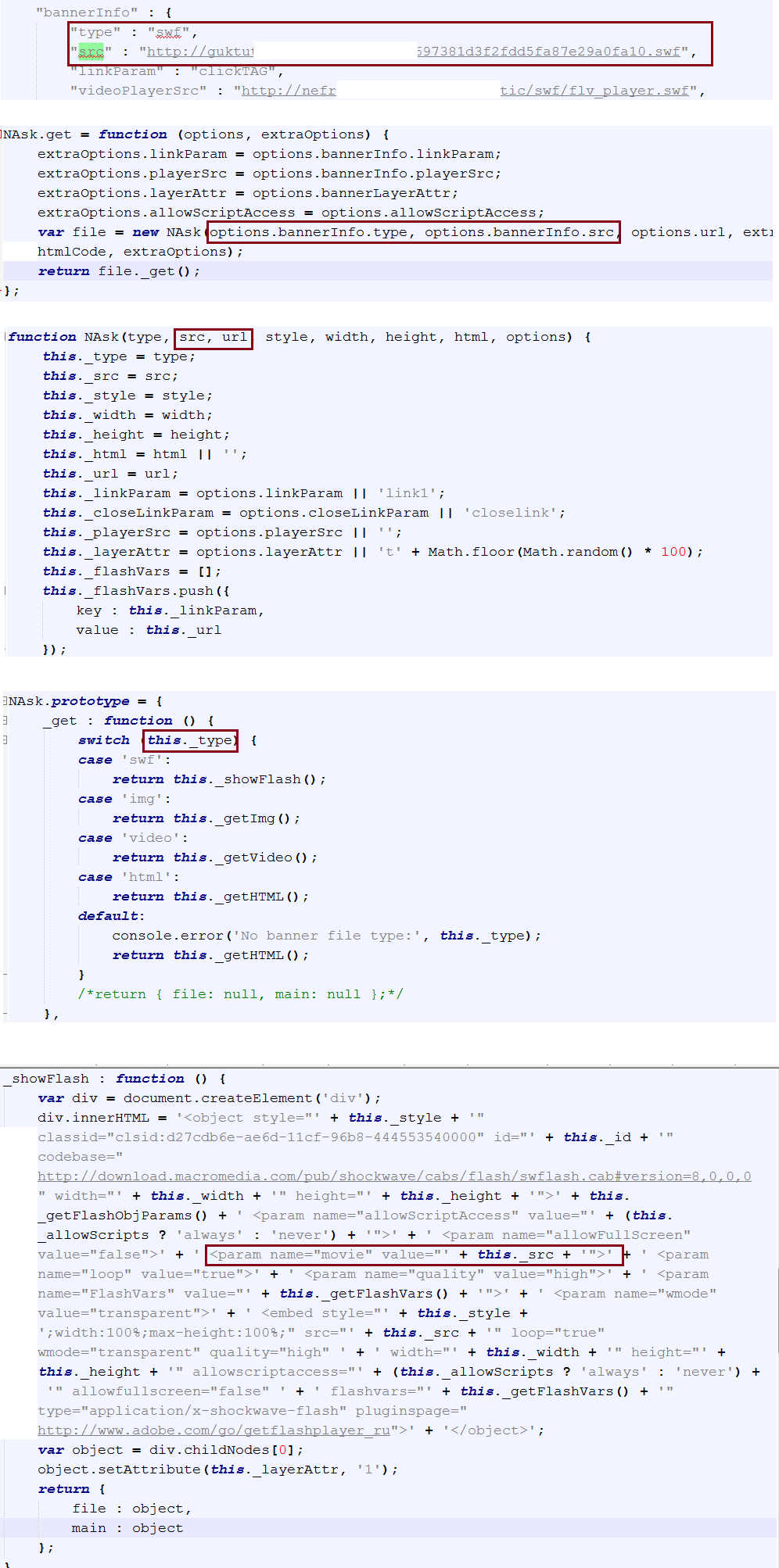
Rig Exploit Kit March 9th 2016 By redirecting one instance's global value slot pointer to the other's, arbitrary addresses can be read and written through normal wasm global get set operations. But now it's time to put it all together and create an arbitrary memory read and write primitive. we are building here on the setup from last post. let's recap how the victim object looks like in memory. the victim object is an arraywithdoubles, so it has a butterfly that contains double elements. Since it was fixed in a recent commit 9158c52, we decided to share the technical details of the vulnerability and how we successfully exploited it to gain rce in javascriptcore. starting from the commit 053d9a84, where a method, array.prototype.toreversed(), was reimplemented in webkit. We are finally achieving arbitrary read write and talk about the various possibilities we have now. blog: liveoverflow preparing fo more. 3.3 arbitrary read write engine the exploit escalates from addrof fakeobj to full arbitrary read write by constructing a fake jsobject whose inline property storage overlaps with a controlled region:. Today, we’ll break down cve 2023 32419—what it is, how attackers could exploit it, what apple did to fix it, and tips to make sure you’re protected.
Comments are closed.