Arbitrary File Write Articles
Arbitrary File Write Articles These are arbitrary file write vulnerabilities. they can become a powerful tool in the hands of an attacker, for example, when attacking a website or escalating privileges in an os. also, afw can be used in the implementation of remote code execution attacks. The praisonai templates installation feature is vulnerable to a "zip slip" arbitrary file write attack. when downloading and extracting template archives from external sources (e.g., github), the application uses python's zipfile.extractall() without verifying if the files within the archive resolve outside of the intended extraction directory.

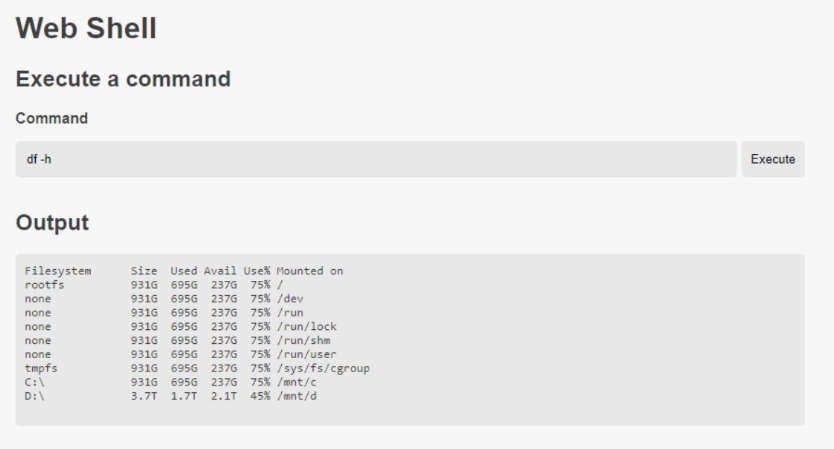
Cve 2025 48384 Git Vulnerable To Arbitrary File Write On Non Windows This oversight allows an authenticated attacker to manipulate the folder parameter to traverse directories and write files to arbitrary locations on the server, potentially leading to remote code execution. The following write up illustrates a real world chain of distinct vulnerabilities to obtain arbitrary command execution during one of our engagements, which resulted in the discovery of a new method. The vulnerability ultimately led to an arbitrary file write primitive inside the application’s private storage, caused by a path traversal issue in an exported webview activity combined with an. Cve 2025 48384 is a vulnerability that allows arbitrary file write, and ultimately code execution, on linux and macos when using git clone recursive on a weaponized repository.

Cve 2025 48384 Git Vulnerable To Arbitrary File Write On Non Windows The vulnerability ultimately led to an arbitrary file write primitive inside the application’s private storage, caused by a path traversal issue in an exported webview activity combined with an. Cve 2025 48384 is a vulnerability that allows arbitrary file write, and ultimately code execution, on linux and macos when using git clone recursive on a weaponized repository. One simple and often consistent way to execute arbitrary commands is to write your own code in a file that the server executes. this may be direct source code or other files that include code like templates which will be executed. Learn about cve 2026 39305, a critical vulnerability in praisonai that allows arbitrary file writes. update to version 4.5.113 to secure your application. A new poc exploit for cve 2026 33309 exposes langflow users to arbitrary file write and possible code execution. learn about the risks, affected versions, and mitigation steps. The gigabyte control center is vulnerable to an arbitrary file write flaw that could allow a remote, unauthenticated attacker to access files on vulnerable hosts. the hardware maker says that successful exploitation could potentially lead to code execution on the underlying system, privilege escalation, and a denial of service condition.

File 40 Pdf One simple and often consistent way to execute arbitrary commands is to write your own code in a file that the server executes. this may be direct source code or other files that include code like templates which will be executed. Learn about cve 2026 39305, a critical vulnerability in praisonai that allows arbitrary file writes. update to version 4.5.113 to secure your application. A new poc exploit for cve 2026 33309 exposes langflow users to arbitrary file write and possible code execution. learn about the risks, affected versions, and mitigation steps. The gigabyte control center is vulnerable to an arbitrary file write flaw that could allow a remote, unauthenticated attacker to access files on vulnerable hosts. the hardware maker says that successful exploitation could potentially lead to code execution on the underlying system, privilege escalation, and a denial of service condition.
Comments are closed.