Applying Firewall Rules Eukhost
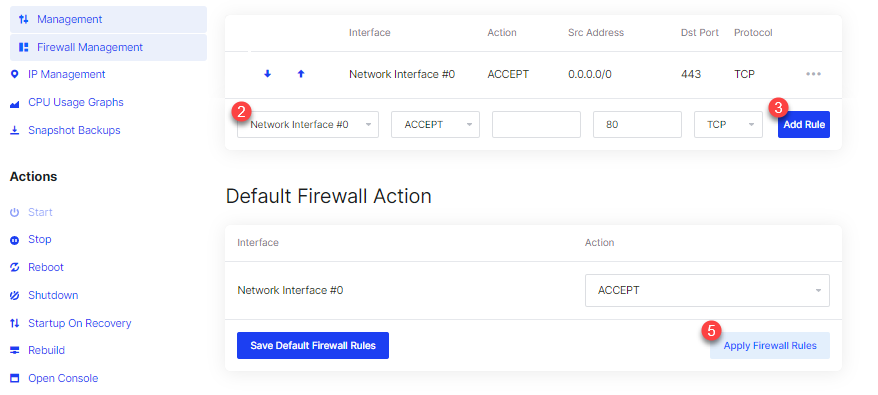
Applying Firewall Rules Eukhost Ensure robust security for your system by mastering the application of firewall rules. our guide provides step by step instructions. For example, an administrator or user may choose to add a rule to accommodate a program, open a port or protocol, or allow a predefined type of traffic. this article describes the concepts and recommendations for creating and managing firewall rules.
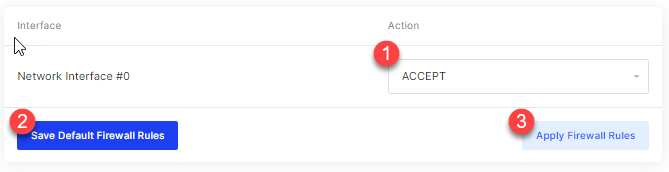
Applying Firewall Rules Eukhost Upgrading your dedicated server at the right time guarantees better performance, stronger security, and long term scalability. this guide helps you identify upgrade indicators, perform technical checks, and follow a structured… read more. Routeros documentation this webpage contains the official routeros user manual. routeros is the operating system of mikrotik devices. documentation applies for the latest stable routeros version. also, available in the documentation in pdf and html formats for offline use (updated monthly). In the gpo, you can specify whether you want to allow local administrators to create their own firewall rules on their computers, and how these rules should be merged with the rules assigned through the gpo. The new netfirewallrule cmdlet creates an inbound or outbound firewall rule and adds the rule to the target computer. some parameters are used to specify the conditions that must be matched for the rule to apply, such as the localaddress and remoteaddress parameters.
Applying Firewall Rules Eukhost In the gpo, you can specify whether you want to allow local administrators to create their own firewall rules on their computers, and how these rules should be merged with the rules assigned through the gpo. The new netfirewallrule cmdlet creates an inbound or outbound firewall rule and adds the rule to the target computer. some parameters are used to specify the conditions that must be matched for the rule to apply, such as the localaddress and remoteaddress parameters. However, sometimes legitimate applications and services might get blocked by this firewall, hindering your productivity. this scenario necessitates adding exceptions to the windows firewall settings, thus enabling specific programs to operate seamlessly while still maintaining overall security. However, defining and configuring your firewall rules correctly is very complicated. it is important that the rules are applied in the right order (“deny all traffic” needs to be the last rule applied, after the few approvals that you add for traffic you want, for instance). The firewall includes three different profiles, so you can apply different rules to private and public networks. these options are included in the windows firewall with advanced security snap in, which first appeared in windows vista. It plays a crucial role in regulating the flow of incoming and outgoing network traffic based on predetermined security rules. as a user, understanding how to set inbound and outbound rules within windows firewall can significantly enhance your network security posture.
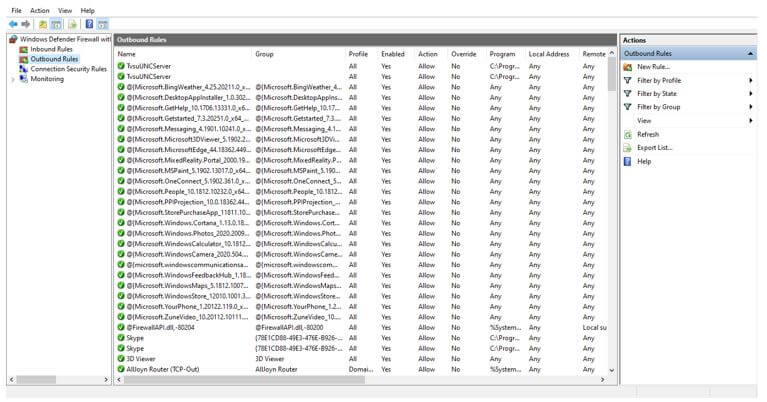
Firewall Rules How Firewall Rules Works With Examples However, sometimes legitimate applications and services might get blocked by this firewall, hindering your productivity. this scenario necessitates adding exceptions to the windows firewall settings, thus enabling specific programs to operate seamlessly while still maintaining overall security. However, defining and configuring your firewall rules correctly is very complicated. it is important that the rules are applied in the right order (“deny all traffic” needs to be the last rule applied, after the few approvals that you add for traffic you want, for instance). The firewall includes three different profiles, so you can apply different rules to private and public networks. these options are included in the windows firewall with advanced security snap in, which first appeared in windows vista. It plays a crucial role in regulating the flow of incoming and outgoing network traffic based on predetermined security rules. as a user, understanding how to set inbound and outbound rules within windows firewall can significantly enhance your network security posture.
Comments are closed.