Applied Network Forensics Chapter 04 Basic Tools Used For Analysis

Evaluating Network Forensics Applying Advanced Tools Pdf Computer Applied network forensics chapter 04 basic tools used for analysis lecture playlist: more. Their usage has been discussed. network forensic tools empower the investigator to monitor networks, gather information about the attack traffic, and assis in analyzing the network crime. a collection of network security and monitoring tools were also introduced, which are very helpful for forensics, though they were not created with evidenc.

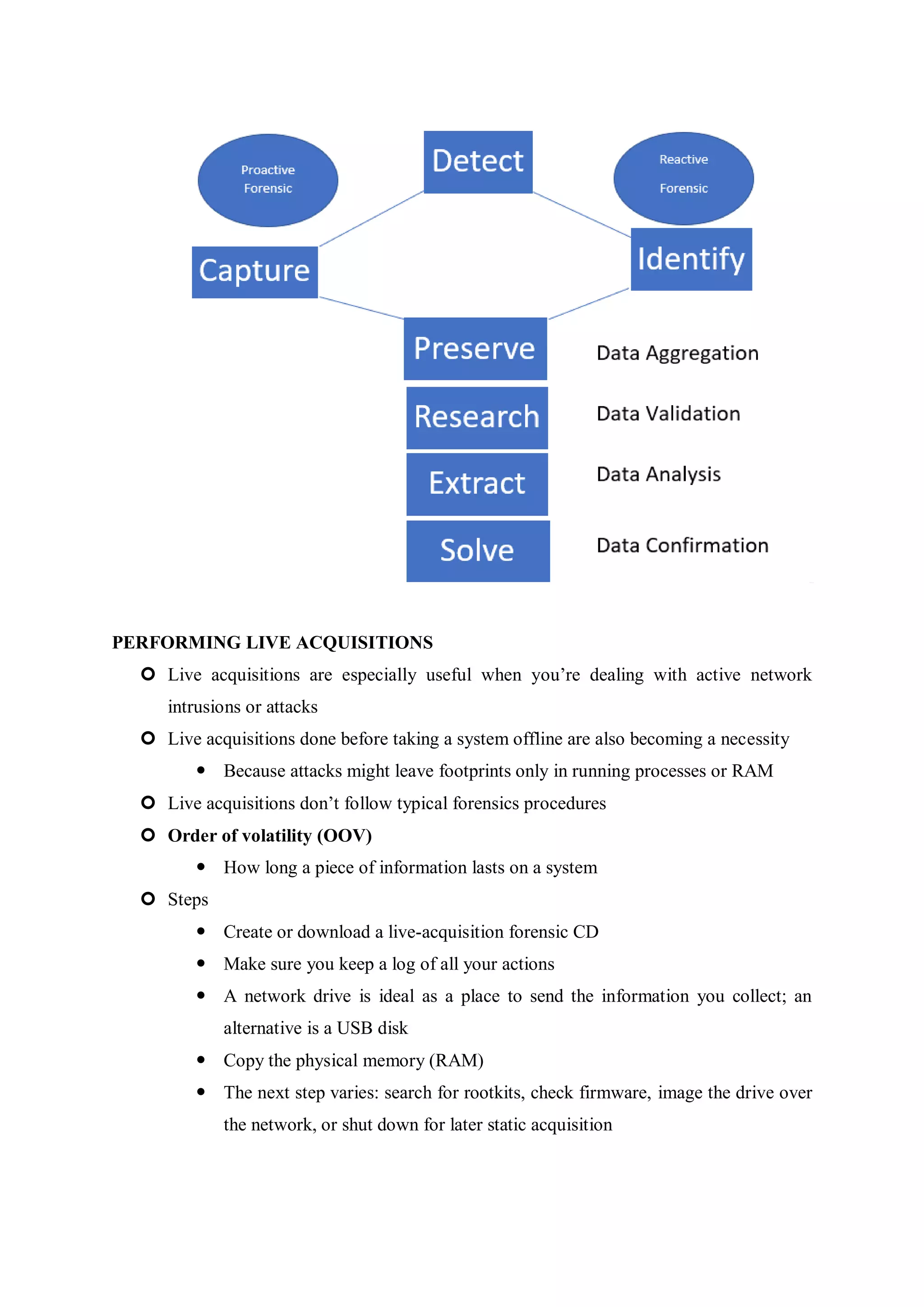
Some Commonly Used Tools For Network Forensics Investigations Source Discover the best network forensic tools for packet and log analysis in 2025. this guide covers essential software like wireshark, splunk, arkime, and zeek for investigating cyber incidents. Applied network forensics chapter 04 basic tools used for analysis arthur salmon • 623 views • 4 years ago. It outlines the steps in network forensic examination, including identification, preservation, collection, examination, analysis, presentation, and incident response, as well as methods applicable across various network protocols. This chapter explores the field of network forensics, its key principles, methodologies, and tools used to investigate and uncover cybercrimes.
The Ultimate Guide To Network Forensics Tools For 2025 It outlines the steps in network forensic examination, including identification, preservation, collection, examination, analysis, presentation, and incident response, as well as methods applicable across various network protocols. This chapter explores the field of network forensics, its key principles, methodologies, and tools used to investigate and uncover cybercrimes. Tool ecosystem and analysis workflow network forensics relies on a layered toolchain for capture, filtering, protocol dissection, and data extraction. the workflow progresses from raw packet capture to protocol specific analysis to decryption and reconstruction. Network forensics relies on specialized tools for capturing, analyzing, and investigating network data. these range from open source utilities to sophisticated commercial platforms, each with specific strengths and applications. In this blog post we explore nearly two dozen types of network forensics tools and techniques that cybersecurity professionals are using to aid in investigations. Learn how network forensic tools and network forensic analysis tools support network traffic forensics and cyber security investigations.
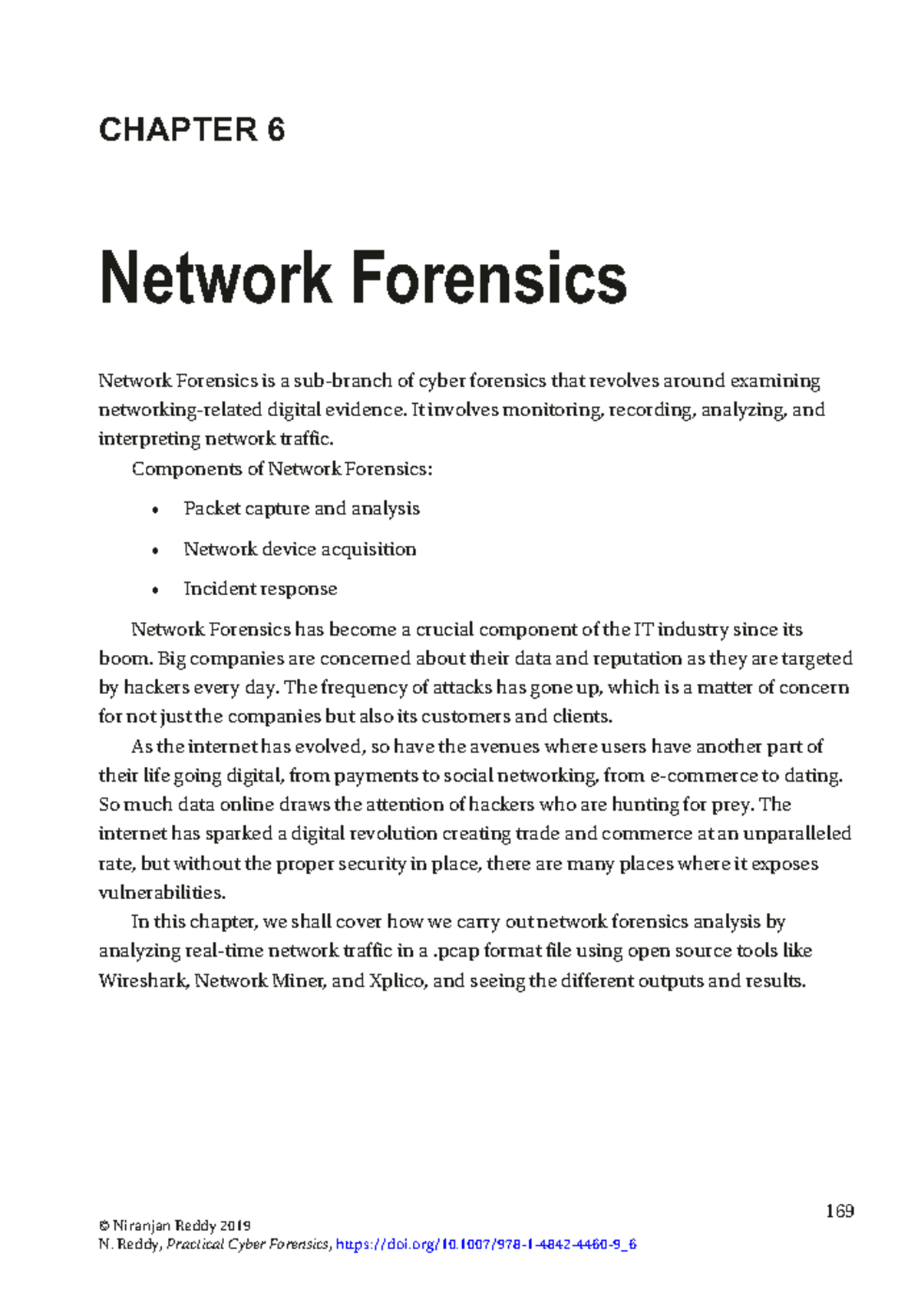
Chapter 11 Network Forensics Niranjan Reddy 2019 169 N Reddy Tool ecosystem and analysis workflow network forensics relies on a layered toolchain for capture, filtering, protocol dissection, and data extraction. the workflow progresses from raw packet capture to protocol specific analysis to decryption and reconstruction. Network forensics relies on specialized tools for capturing, analyzing, and investigating network data. these range from open source utilities to sophisticated commercial platforms, each with specific strengths and applications. In this blog post we explore nearly two dozen types of network forensics tools and techniques that cybersecurity professionals are using to aid in investigations. Learn how network forensic tools and network forensic analysis tools support network traffic forensics and cyber security investigations.

Mastering Network Forensics A Practical Approach To Investigating And In this blog post we explore nearly two dozen types of network forensics tools and techniques that cybersecurity professionals are using to aid in investigations. Learn how network forensic tools and network forensic analysis tools support network traffic forensics and cyber security investigations.
Network Forensics Pdf
Comments are closed.