Application Security Assessment Process

Sample Web Application Security Assessment Download Free Pdf Learn these 10 steps for a proactive application security assessment. prevent threats and identify vulnerabilities with earlier testing. In this article, we’ll walk through what an application security assessment involves, why it’s essential, the key steps to performing one effectively, and the role of aspm in transforming how organizations approach application security.

Mobile Application Security Assessments Is It Right For Your Business Strengthen security with our appsec risk assessment checklist. learn why assessments matter, core elements, step by step guidance, and mistakes. Here we’ve outlined each step of an effective security risk assessment checklist to get all of your bases covered. applications are composed of underlying services, code, and data, and are built and deployed along a software supply chain containing systems, infrastructure, pipelines and processes. Learn how to conduct a comprehensive application security risk assessment with this 8 step checklist. Application security assessment is a structured process to evaluate how well an application resists threats. the evaluation aims to identify, validate, and help remediate security weaknesses that could be exploited to compromise confidentiality, integrity, or availability.

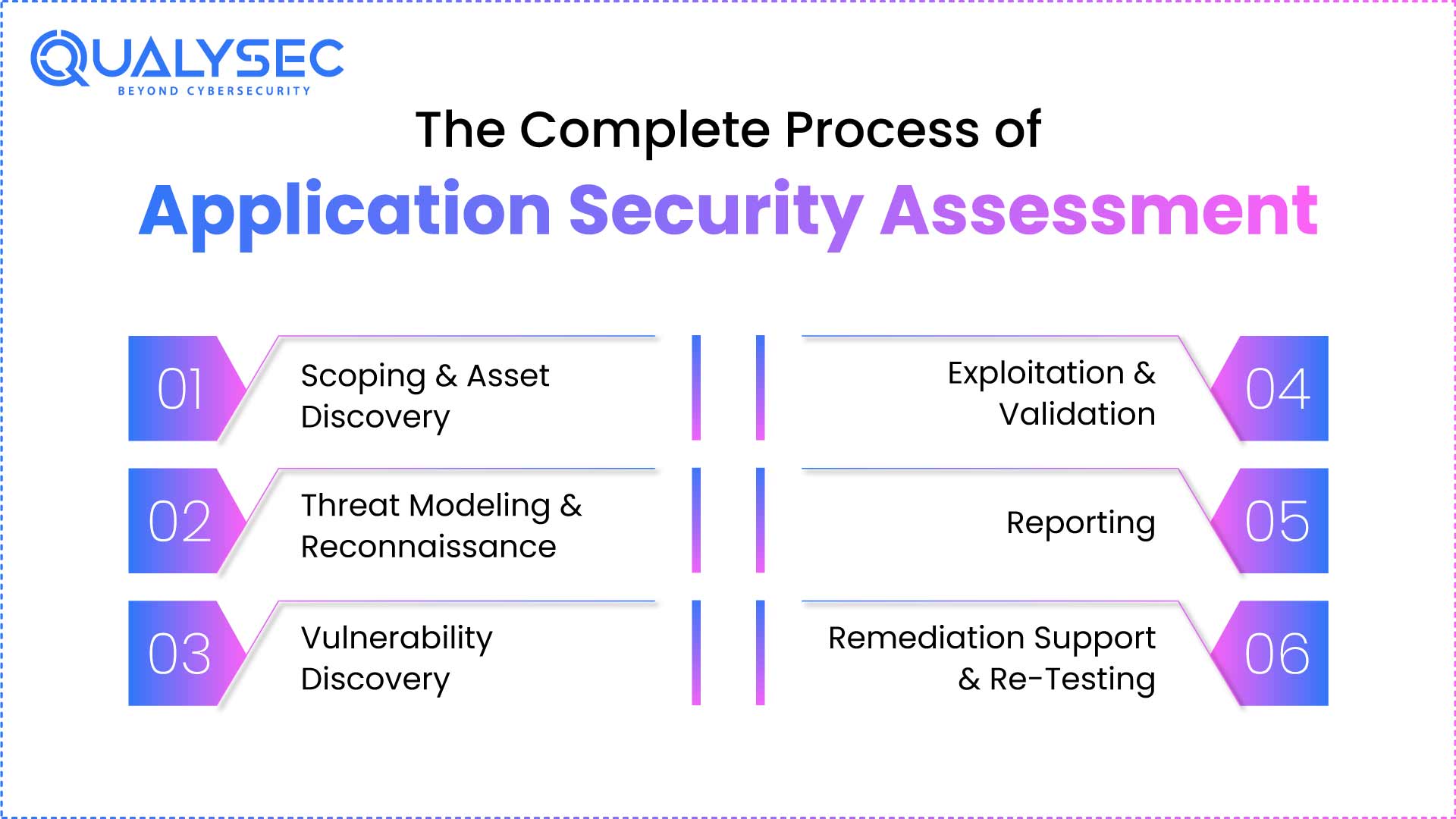
Process Phases For Application Security Assessment Ppt Presentation Learn how to conduct a comprehensive application security risk assessment with this 8 step checklist. Application security assessment is a structured process to evaluate how well an application resists threats. the evaluation aims to identify, validate, and help remediate security weaknesses that could be exploited to compromise confidentiality, integrity, or availability. Application security testing involves evaluating software applications to detect vulnerabilities and ensure compliance with security standards. this testing can be dynamically conducted at runtime or statically by examining the source code for weaknesses. This guide covers what an application security assessment actually is, the different types you should know about, why running them matters for your business (beyond just "our compliance team said so"), and how to pick the right tools. Fortinet cloud consulting services offers short and medium term steps to assess web applications by performing multiple application security testing scans at different stages of the software development life cycle. Evaluate your app’s security posture with a detailed application security assessment. discover how it works and why it’s essential for threat protection.
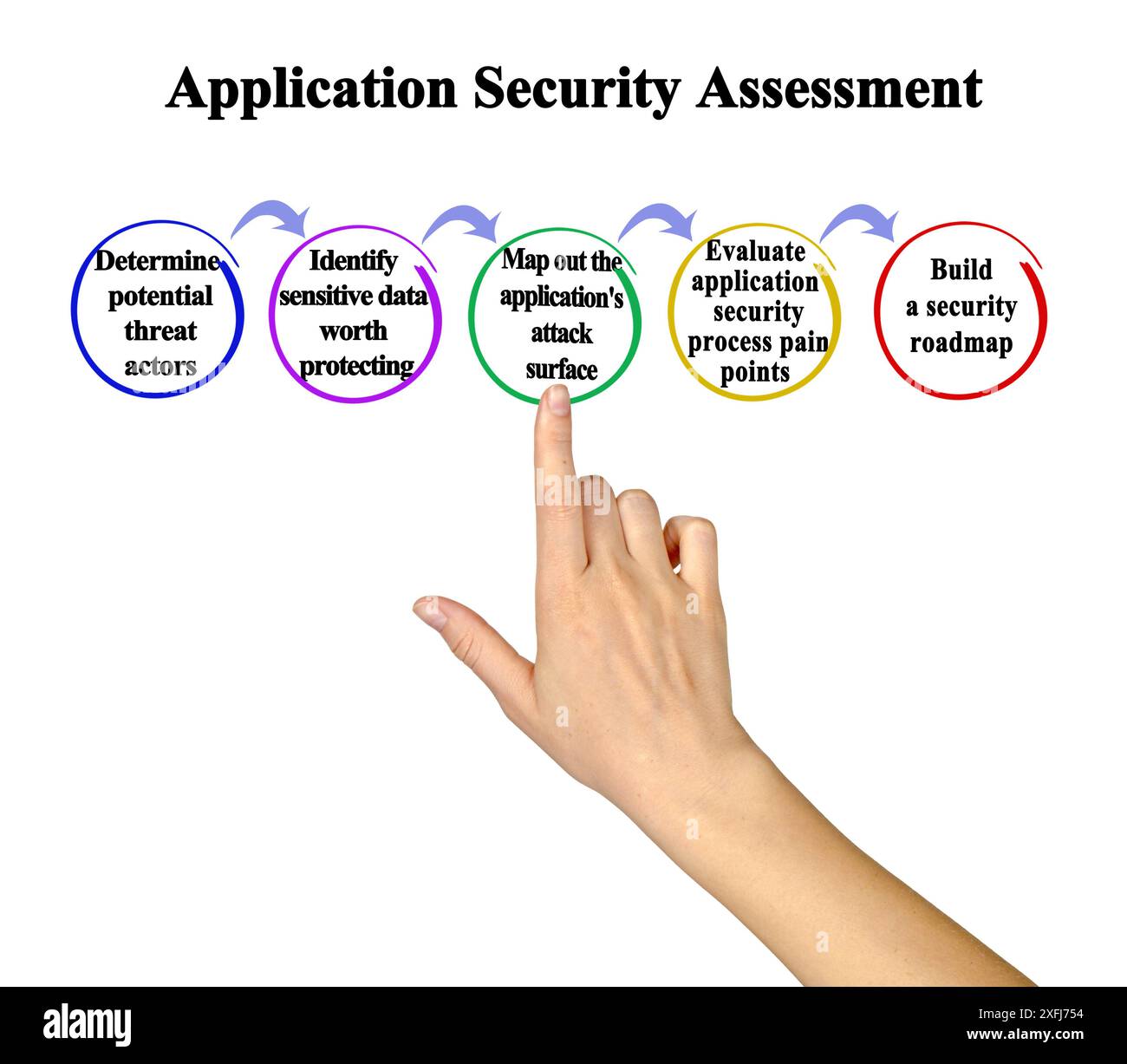
Processs Of Application Security Assessment Stock Photo Alamy Application security testing involves evaluating software applications to detect vulnerabilities and ensure compliance with security standards. this testing can be dynamically conducted at runtime or statically by examining the source code for weaknesses. This guide covers what an application security assessment actually is, the different types you should know about, why running them matters for your business (beyond just "our compliance team said so"), and how to pick the right tools. Fortinet cloud consulting services offers short and medium term steps to assess web applications by performing multiple application security testing scans at different stages of the software development life cycle. Evaluate your app’s security posture with a detailed application security assessment. discover how it works and why it’s essential for threat protection.

Cs Application Security Assessment Plurilock Fortinet cloud consulting services offers short and medium term steps to assess web applications by performing multiple application security testing scans at different stages of the software development life cycle. Evaluate your app’s security posture with a detailed application security assessment. discover how it works and why it’s essential for threat protection.
What Is An Application Security Assessment A Complete Guide
Comments are closed.