Apis Microservices Security Policy Secaware

Apis Microservices Security Policy Secaware This brief policy template concerns the secure design, development, testing, implementation, operation, management and maintenance of apis and microservices in order to protect data and systems from unauthorized access, use, disclosure, disruption, modification, or destruction. There are many security challenges that need to be addressed in the application design and implementation phases. the fundamental security requirements that have to be addressed during design phase are authentication and authorization.
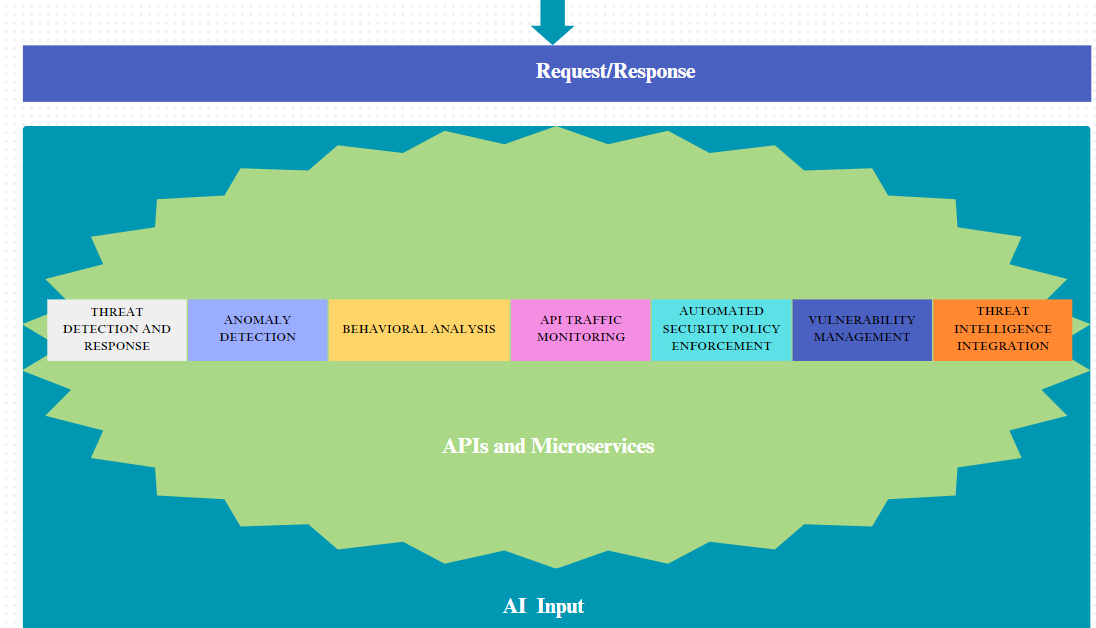
Ai To Bolster Cloud Security Apis Microservices We provide them as ms word documents that you can easily customise. get in touch for additional policies, procedures or guidelines, or if you need assistance to adapt them to your corporate style. buy them individually for $20 or take the whole lot for $399, saving over $1200. Securing apis in a microservices setup involves following essential principles that ensure safe communication and data integrity. here are the key pillars of api security: 1 . By implementing strong authentication and authorization practices, ensuring data protection through encryption, securing apis, and managing network and configuration settings effectively, organizations can create a robust defense against potential threats. Microservices architectures demand secure apis. learn how to protect api endpoints with authentication, encryption, zero trust, and automation in your devsecops strategy.
Dns Security Policy Secaware By implementing strong authentication and authorization practices, ensuring data protection through encryption, securing apis, and managing network and configuration settings effectively, organizations can create a robust defense against potential threats. Microservices architectures demand secure apis. learn how to protect api endpoints with authentication, encryption, zero trust, and automation in your devsecops strategy. These practices are essential for protecting data and maintaining a flexible, reliable, and secure microservices system. this article aims to be a resourceful guide, offering practical advice and strategies for devops teams. Uncover vital insights on how to address api security effectively within microservices architectures to protect your system's integrity and sensitive data. Microservices architecture relies heavily on apis for communication between services, making their security a critical concern. below are the tools and techniques to enhance api security in a microservices setup:. Learn how to secure your microservices architecture with robust api security strategies. protect your data and ensure compliance with best practices.
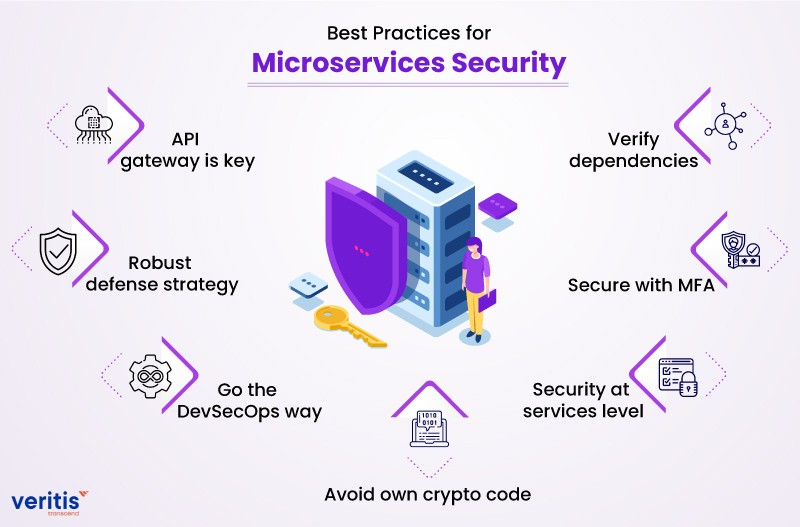
How To Manage Managing Security For Microservices Apis These practices are essential for protecting data and maintaining a flexible, reliable, and secure microservices system. this article aims to be a resourceful guide, offering practical advice and strategies for devops teams. Uncover vital insights on how to address api security effectively within microservices architectures to protect your system's integrity and sensitive data. Microservices architecture relies heavily on apis for communication between services, making their security a critical concern. below are the tools and techniques to enhance api security in a microservices setup:. Learn how to secure your microservices architecture with robust api security strategies. protect your data and ensure compliance with best practices.
Comments are closed.